Urgent Alert: NetScaler bug CVE-2026-3055 probed by attackers could leak sensitive data

Attackers are actively probing a critical Citrix NetScaler flaw (CVE-2026-3055) that can leak sensitive data via a memory overread issue.
A critical vulnerability, tracked as CVE-2026-3055 (CVSS score of 9.3), in Citrix NetScaler ADC and Gateway is already being actively probed by attackers.
This week, Citrix issued security updates for two NetScaler vulnerabilities, including the critical memory overread issue CVE-2026-3055 (CVSS score of 9.3), that allows unauthenticated attackers to leak sensitive data.
The flaw CVE-2026-3055 is an insufficient input validation leading to memory overread, it can be triggered only if Citrix ADC or Citrix Gateway are configured as a SAML IDP.
Customers can check if their NetScaler appliance is set up as a SAML IDP by looking for the configuration string:
add authentication samlIdPProfile .*“This vulnerability, CVE-2026-3055, which is classified as an out-of-bounds read and holds a CVSS score of 9.3, allows unauthenticated remote attackers to leak potentially sensitive information from the appliance’s memory.” reads the advisory published by Rapid7 researchers. “The Citrix advisory states that systems configured as a SAML Identity Provider (SAML IDP) are vulnerable, whereas default configurations are unaffected. This SAML IDP configuration is likely a very common configuration for organizations utilizing single sign-on.”
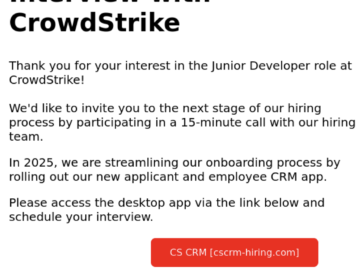
At this time, CVE-2026-3055 has no known in-the-wild exploits or public proof-of-concept. Citrix discovered it internally, but once exploit code is released, attacks are likely. Customers should patch immediately, as similar memory-leak flaws like “CitrixBleed” (CVE-2023-4966) were widely exploited in 2023.
watchTowr Intel researchers are not detecting active reconnaissance against NetScaler instances for CVE-2026-3055 through their honeypot network. The experts warn that in-the-wild exploitation of this issue is likely imminent.
Organizations using affected Citrix NetScaler versions should patch immediately, as ongoing reconnaissance could quickly turn into active exploitation, leaving little time to respond.
“watchTowr Intel is detecting active reconnaissance against NetScaler instances for CVE-2026-3055 through our Attacker Eye honeypot network. We believe that in-the-wild exploitation is likely imminent.” the cybersecurity firm wrote on LinkedIn. “Organizations running affected Citrix NetScaler versions in affected configurations need to drop tools and patch immediately. When attacker reconnaissance shifts to active exploitation, the window to respond will evaporate.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Citrix)