- CVE-2026-21262, CVE-2026-26115 and CVE-2026-26116 | SQL Server Elevation of Privilege Vulnerability
- CVE-2026-26127 |.NET Denial of Service Vulnerability
- CVE-2026-24287, CVE-2026-24289 and CVE-2026-26132 | Windows Kernel Elevation of Privilege Vulnerability
- CVE-2026-26118 | Azure MCP Server Tools Elevation of Privilege Vulnerability
- CVE-2026-26110 and CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability
- Tenable Solutions
- Get more information
- 8Critical
- 75Important
- 0Moderate
- 0Low
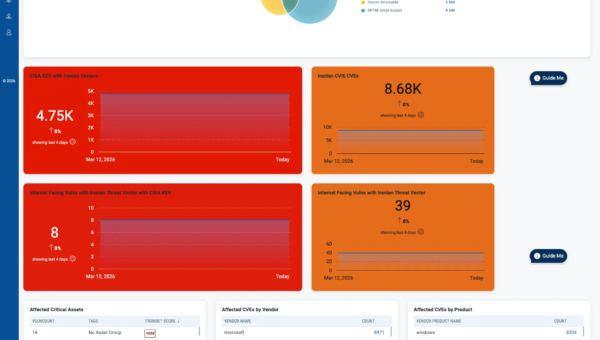
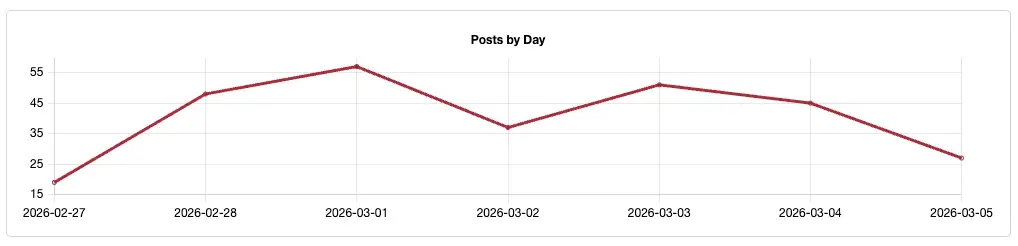
Microsoft addresses 83 CVEs including two vulnerabilities that were publicly disclosed prior to a patch being released.
Microsoft patched 83 CVEs in its March 2026 Patch Tuesday release, with eight rated critical and 75 rated as important. Our counts omitted one CVE (CVE-2026-26030) assigned by GitHub.
This month’s update includes patches for:
- .NET
- ASP.NET Core
- Active Directory Domain Services
- Azure Arc
- Azure Compute Gallery
- Azure Entra ID
- Azure IoT Explorer
- Azure Linux Virtual Machines
- Azure MCP Server
- Azure Portal Windows Admin Center
- Azure Windows Virtual Machine Agent
- Broadcast DVR
- Connected Devices Platform Service (Cdpsvc)
- Microsoft Authenticator
- Microsoft Brokering File System
- Microsoft Devices Pricing Program
- Microsoft Graphics Component
- Microsoft Office
- Microsoft Office Excel
- Microsoft Office SharePoint
- Payment Orchestrator Service
- Push Message Routing Service
- Role: Windows Hyper-V
- SQL Server
- System Center Operations Manager
- Windows Accessibility Infrastructure (ATBroker.exe)
- Windows Ancillary Function Driver for WinSock
- Windows App Installer
- Windows Authentication Methods
- Windows Bluetooth RFCOM Protocol Driver
- Windows DWM Core Library
- Windows Device Association Service
- Windows Extensible File Allocation
- Windows File Server
- Windows GDI
- Windows GDI+
- Windows Kerberos
- Windows Kernel
- Windows MapUrlToZone
- Windows Mobile Broadband
- Windows NTFS
- Windows Performance Counters
- Windows Print Spooler Components
- Windows Projected File System
- Windows Resilient File System (ReFS)
- Windows Routing and Remote Access Service (RRAS)
- Windows SMB Server
- Windows Shell Link Processing
- Windows System Image Manager
- Windows Telephony Service
- Windows Universal Disk Format File System Driver (UDFS)
- Windows Win32K
- Winlogon

Elevation of privilege (EoP) vulnerabilities accounted for 55.4% of the vulnerabilities patched this month, followed by remote code execution (RCE)vulnerabilities at 20.5%.
