The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday warned that multiple nation-state actors are exploiting security flaws in Fortinet FortiOS SSL-VPN and Zoho ManageEngine ServiceDesk Plus to gain unauthorized access and establish persistence on compromised systems.
“Nation-state advanced persistent threat (APT) actors exploited CVE-2022-47966 to gain unauthorized access to a public-facing application (Zoho ManageEngine ServiceDesk Plus), establish persistence, and move laterally through the network,” according to a joint alert published by the agency, alongside Federal Bureau of Investigation (FBI), and Cyber National Mission Force (CNMF).
The identities of the threat groups behind the attacks have not been disclosed, although the U.S. Cyber Command (USCYBERCOM) hinted at the involvement of Iranian nation-state crews.
The findings are based on an incident response engagement conducted by CISA at nn unnamed aeronautical sector organization from February to April 2023. There is evidence to suggest that the malicious activity commenced as early as January 18, 2023.
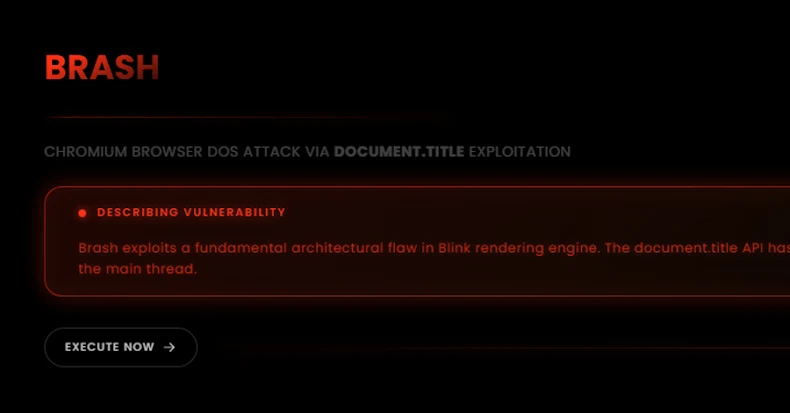
CVE-2022-47966 refers to a critical remote code execution flaw that allows an unauthenticated attacker to completely take over susceptible instances.

Following the successful exploitation of CVE-2022-47966, the threat actors obtained root-level access to the web server and took steps to download additional malware, enumerate the network, collect administrative user credentials, and move laterally through the network.
It’s not immediately clear if any proprietary information was stolen as a result.
The entity in question is also said to have been breached using a second initial access vector that entailed the exploitation of CVE-2022-42475, a severe bug in Fortinet FortiOS SSL-VPN, to access the firewall.
“It was identified that APT actors compromised and used disabled, legitimate administrative account credentials from a previously hired contractor—of which the organization confirmed the user had been disabled prior to the observed activity,” CISA said.
The attackers have also been observed initiating multiple Transport Layer Security (TLS)-encrypted sessions to multiple IP addresses, indicating data transfer from the firewall device, in addition to leveraging valid credentials to hop from the firewall to a web server and deploy web shells for backdoor access.
In both instances, the adversaries are said to have disabled administrative account credentials and deleted logs from several critical servers in the environment in an attempt to erase the forensic trail of their activities.
Way Too Vulnerable: Uncovering the State of the Identity Attack Surface
Achieved MFA? PAM? Service account protection? Find out how well-equipped your organization truly is against identity threats
Supercharge Your Skills
“Between early-February and mid-March 2023, anydesk.exe was observed on three hosts,” CISA noted. “APT actors compromised one host and moved laterally to install the executable on the remaining two.”
It’s currently not known how AnyDesk was installed on each machine. Another technique used in the attacks entailed the use of the legitimate ConnectWise ScreenConnect client to download and run the credential dumping tool Mimikatz.
What’s more, the actors attempted to exploit a known Apache Log4j vulnerability (CVE-2021-44228 or Log4Shell) in the ServiceDesk system for initial access but were ultimately unsuccessful.
In light of the continued exploitation of security flaws, it’s recommended that organizations apply the latest updates, monitor for unauthorized use of remote access software, and purge unnecessary accounts and groups to prevent their abuse.