Hackers are impersonating popular secure messaging apps to deploy a sophisticated Android spyware tool called ProSpy against journalists, activists, and political figures across the Middle East, in a hack‑for‑hire campaign linked to the BITTER APT group.
The campaign has been active since at least 2022. It primarily targets civil society members and potentially government officials in countries such as Egypt, Lebanon, Bahrain, the UAE, Saudi Arabia, and the wider MENA region.
Attackers typically start by approaching a target on platforms like LinkedIn, messaging apps, or email, then pressure them into clicking a malicious link under the pretext of a video call, document share, or urgent account alert.
According to joint research by Access Now, Lookout, and SMEX, the operation relies on persistent social engineering and tailored spearphishing, often delivered through fake social media accounts and messaging profiles that pose as journalists, support staff, or trusted contacts.
Those links either lead to credential‑phishing pages imitating services like iCloud, Office 365, or webmail or to fake download pages that quietly deliver ProSpy to Android devices as an APK.
Secure Messaging Apps
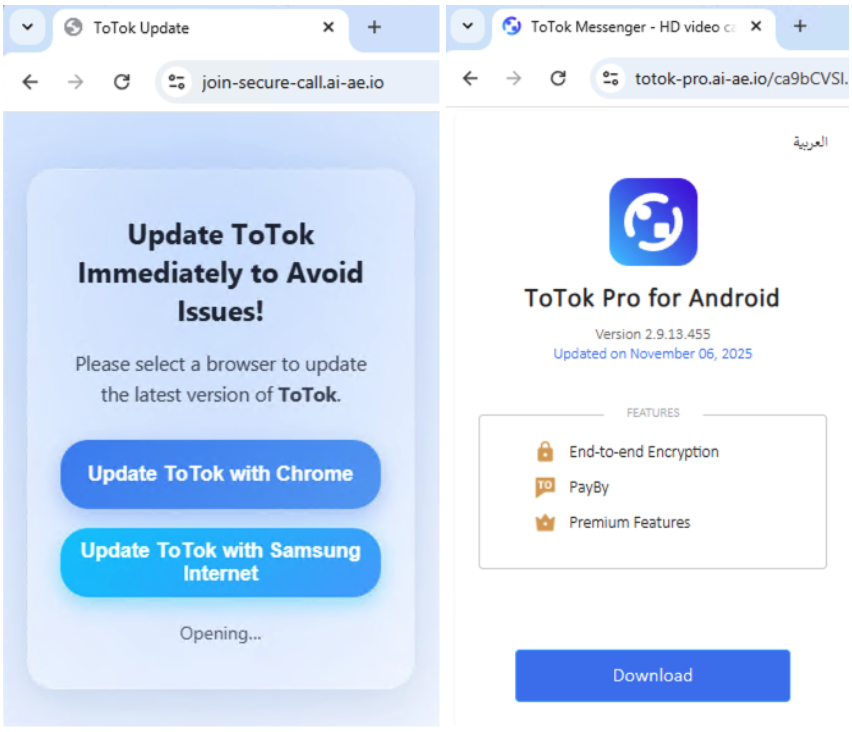
ProSpy is an Android spyware family written in Kotlin that pretends to be secure or “pro” versions of trusted communication tools, including Signal, ToTok, and Botim.
Attackers set up simple, single‑page “official‑looking” websites for these apps that automatically deliver malicious APKs with names such as “ToTok Pro,” “Botim Pro,” or “Signal Encryption Plugin.”
These sites are hosted on deceptive domains like totok‑pro[.]ai‑ae[.]io or botim‑app[.]pro, sometimes in both English and Arabic, and often uses random‑looking PHP paths to hide the real distribution server and evade basic scanning.
Once the victim installs the fake app from outside the official store, ProSpy gains broad permissions and blends in as a normal messaging client or plugin.
After installation, ProSpy turns the device into a surveillance sensor, exfiltrating contacts, SMS messages, call‑related data, device information, and a wide range of local files, including documents, images, audio, video, archives, and even chat backups.
It uses a modular “worker” design to handle tasks like scanning for recently modified files, searching for backup files (such as ToTok backup archives), and uploading stolen content to command‑and‑control (C2) servers.
Archive MIME types are common archive file formats such as zip, rar, tar, 7z and jar, apk and json files.
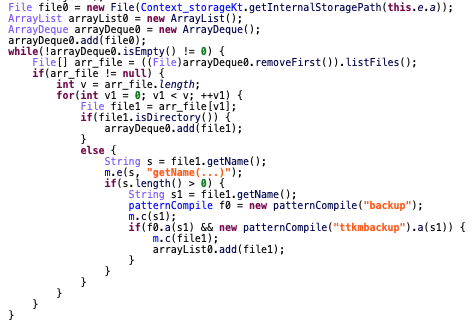
Communication with C2 infrastructure is implemented via REST‑style endpoints, often under paths like “/v3/images” or “/v3/videos,” and the malware regularly polls a “getType”‑style endpoint for numbered commands that trigger specific collection jobs.
Researchers have identified multiple C2 and staging domains such as sg nlapp[.]info, totok‑pro[.]io, and treasuresland[.]cc used to host malicious payloads and receive exfiltrated data.
Links to BITTER APT and Hack‑for‑Hire
Lookout’s analysis connects this campaign to the South Asia–based BITTER APT group, known for long‑running espionage operations aligned with regional intelligence interests.
Infrastructure overlaps, similar worker‑class design, numbered C2 commands, and shared use of secure‑messaging lures echo earlier BITTER‑linked Android malware such as Dracarys.
However, the focus on civil society and opposition politicians in the Middle East, rather than only government and strategic sectors, suggests the activity is part of a hack‑for‑hire model, where BITTER or closely linked operators are contracted to run bespoke spying jobs.
Researchers currently assess this attribution with moderate confidence and note that the case highlights how relatively simple social‑engineering chains, combined with custom Android spyware, remain highly effective against even security‑aware targets.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.