Microsoft has significantly upgraded its Defender platform to automatically detect and block sophisticated cyberattacks targeting High-Value Assets (HVAs) like domain controllers and web servers.
By leveraging the new Microsoft Security Exposure Management tool, the system now uses context-aware intelligence to easily distinguish normal administrative tasks from malicious activities on critical network infrastructure.
As cyberattacks become increasingly targeted, hackers are consistently focusing on the core systems that keep enterprise businesses running smoothly.
Microsoft security researchers found that more than 78 percent of human-operated attack campaigns successfully compromise a critical asset, such as a domain controller, to gain elevated network access.
Traditional security tools often miss these dangerous intrusions because malicious activities using standard administrative utilities look identical to legitimate IT operations when viewed without proper context.
Context-Aware Asset Classification
To solve this ongoing visibility problem, Microsoft Defender now incorporates a critical asset framework powered by Microsoft Security Exposure Management.
This advanced technology automatically builds a comprehensive inventory of a company’s devices and cloud resources, tagging systems with predefined criticality levels based on their specific daily roles.
By understanding exactly which machines are High-Value Assets, defenders can apply stricter security rules to the specific environments where a potential network breach would cause the most damage.
The upgraded protection system relies on real-time intelligence from the cloud to continuously monitor and learn the normal operational baselines for each critical asset.
When Defender observes unexpected behaviors on Tier-0 systems that deviate from these established patterns, it elevates isolated weak signals into high-confidence security alerts.
This intelligent approach allows the endpoint protection platform to prioritise high-impact attacker tactics and proactively block threats before the blast radius expands across the network.
Domain controllers serve as prime targets for attackers looking to steal Active Directory databases and quickly acquire highly privileged domain administrator credentials.
Microsoft detailed a recent real-world scenario where an attacker used a scheduled task to extract the NTDS database, a stealthy move that normally blends in with standard system backup procedures.
Because Defender recognized the server’s critical role and the broader context of the attack path, it instantly blocked the database extraction and automatically disabled the compromised administrator account.
Stopping Stealthy IIS Webshells
Internet-facing systems like Exchange and SharePoint servers face constant scanning and dangerous exploitation attempts from advanced threat actors.
When Defender identifies a high-value asset running Internet Information Services, it automatically applies targeted technical inspections to commonly abused web application directories.
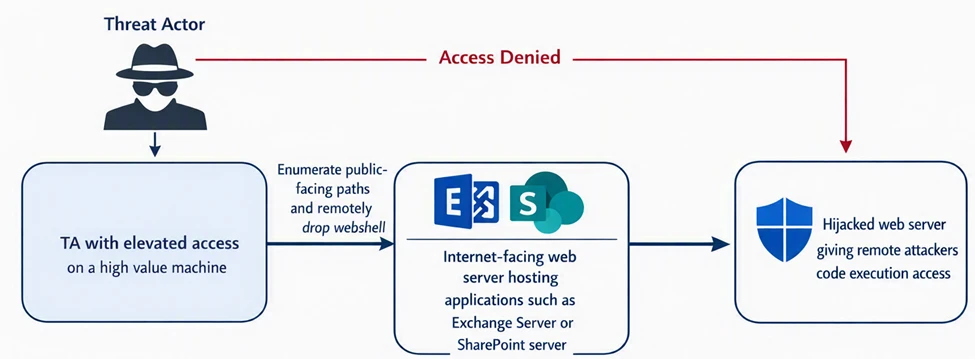
In recent forensic investigations, this context-aware scanning successfully detected and instantly remediated highly customized, previously unseen webshells that had quietly bypassed standard security perimeter filters.
Once hackers successfully establish a foothold inside a network, they frequently attempt to access sensitive credential stores remotely through directory replication methods or Entra Connect synchronization tools.
Microsoft explained that Defender now closely monitors suspicious file creations and unexpected data transfers involving sensitive registry hives or critical identity artifacts.
By carefully analyzing these process chains specifically on identity infrastructure servers, the platform effectively stops adversaries from exfiltrating the organization’s most critical operational passwords.
Cybersecurity teams must focus their initial defensive efforts on implementing vital posture recommendations specifically designed for high-value network assets.
Addressing security gaps on these critical systems delivers a significantly higher reduction in overall organizational risk compared to simply patching standard employee workstations.
Furthermore, accelerating the daily investigation and remediation of alerts originating from these core servers is absolutely essential to mitigating active threats quickly and severely limiting the potential impact of a modern data breach.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.