A new Android banking trojan called Mirax is rapidly gaining traction in the cybercrime ecosystem, combining powerful remote access features with residential proxy capabilities to turn victims’ smartphones into high-value infrastructure nodes.
Mirax is marketed as a premium Android RAT and banking malware, offering attackers full, real‑time control over compromised devices.
Once installed, the malware can execute commands, navigate the user interface via Accessibility Services, capture the screen, and monitor user activity without visible signs.
It also deploys highly dynamic HTML and JavaScript overlays, fetched on demand from its command‑and‑control (C2) server, and rendered on top of legitimate banking and crypto apps to harvest credentials, PINs and one‑time passwords.
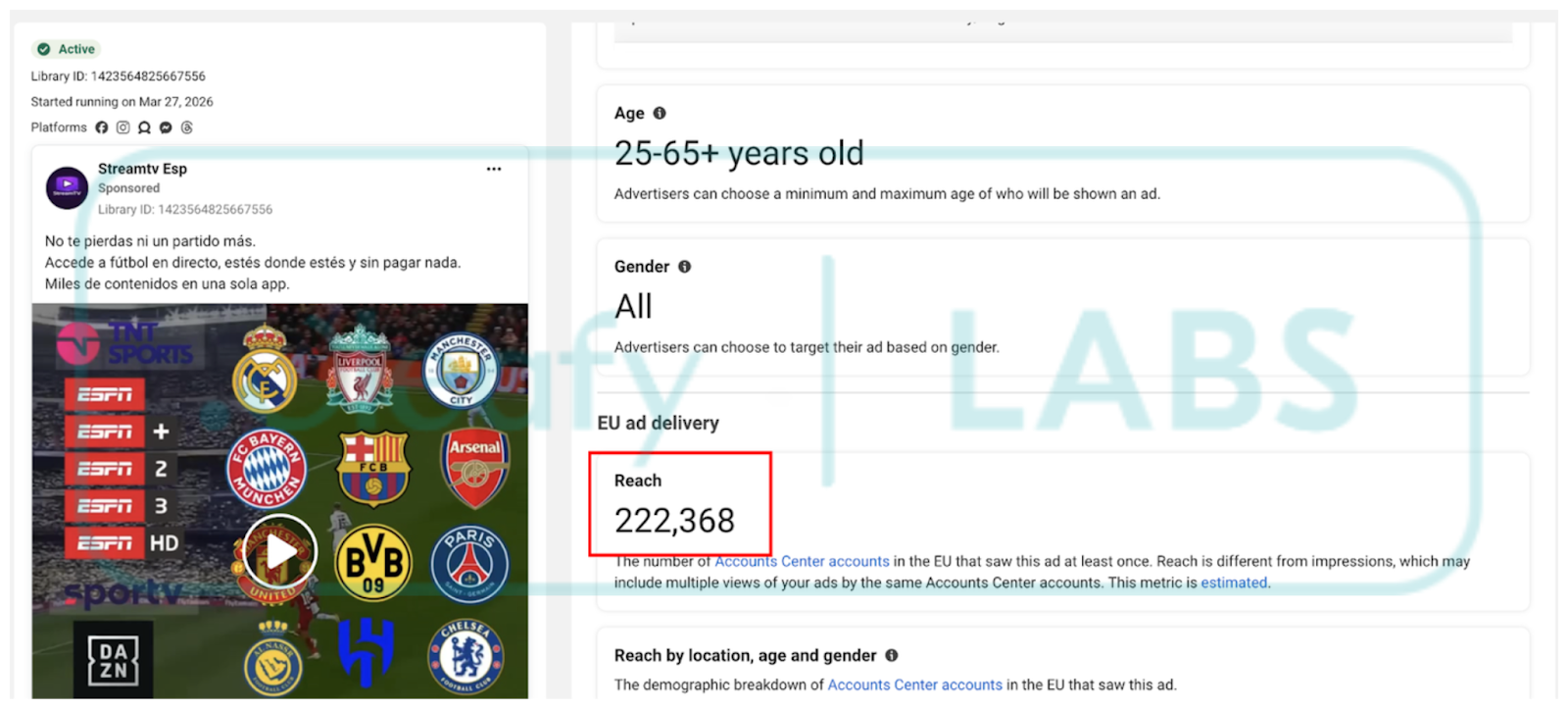
Recent campaigns monitored by Cleafy have focused on Spanish‑speaking users in Europe, reaching more than 200,000 accounts through malicious Meta ads served on Facebook, Instagram, Messenger, and Threads.
