On March 2026 Patch Tuesday, Microsoft addressed 80+ vulnerabilities affecting its software and cloud services. Of these, two were publicly disclosed, but not actively exploited.
Privilege escalation vulnerabilities abound
The two publicly disclosed flaws are CVE-2026-21262, a vulnerability in SQL Server that may allow attackers to gain SQLAdmin privileges, and CVE-2026-26127, a .NET flaw that can be triggered for a denial of service attack.
The former is “less likely” to be exploited, and the latter “unlikely” to be exploited (according to Microsoft).
Six of the vulnerabilities patched are considered “more likely” to be exploited, and they can all be used by attackers to elevate their privileges (either to SYSTEM or admin) on targeted systems:
CVE-2026-24289 and CVE-2026-26132 are two use-after-free Windows Kernel flaws. CVE-2026-23668 is a race condition in the Windows Graphics Component.
“[CVE-2026-23668] was submitted to the ZDI program by Marcin Wiązowski as two separate bugs, and it demonstrates the need for variant investigations when creating security patches,” said Dustin Childs, head of threat awareness at Trend Micro’s Zero Day Initiative.
CVE-2026-24294 affects the Windows SMB Server and stems from improper authentication. CVE-2026-25187 is found in Winlogon, the Windows system process responsible for managing user authentication, secure logons/logoffs, and desktop security), and is caused by improper link resolution before file access.
CVE-2026-24291 affects Windows Accessibility Infrastructure (ATBroker.exe).
“This specific vulnerability is highly prized by threat actors because it offers a reliable transition from a limited user account to SYSTEM privileges. While many elevation flaws only grant Administrator status, gaining SYSTEM rights provides total control over the system and the ability to manipulate memory. This is the ultimate goal for any local attacker because it allows complete bypass of endpoint detection and response tools, which might otherwise block an Administrator but can’t easily stop a process running with the SYSTEM token,” said Ben McCarthy, lead cyber security engineer at Immersive.
He also noted that because this core accessibility component is present on nearly every modern Windows installation, “the potential attack surface is vast, making the rapid deployment of the official fix essential to maintaining perimeter integrity.”
Prioritize these patches
Childs singled out four more vulnerabilities as worthy of a quick patch:
- CVE-2026-23669, an authenticated remote code execution flaw in the Windows Print Spooler service
- CVE-2026-26144, a critical cross-site scripting (XSS) bug in Excel that could be exploited to cause the Copilot Agent to exfiltrate data off the target
- CVE-2026-26110 and CVE-2026-26113, two RCE flaws in Microsoft Office.
“Another month and another pair of Office bugs where the Preview Pane is an exploit vector. I’ve lost count of how many of these bugs have been patched over the last year, but it’s just a matter of time until they start appearing in active exploits,” he noted.
“The latest versions of Outlook allow you to hide the Preview Pane, but it isn’t clear if this would mitigate these attacks. The best option is still to test and deploy the update, but considering how many of these patches exist, it’s likely further updates will be needed to fully address these issues.”
Other critical bugs fixed were in a variety of cloud services: Microsoft ACI Confidential Containers, Microsoft Devices Pricing Program, and the Payment Orchestrator Service. These have been mitigated by Microsoft server-side, and users don’t have to do anything to be protected.
