Mirai-based botnets have evolved from simple IoT malware into large-scale DDoS and proxy abuse platforms that now underpin record-breaking attacks and stealthy cybercrime operations.
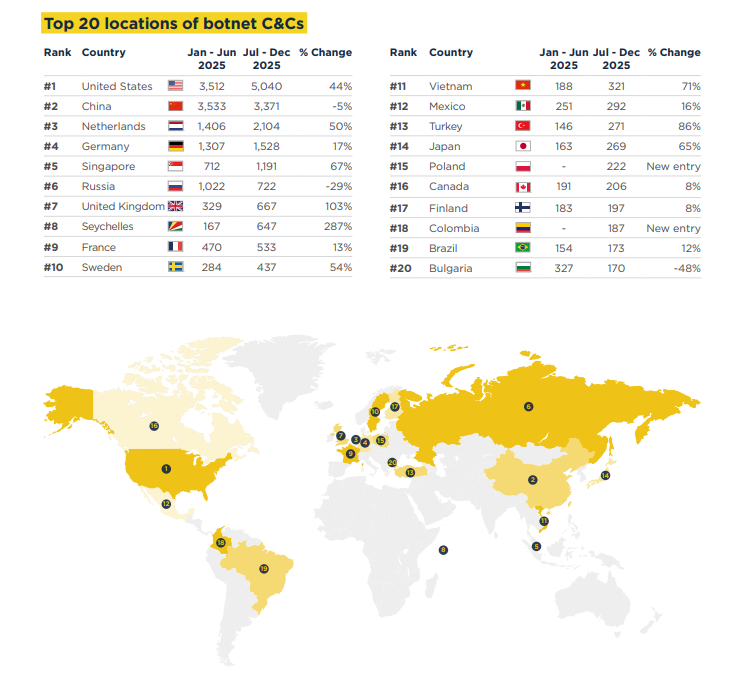
In total, over 21,000 C2 servers were observed between July and December 2025, with a notable shift towards abusing bots as residential proxies in addition to classic DDoS use.
This growth coincided with ever larger DDoS campaigns; Cloudflare’s Q4 2025 data highlights a series of “hyper‑volumetric” attacks, including a 31.4 Tbps incident attributed to the Aisuru‑Kimwolf botnet family.
Spamhaus reports that botnet command-and-control (C2) activity grew by 26% in early 2025 and a further 24% in the second half of the year, reversing 18 months of relative stability.
Mirai as the base framework
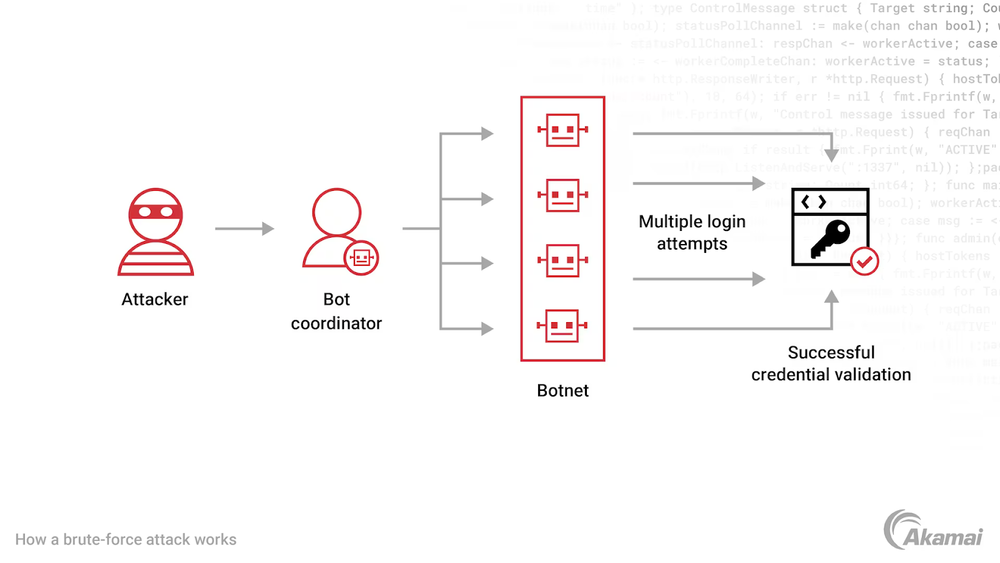
Mirai, first seen in 2016, targets internet‑connected devices running lightweight Linux and typically protected only by default or weak credentials.
Once compromised, these IoT systems are enrolled into a botnet that can perform high‑volume UDP, TCP, and application‑layer floods against chosen targets.