First promoted in underground forums in December 2025, Mirax is sold under a tightly controlled Malware-as-a-Service (MaaS) model and is currently used by a small circle of trusted, mostly Russian‑speaking affiliates.
The developers operate Mirax as a “private MaaS,” restricting access to vetted clients and offering tiered subscription plans, including full and “light” variants with different feature sets.
This commercial structure mirrors enterprise software, with ongoing feature development and documentation that details builder options, packers and deployment workflows.
Advanced Surveillance And Keyguard
Beyond overlays, Mirax includes comprehensive spyware modules. It continuously logs keystrokes across applications, enabling attackers to capture usernames, passwords and other sensitive input entered anywhere on the device.
The malware also exfiltrates detailed information about the device’s lock screen configuration, including PIN length, unlock pattern characteristics and the use of biometric methods such as fingerprint or face unlock.
These capabilities support follow‑on fraud: attackers can use keylogged data and keyguard insights to defeat banking app protections, reset accounts or socially engineer victims during support calls.
When combined with live remote access and screen‑viewing, Mirax enables near‑complete takeover of a victim’s mobile banking environment.
Mirax’s standout feature is its built‑in SOCKS5 residential proxy module, which effectively repurposes infected phones as proxy endpoints.
Using SOCKS5 together with Yamux multiplexing over WebSocket, the malware establishes persistent, multiplexed tunnels that route attacker traffic through the victim’s real IP address.
This allows operators to bypass geolocation controls, blend into normal user traffic and evade fraud detection systems that rely on IP reputation and device fingerprinting.
Cleafy’s analysis notes that Mirax maintains separate WebSocket channels for command control, data exfiltration and the proxy tunnel, typically on ports 8443 (/control), 8444 (/data) and 8445 (/tunnel).
Even if the RAT fails to obtain all high‑risk permissions, the proxy component can still function in the background, letting criminals retain value from partially compromised devices by using them as exit nodes for activities such as account takeovers, password spraying, or broader network abuse.
Malvertising and GitHub Abuse
Current Mirax campaigns rely heavily on Meta Ads to drive traffic to phishing pages that impersonate IPTV or illegal sports streaming services, a lure tailored to users already accustomed to sideloading Android apps.
These landing pages perform strict checks to ensure they are being accessed from mobile devices, helping the operators evade automated crawlers and security scanners.
The initial APK functions as a dropper, hosted and continuously updated via GitHub Releases, where attackers push new samples to existing release entries to hinder automated sample collection and hash‑based detection.
