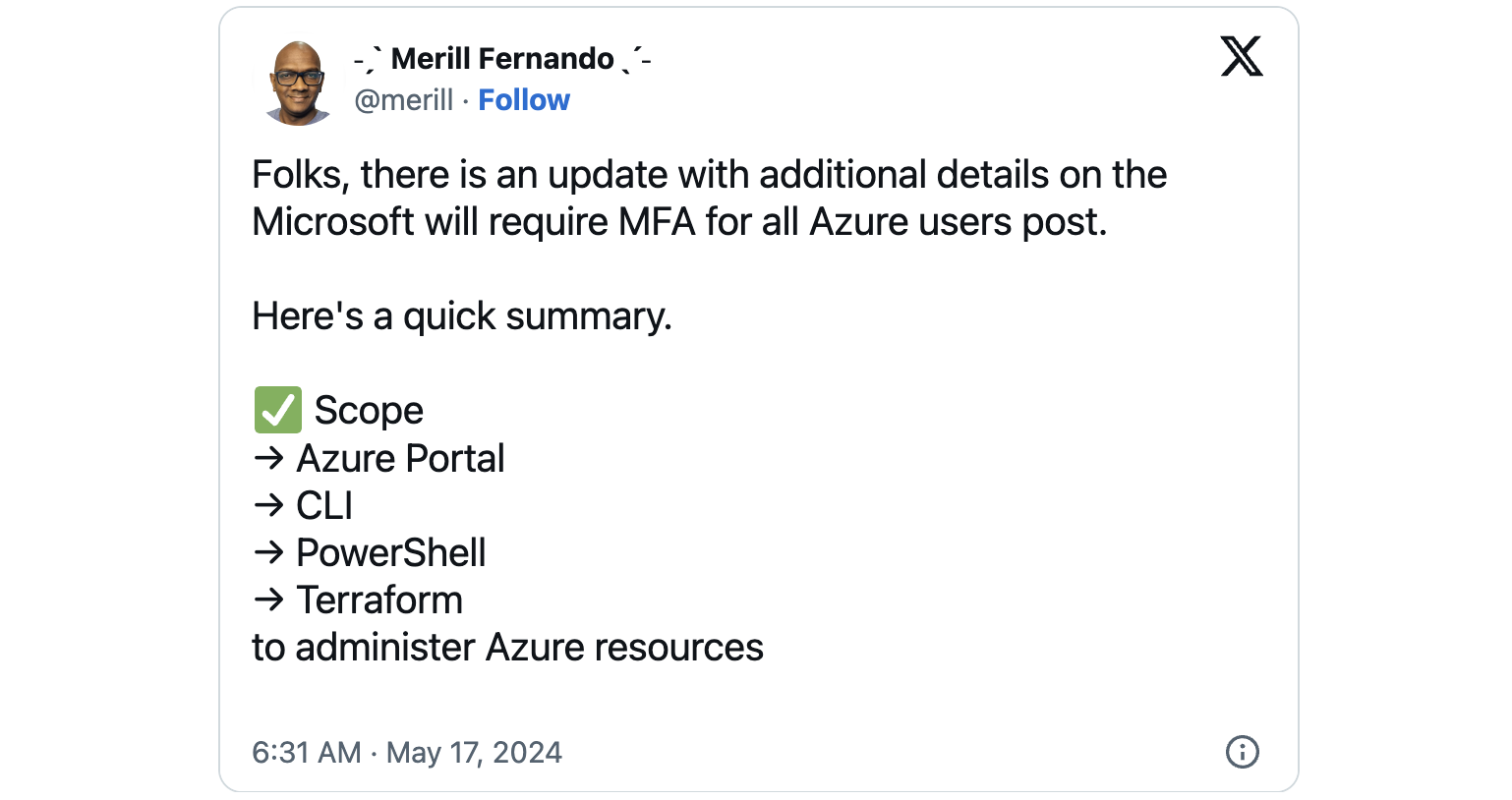
Starting in July, Microsoft will begin gradually enforcing multi-factor authentication (MFA) for all users signing into Azure to administer resources.
After first completing the rollout for the Azure portal, the MFA enforcement will see a similar rollout for CLI, PowerShell, and Terraform.
Redmond says customers will also receive additional information via email and official notifications before the MFA enforcement.
“Service principals, managed identities, workload identities, and similar token-based accounts used for automation are excluded. Microsoft is still gathering customer input for certain scenarios such as break-glass accounts and other special recovery processes,” explained Azure product manager Naj Shahid.
“Students, guest users and other end-users will only be affected if they are signing into Azure portal, CLI, PowerShell or Terraform to administer Azure resources. This enforcement policy does not extend to apps, websites or services hosted on Azure. The authentication policy for those will still be controlled by the app, website or service owners.”
Microsoft also urged admins to enable MFA in their tenants before the rollout using the MFA wizard for Microsoft Entra. They can also monitor which users have registered for MFA using the authentication methods registration report and this PowerShell script to get a report of the MFA state across the entire user base.
According to a Microsoft study focused on analyzing the security performance of MFA methods across a large dataset of Azure Active Directory users exhibiting suspicious activity, MFA offers a big boost of protection for user accounts against cyberattacks, with over 99.99% of all MFA-enabled accounts resisting hacking attempts.
As the company’s analysts further found, MFA also reduces the risk of compromise by 98.56%, even when the attackers attempted to breach accounts using stolen credentials.
This comes after Redmond announced in November that it would soon roll out Conditional Access policies requiring MFA for all admins when signing into Microsoft admin portals (e.g., Entra, Microsoft 365, Exchange, and Azure), for users on all cloud apps, and for high-risk sign-ins (the latter option is only available for Microsoft Entra ID Premium Plan 2 customers).
“Our goal is 100 percent multi-factor authentication. Given that formal studies show multi-factor authentication reduces the risk of account takeover by over 99 percent, every user who authenticates should do so with modern strong authentication,” Weinert said at the time.
As part of the same move to boost MFA adoption, Microsoft-owned GitHub also requires all active developers to enable two-factor authentication (2FA) beginning January 2024.







