Microsoft has released the Windows 10 KB5082200 extended security update to fix the April 2026 Patch Tuesday vulnerabilities, including 2 zero-days.
This update brings some interesting changes, including new Remote Desktop Protocol file phishing protections and new Windows Security indicators that provide the status of the rollout of new Secure Boot certificates.
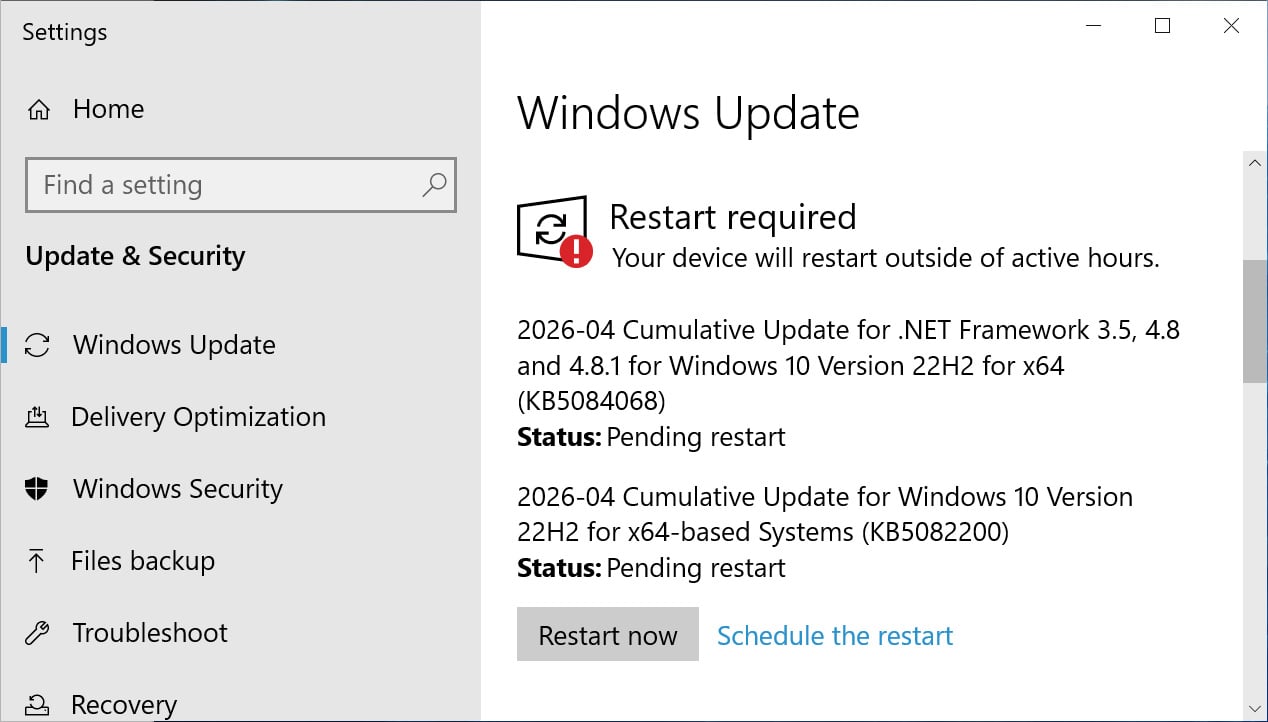
If you are running Windows 10 Enterprise LTSC or are enrolled in the ESU program, you can install this update like normal by going into Settings, clicking on Windows Update, and manually performing a ‘Check for Updates.’

Source: BleepingComputer
After installing this update, Windows 10 will be updated to build 19045.7184, and Windows 10 Enterprise LTSC 2021 will be updated to build 19044.7184.
What’s new in Windows 10 KB5082200
Microsoft is no longer releasing new features for Windows 10, and the KB5082200 update primarily contains security updates and bug fixes.
With today’s April 2026 Patch Tuesday, Microsoft has fixed 167 vulnerabilities, including two zero-day flaws.
The complete list of fixes is below:
- [Sign-In] Fixed: After you install the Windows update released on or after March 10, 2026, some users might experience an issue signing in to apps with a Microsoft account. Even when the device has a working Internet connection, a “no Internet” error appears during sign in and prevents access to Microsoft services and apps such as Microsoft Teams.
- [Remote Desktop] This update improves protection against phishing attacks that use Remote Desktop (.rdp) files. When you open an .rdp file, Remote Desktop shows all requested connection settings before it connects, with each setting turned off by default. A one-time security warning also appears the first time you open an .rdp file on a device. For more information, see Understanding security warnings when opening Remote Desktop (RDP) files.
- [Secure Boot]
- This update enables dynamic status reporting for Secure Boot states in the Windows Security App (Settings > Update & Security > Windows Security). Learn more about the status alerts via badges and notifications. Note that these enhancements are disabled by default on commercial devices and servers.
- This update fixes an issue that could cause a device to enter BitLocker Recovery after Secure Boot updates.
- With this update, Windows quality updates include additional high confidence device targeting data, increasing coverage of devices eligible to automatically receive new Secure Boot certificates. Devices receive the new certificates only after demonstrating sufficient successful update signals, maintaining a controlled and phased rollout.
As explained in the changelog above, this update fixes a longstanding issue that causes some Intel-based devices that support Connected Standby to enter the BitLocker recovery screen when restarted.
Microsoft is also continuing to roll out new Secure Boot certificates to replace older 2011 certificates that expire in June 2026. With this update, Windows users can go into Windows Security to check the status of this rollout.
Microsoft states that there are no known issues with this update.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.







