A sophisticated spear-phishing campaign, dubbed Operation GriefLure, targeting senior executives in Vietnam and the Philippines with a stealthy modular remote access trojan (RAT).
The campaign focuses on high-value organizations, including Viettel Group Vietnam’s largest military-backed telecom provider and St. Luke’s Medical Center (SLMC) in the Philippines, demonstrating a calculated approach to regional cyber-espionage.
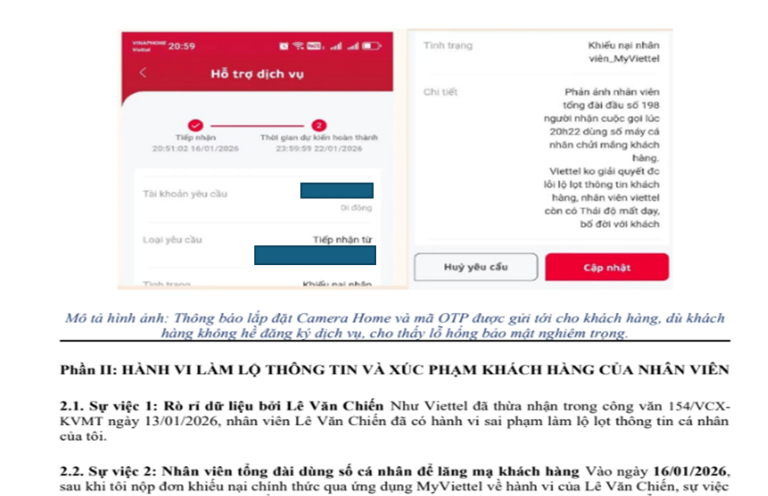
What sets Operation GriefLure apart is its use of deeply convincing decoy content. In the Vietnam-focused campaign, attackers embedded eight genuine legal and investigative documents tied to a real data breach dispute involving Viettel.
These included police reports, internal emails, and signed corporate admissions, making the lure nearly indistinguishable from legitimate case material.
In contrast, the Philippines campaign used a fabricated whistleblower complaint accusing SLMC of financial fraud and compliance violations.
The document was carefully crafted to trigger urgency among healthcare administrators by referencing regulatory risks, including potential violations tied to PhilHealth and JCI accreditation.
Seqrite Labs has uncovered a targeted spear phishing campaign dubbed Operation GriefLure, which targeted at senior executives of Viettel Group.
The attack begins with a spear-phishing email delivering a compressed archive containing decoy PDFs and a malicious Windows shortcut (LNK) file.
This LNK abuses the legitimate Windows ftp.exe utility as a Living-off-the-Land (LotL) tool, allowing attackers to evade traditional endpoint detection.
Once executed, the malware silently reconstructs its payload using fragmented files disguised as .doc documents.
Within seconds, a malicious executable named sfsvc.exe is assembled and launched while a decoy PDF opens to distract the victim. The entire process completes in under 10 seconds with no visible indicators.
Modular RAT Campaign
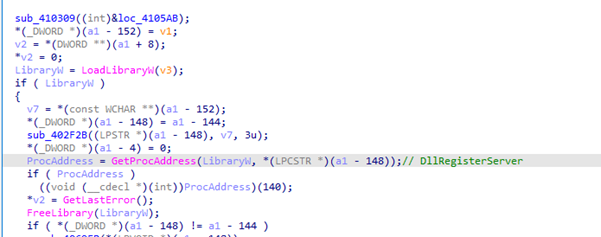
At the core of the attack is a modular malware framework. The sfsvc.exe binary acts as a custom loader, executing a secondary DLL payload (360.dll) that functions as a multi-stage shellcode loader. This design enables fileless execution, process injection, and persistence.
The primary decoy document a formal legal escalation email written directly to Viettel’s CEO summarizing a 4-month data breach dispute and threatening for legal action against the corporation.
Once active, the RAT communicates with a command-and-control (C2) server using obfuscated HTTP requests. It supports a wide range of surveillance and data theft capabilities, including:
- Credential harvesting from browsers, FTP clients, and remote access tools.
- Screenshot capture with dynamic resolution adjustment.
- Process enumeration and system profiling.
- Directory listing and file metadata exfiltration.
- Chunked payload delivery and remote execution.
For example, the malware can scan Chrome’s stored login data, capture screenshots of sensitive applications, and upload them to a remote server disguised as a legitimate domain.
The malware employs advanced evasion strategies, including DLL sideloading, XOR-based payload obfuscation, and NTFS Alternate Data Streams to hide malicious files.
It also includes functionality to detect installed security software and adapt its behavior accordingly.
A notable feature is its ability to terminate and relaunch the Windows Explorer process under controlled conditions, effectively manipulating the user environment to maintain persistence and reduce visibility.
Operation GriefLure highlights the evolution of targeted phishing campaigns, where attackers blend authentic documents with advanced malware delivery techniques.
Analysis of the campaign infrastructure revealed the use of a suspicious domain, whatsappcenter[.]com, hosted on a Hong Kong-based provider known for bulletproof hosting.
The malware also contains indicators such as targeting of WeChat data and references to China-based security software, suggesting a China-linked threat actor with moderate-to-high confidence.
By combining social engineering precision with modular, fileless malware, threat actors can achieve rapid and covert compromise of high-profile targets.
Security teams should monitor for unusual use of native tools such as ftp.exe, inspect compressed attachments carefully, and deploy behavioral detection mechanisms that can identify fileless execution patterns.
IOCs
| File Name | SHA256 |
|---|---|
| HỒ SƠ BẰNG CHỨNG GHI NHẬN CHUỖI HÀNH VI VI PHẠM PHÁP LUẬT… .lnk | 35af2cf5494181920b8624c7b719d39590e2a5ff5eaa1a2fa1ba86b2b5aa9b43 |
| Whistleblowing_Report_SLMC_Fraud_and_Misconduct_2026.pdf.lnk | bc090d75f51c293d916c40d4b21094faaec191a42d97448c92d264875bf1f17b |
| Valid_Government_Identification_Card_of_Dela_Cruz_Juan_… .png.lnk | 197f11a7b0003aa7da58a3302cfa2a96a670de91d39ddebc7a51ac1d9404a7e6 |
| iPad_Pro_Display_Spec_Final_CONFIDENTIAL.docx.lnk | f34f550147c2792c1ff2a003d15be89e5573f0896c5aa6126068baa4621ef416 |
| 360.8.dll | bc83817c6d2bf8df1d58eac946a12b5e2566b2ffe15cf96f37c711c4b755512b |
| th5znehec.exe | 61e9d76f07334843df561fe4bac449fb6fdaed5e5eb91480bded225f3d265c5f |
| a.dll | ee6330870087f66a237a7f7c115b65beb042299f12eae1e9004e016686d0c387 |
| SlULIRDJOiq | 91a15554ec9e49c00c5ca301f276bd79d346968651d54204743a08a3ca8a5067 |
| Batch | a49155df50963d2412534090bbd967749268bd013881ddb81d78b87f91cdc15b |
| Batch | 7f80add94ee8107a79c87a9b4ccbd33e39eccd1596748a5b88629dd6ac11b86d |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.