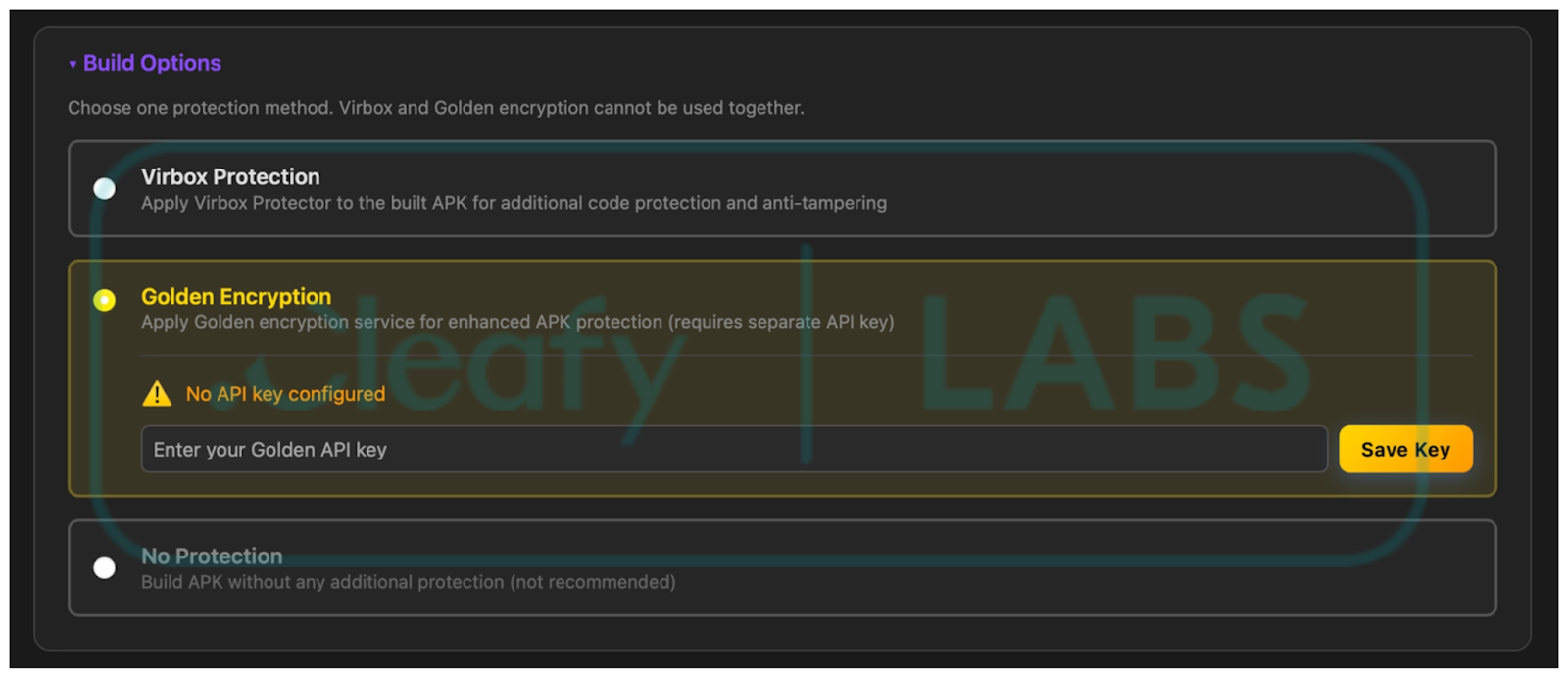
The dropper hides the real payload inside encrypted .dex files buried deep in the app’s assets, using RC4 and XOR‑based decryption routines and commercial packers such as Golden Encryption (GoldCrypt) to resist static analysis.
After unpacking, the final implant masquerades as a video player, requests Accessibility privileges, and then runs in the background while showing fake error pages and black overlays to obscure its activity.
Mirax illustrates how Android banking trojans are evolving from simple credential stealers into multi‑purpose platforms that fuse RAT, spyware and residential proxy capabilities in a single tool.
By abusing trusted platforms such as Meta’s ad network and GitHub, and by embedding proxy functionality directly into a full‑featured RAT, Mirax gives attackers new ways to monetize each infection and to weaponize everyday smartphones as both targets and infrastructure.
Security teams are urged to tighten mobile threat defenses, monitor for anomalous proxy‑like traffic from devices, and educate users about the heightened risks of sideloading apps from links in social media advertisements, especially those offering free IPTV, streaming or “cracked” services.
IOCs
| SHA 256 | Name | Package | Description |
|---|---|---|---|
| 53de68ebec281e7233bffc52199b22ec2dba 463eec3b29d4c399838e18daecbf | StreamTV | org.lgvvfj.pluscqpuj | Dropper |
| 88e6e4a5478a3ee7bfdfc5e7614ae6f3f121 e0d470741a9cc84a111fe9b266db | Reproductor de video | org.yjeiwd.plusdc71 | Malware |
| 759eed82699b86b6a792a63ccc76c2fa5ed 71720b89132abdead9753f5d7bd11 | StreamTV | org.dawme.secure5ny | Dropper |
| 29577570d18409d93fa2517198354716740 b19699eb5392bfaa265f2f6b91896 | Reproductor de video | org.azgaw.managergst1d | Malware |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.





