A threat group resembling MuddyWater has conducted a large-scale reconnaissance and intrusion operation targeting critical sectors in the Middle East, including aviation, energy, and government entities.
The attackers reportedly scanned over 12,000 internet-facing systems before launching selective exploitation attempts that led to the confirmed theft of sensitive data.
The incident followed a structured, multi-phase workflow, beginning with mass vulnerability scanning and ending in confirmed data exfiltration.
According to Oasis Security, the attackers weaponized at least five newly disclosed CVEs to identify exploitable systems across web applications, email servers, and workflow automation platforms.
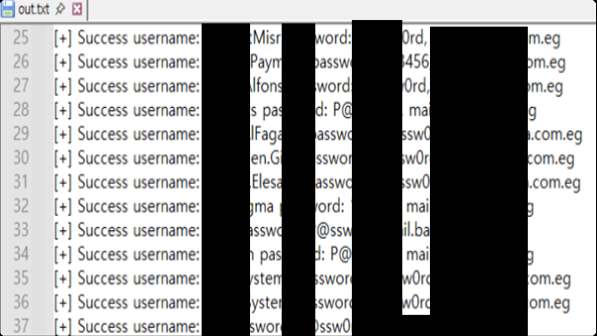
Following the broad reconnaissance, the group carried out brute-force attacks against Outlook Web Access (OWA) using custom scripts like owa.py and multi-threaded tools such as Patator.
These credential-based intrusions proved critical to the campaign’s second stage, giving the actor persistent access to compromised networks.
The tcp_serv.py controller listens on port 5009 and accepts inbound connections from compromised systems, while udp_3.0.py operates as a UDP-based controller with similar communication structures.
tcp_serv.py) using a custom header structure (Source : Oasis). Targets included organizations in Egypt, Israel, and the United Arab Emirates, with several confirmed credentials and account lists recovered from attacker-controlled servers.
Advanced C2 Infrastructure Revealed
Technical analysis of adversary infrastructure uncovered an elaborate Command and Control (C2) framework hosted on IP address 157.20.182.49 in the Netherlands.
Investigators found evidence of multiple modular C2 controllers written in Python and Go, handling communications over TCP, HTTP, and UDP channels.
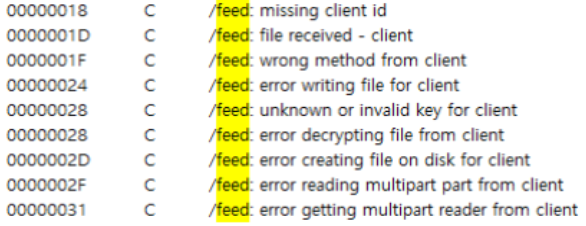
/feed endpoint of ex-server (Source : Oasis).Key properties included:
- AES (CTR-mode) encrypted communication over HTTP endpoints like /command and /feed.
- Cookie-based client identifiers manage active session control.
- Custom binary header structures, such as
, observed across multiple controller types.
Some C2 controllers, such as tcp_serv.py and udp_3.0.py, accepted inbound traffic from infected systems, while Go-based binaries like ex-server managed encrypted data and operational tasking.
These designs closely mirror MuddyWater previous tradecraft, especially infrastructure patterns linked to the ArenaC2 framework.
Exploited Vulnerabilities
The threat actor exploited five key vulnerabilities across varied platforms:
- CVE-2025-54068 (Laravel Livewire RCE) – Targeting web-based apps.
- CVE-2025-52691 (SmarterMail RCE) – Exploiting email servers.
- CVE-2025-68613 (n8n RCE) – Targeting workflow automation tools.
- CVE-2025-9316 (Session ID flaw) – Impacting remote management systems.
- CVE-2025-34291 (Langflow RCE) – Affecting AI workflow frameworks.
While the initial scans were widespread, subsequent exploitation showed regional focus, prioritizing Middle Eastern aviation and energy sectors.
Oasis researchers confirmed data theft from an Egyptian aviation company, including passport and visa records, payroll data, credit card information, and corporate documents about 200 files in total.
Investigators note that the campaign began in early February, shortly before tensions escalated in the Middle East.
Oasis Security warns that the operation exemplifies a shifting threat landscape, where automated reconnaissance, credential theft, lateral movement, and exfiltration are integrated into continuous, strategic pipelines.
The tight operational structure, multi-stage workflow, and shared technical indicators suggest potential alignment with MuddyWater-linked cyber activity often attributed to Iranian state interests.
The group’s resource-efficient methods and C2 modularity highlight a refined evolution of state-aligned cyber tactics targeting critical regional infrastructure.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.