CVE-2026-21262, CVE-2026-26115 and CVE-2026-26116 | SQL Server Elevation of Privilege Vulnerability
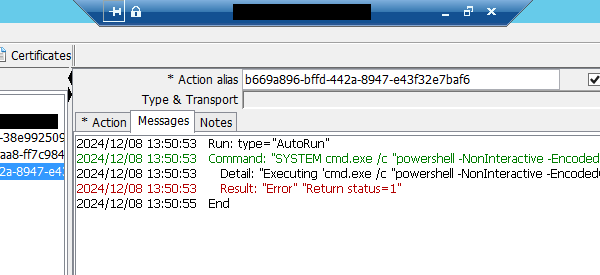
CVE-2026-21262, CVE-2026-26115 and CVE-2026-26116 are EoP vulnerabilities affecting Microsoft SQL Server. Each of these flaws received a CVSSv3 score of 8.8 and were rated as important. While each of these were assessed as “Exploitation Less Likely” according to Microsoft’s Exploitability Index, CVE-2026-21262 was publicly disclosed as a zero-day. While no exploitation has been reported by Microsoft, a successful exploit of any one of these three flaws would result in an attacker gaining SQL sysadmin privileges.
CVE-2026-26127 |.NET Denial of Service Vulnerability
CVE-2026-26127 is a denial of service (DoS) vulnerability affecting.NET 9.0 and 10.0 on Windows, Mac OS and Linux. It received a CVSSv3 score of 7.5 and was rated as important. According to Microsoft, this vulnerability was publicly disclosed prior to patches being made available. Although it was publicly disclosed, Microsoft assesses that exploitation is unlikely for this DoS vulnerability.
.NET updates this month also include patches to address CVE-2026-26131, an important severity EoP vulnerability for.NET 10 installations on Linux.
CVE-2026-24287, CVE-2026-24289 and CVE-2026-26132 | Windows Kernel Elevation of Privilege Vulnerability
CVE-2026-24287, CVE-2026-24289 and CVE-2026-26132 are EoP vulnerabilities in the Windows Kernel. Each was assigned CVSSv3 scores of 7.8 and rated important. A local, authenticated attacker could exploit these vulnerabilities in order to gain SYSTEM privileges. While Microsoft reports no evidence of exploitation, it did assess CVE-2026-24289 and CVE-2026-26132 as “Exploitation More Likely.” Including these three CVEs, six EoPs affecting Windows Kernel have been patched so far in 2026.
CVE-2026-26118 | Azure MCP Server Tools Elevation of Privilege Vulnerability
CVE-2026-26118 is an EoP vulnerability in Azure Model Context Protocol (MCP) Server. An attacker could exploit this vulnerability by sending a crafted input to a vulnerable Azure MCP Server that accepts user-provided parameters. Successful exploitation would grant an attacker to elevate privileges using an obtained managed identity token.
MCP, an open standard introduced in 2024 by Anthropic, is used to allow large language models (LLMs) to connect to external data and tools. For more information on MCP, please check out our FAQ blog on Model Context Protocol (MCP) and Integrating with AI for Agentic Applications as well Tenable Research’s AI Security blog examining web flaws in MCP servers.
CVE-2026-26110 and CVE-2026-26113 | Microsoft Office Remote Code Execution Vulnerability
CVE-2026-26110 and CVE-2026-26113 are RCE vulnerabilities affecting Microsoft Office. Both received CVSSv3 scores of 8.4 and were rated as critical. A local, unauthenticated attacker could exploit these vulnerabilities to achieve local code execution. Microsoft notes that the preview pane is an attack vector for these flaws and both CVEs were assessed as “Exploitation Less Likely.”
Tenable Solutions
A list of all the plugins released for Microsoft’s March 2026 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
For more specific guidance on best practices for vulnerability assessments, please refer to our blog post on How to Perform Efficient Vulnerability Assessments with Tenable.
Get more information
- Microsoft’s March 2026 Security Updates
- Tenable plugins for Microsoft March 2026 Patch Tuesday Security Updates
Join Tenable’s Research Special Operations (RSO) Team on Tenable Connect for further discussions on the latest cyber threats.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.