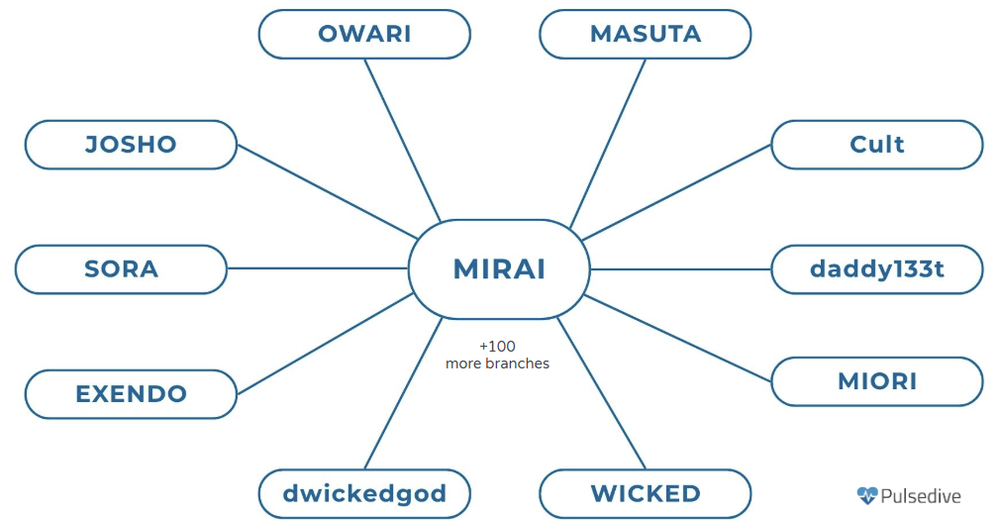
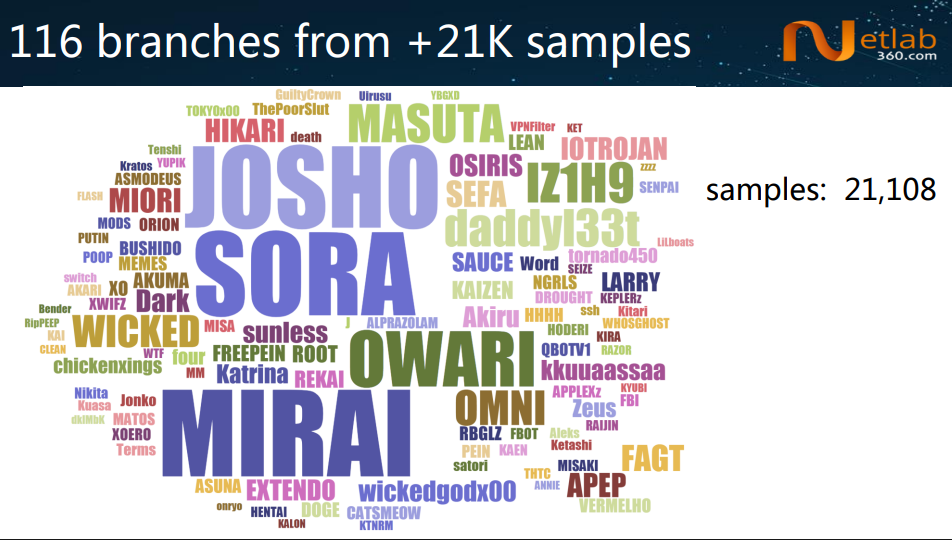
Public release of Mirai’s source code sparked an explosion of variants and “branches,” many of which add new exploits, CPU architectures, and evasion features while preserving the core scanning and DDoS logic.
Satori is one of the best‑known Mirai derivatives and was first detected in late 2017. It quickly infected hundreds of thousands of home and small‑office routers by weaponizing remote code execution flaws, such as command‑injection bugs in D‑Link DSL devices, and then deploying installation scripts that drop architecture‑specific binaries for broad coverage.
These scripts automate downloading, permission changes, and execution so that once a router is reachable, it can usually be folded into the botnet with no user interaction.
Aisuru-Kimwolf: DDoS and proxy abuse
More recently, the Aisuru and Kimwolf families have pushed Mirai‑style botnets into a dual role: extreme‑scale DDoS engines and rentable residential proxy networks.
Cloudflare and multiple security researchers link Aisuru‑Kimwolf to the 31.4 Tbps attack and to floods measured in tens of billions of packets per second, often using randomized packet characteristics to evade simple filtering.
Parallel reporting shows Kimwolf, an Android‑focused Aisuru variant, abusing residential proxy providers such as IPIDEA to reach internal networks, infect smart TVs and mobile devices, and then resell that access for fraud, credential‑stuffing, and other abuse via underground channels.
Authorities have started pushing back at scale: U.S. disruption efforts have targeted IoT DDoS botnets’ C2 infrastructure, while Google and partners moved to disrupt domains and accounts used to market and control abused residential proxy pools.
Despite these efforts, Mirai‑based ecosystems remain resilient, thanks to unpatched routers, insecure Android devices, and constantly recycled infrastructure that lets operators rebuild quickly after takedowns.
For defenders, this means prioritizing basic hygiene on edge devices, monitoring for unusual outbound traffic patterns, and tracking Mirai‑derived indicators remains essential as these botnets continue to grow in both DDoS power and proxy abuse capabilities.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.