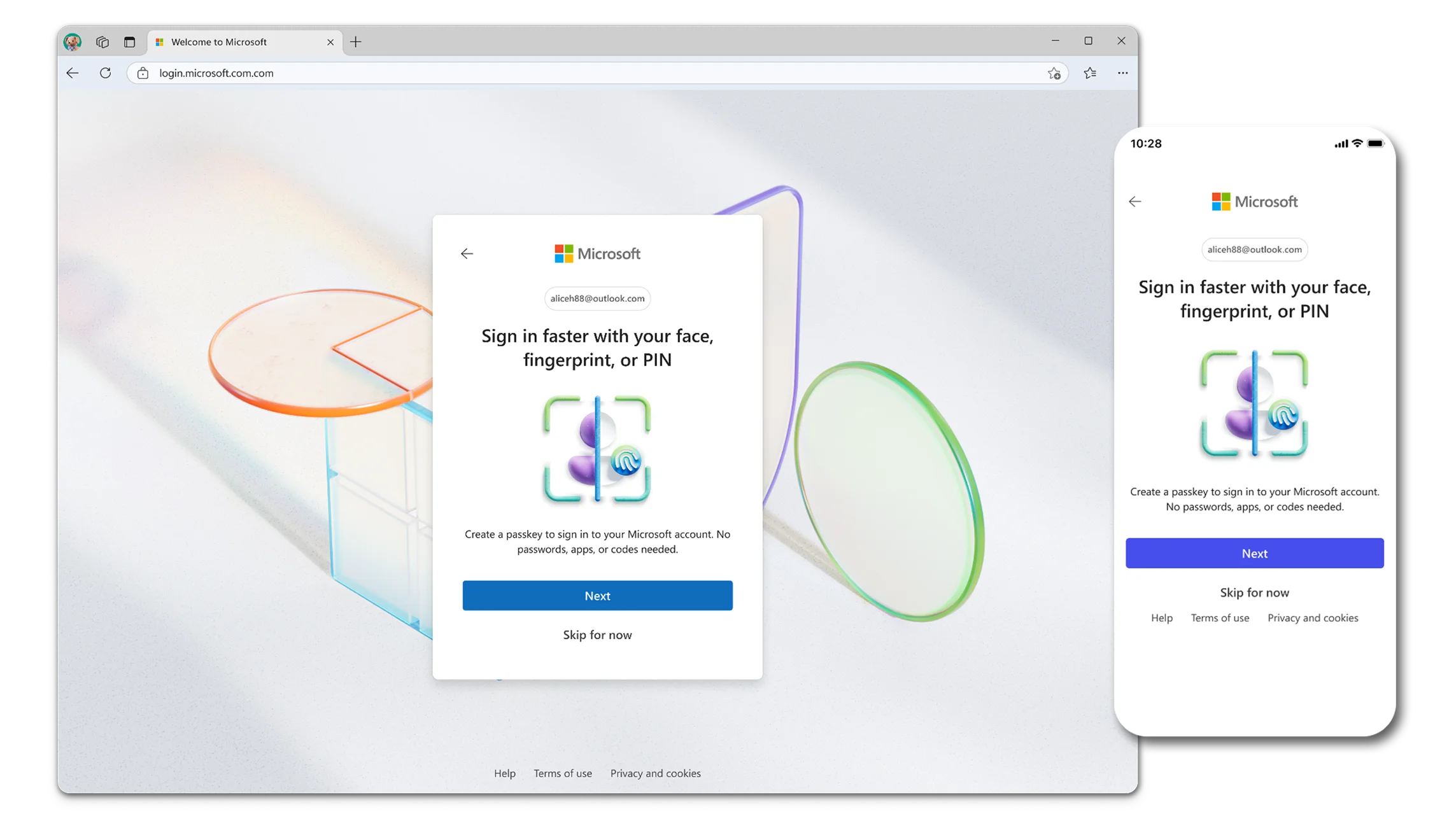
The Dutch National Cyber Security Center has also pointed out that CVE-2026-26123, which affects Microsoft Authenticator for Android and iOS, could be exploited by attackers via a rogue app to catch the victim’s sign-in in a Man-in-the-Middle attack.
“Because successful abuse depends on various steps and social engineering, large-scale abuse is not likely, but can be expected in targeted attacks by technically high-level actors,” they added.
“User interaction is required because the user must have a malicious application installed on their device and then accidentally select that application as the handler for the sign‑in deep link. This can occur when the user scans a QR code or taps a sign‑in link and chooses the malicious app instead of Microsoft Authenticator, causing the sign‑in flow to be handled by the attacker‑controlled app,” Microsoft explained the danger in the security advisory.
Adam Barnett, senior software engineer at Rapid7, noted that as users can choose the authenticator app they want to use, enterprise defenders “should consider how well their mobile device management policy covers app choice enforcement and patching for MFA apps.”
![]()
Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!
![]()