An updated version of the MATA backdoor framework was spotted in attacks between August 2022 and May 2023, targeting oil and gas firms and the defense industry in Eastern Europe.
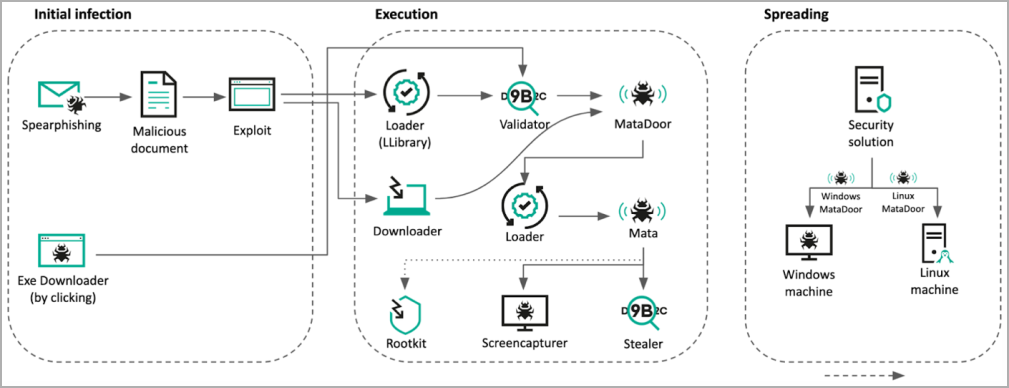
The attacks employed spear-phishing emails to trick targets into downloading malicious executables that exploit CVE-2021-26411 in Internet Explorer to initiate the infection chain.
The updated MATA framework combines a loader, a main trojan, and an infostealer to backdoor and gain persistence in targeted networks.
The MATA version in these attacks is similar to previous versions linked to the North Korean Lazarus hacking group but with updated capabilities.
Notably, spreading malware across all reachable corners of the corporate network occurs by breaching security compliance solutions and exploiting their flaws.
Abusing EDR in attacks
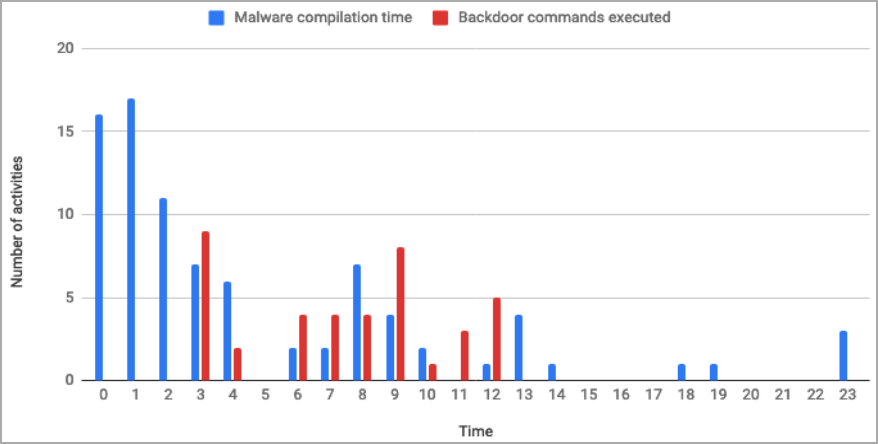
The cybersecurity company discovered the activity in September 2022 after examining two MATA samples communicating with command and control servers (C2) inside breached organization networks.
Further analysis revealed that the breached systems were financial software servers connected to numerous subsidiaries of the target organization.
The investigation revealed that the hackers had expanded their foothold from a single domain controller on a production plant to the entire corporate network.
The attack continued with the hackers accessing two security solution admin panels, one for endpoint protection and one for compliance checks.
The hackers abused the access to the security software admin panel to perform surveillance on the organization’s infrastructure and to disseminate malware to its subsidiaries.
Updated MATA malware
In applicable cases where the targets were Linux servers, the attackers employed a Linux variant of MATA in the form of an ELF file, which appears to be similar in functionality to the third generation of the Windows implant.
Kaspersky says it sampled three new versions of the MATA malware: one (v3) evolved from the second generation seen in past attacks, a second (v4) dubbed ‘MataDoor,’ and a third (v5) that was written from scratch.
The latest version of MATA comes in DLL form and features extensive remote control capabilities, supports multi-protocol (TCP, SSL, PSSL, PDTLS) connections to the control servers, and supports proxy (SOCKS4, SOCKS5, HTTP+web, HTTP+NTLM) server chains.
The 23 commands supported by MATA fifth generation include actions to set up connectivity, perform management of the implant, and retrieve information.
The most important commands supported by vanilla MATA are the following:
- 0x003: Connects to the C2 server using a specific command set.
- 0x001: Initiates a new client session that manages various commands from Buffer-box.
- 0x006: Schedules a reconnect with specific delays and queued commands.
- 0x007: Returns detailed system and malware information, encryption keys, plugin paths, etc.
- 0x00d: Configures vital settings like VictimID and connection parameters.
- 0x020: Initiates connection to C2 server and forwards traffic.
- 0x022: Probes active connection to given C2 servers and proxy list.
Additional plugins loaded onto the malware allow it to launch another 75 commands related to information gathering, process management, file management, network reconnaissance, proxy functionality, and remote shell execution.
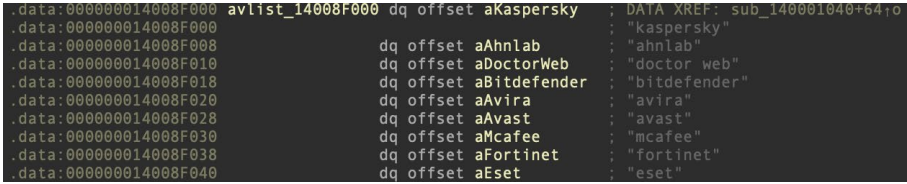
Other interesting findings include a new malware module that can leverage removable storage media such as USB to infect air-gapped systems, various stealers capable of capturing credentials, cookies, screenshots, and clipboard contents, and EDR/security bypass tools.
The researchers report that the hackers bypassed the EDR and security tools using a publicly available exploit for CVE-2021-40449, dubbed ‘CallbackHell.’
Employing this tool, the attackers alter kernel memory and target specific callback routines, which render endpoint security tools ineffective.
If that bypass method failed, they switched to previously documented Bring Your Own Vulnerable Driver (BYOVD) techniques.
Attribution unclear
Although Kaspersky previously associated MATA with the North Korean state-backed hacking group Lazarus, the cybersecurity firm has trouble associating the recently observed activity with high confidence.
Although there are still apparent links to Lazarus activity, the newer MATA variants and techniques such as TTLV serialization, multilayered protocols, and handshake mechanisms resemble more closely those of ‘Five Eyes’ APT groups like Purple, Magenta, and Green Lambert.
Also, the deployment of multiple malware frameworks and MATA framework versions in a single attack is very uncommon, indicating a particularly well-resourced threat actor.
For more technical information on MATA malware and the techniques used in the latest attacks, check out Kaspersky’s full report here.