The professional and personal online spheres are merging as social media platforms like Facebook, LinkedIn, and WhatsApp are now commonly used for work communication. Their integration creates cybersecurity vulnerabilities.
Threat actors can target employees on social media using their accounts accessed from work devices.
These accounts act as attack vectors, allowing unauthorized access to the organization’s systems.
A new LinkedIn threat combines breached users’ accounts and an evasive 2-step phishing attack.
A recent Python-based infostealer called Snake targets Facebook users with malicious messages.
By tricking users into downloading malware, Snake steals sensitive browsing data to hijack accounts.
It highlights how social media is a potential attack vector for stealing credentials and compromising corporate systems.
LinkedIn is a social media platform for professional networking that is vulnerable to attacks due to the abundance of publicly available user data.
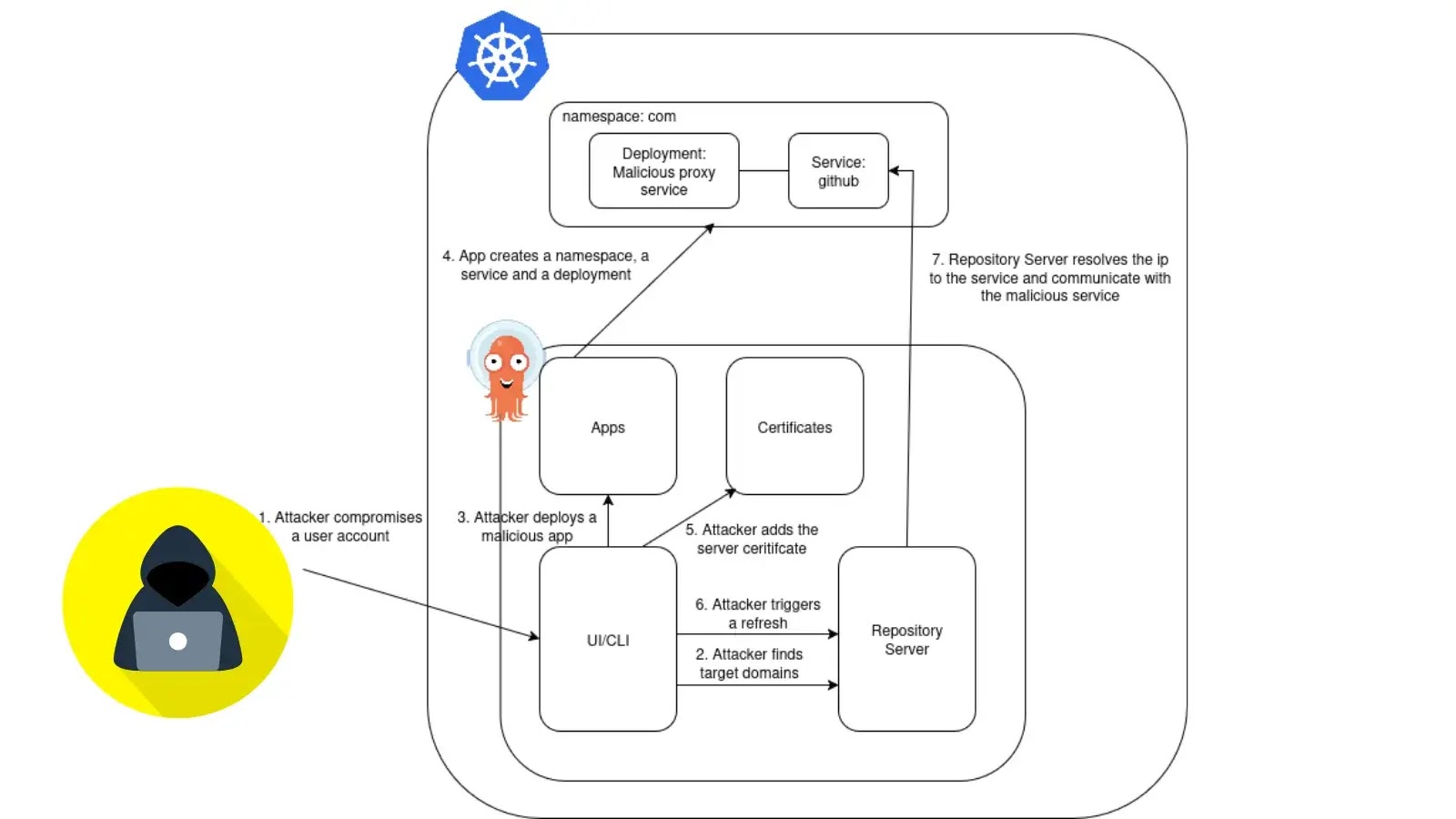
Attackers can harvest email addresses for surveys and use fake profiles to deliver malware through phishing attacks. Perception Point recently discovered a new attack that combines compromised user accounts with a 2-step phishing scheme to bypass detection.
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Try Trustifi Free Threat Scan with Sophisticated AI-Powered Email Protection .
Compromised LinkedIn accounts had been exploited to launch social engineering attacks. The attackers sent messages to the victim’s network, pretending to be a trusted connection (1st degree).
The messages contain a malicious link disguised as a legitimate OneDrive document link, often using the lure of a confidential project to trick the victim into clicking it, leading to an account takeover.
Phishing actors utilize a two-step attack. First, they trick victims into clicking a URL that leads to a legitimate OneDrive page hosting a malicious Word document.
Free Webinarfor DIFR/SOC Teams: Securing the Top 3 SME Cyber Attack Vectors - Register for Free
Second, the document embeds a URL redirecting victims through a fake Cloudflare verification prompt before landing on a phishing webpage designed to steal Microsoft 365 credentials.
The phishing page’s HTML code reveals it originates from a group called “3rr0r Hun73r” that creates and sells phishing kits.
Social media’s popularity creates a vulnerability for enterprises where hackers exploit employees’ social media use within work browsers to steal personal and corporate data.
Secure your emails in a heartbeat! Take our free 30-second assessment and get matched with your ideal email security vendor.