Google announced a new Chrome security feature that ties cookies to a specific device, blocking hackers from stealing and using them to hijack users’ accounts.
Cookies are files that websites use to remember your browsing information and preferences and automatically log you into a service or website. These cookies are created after you log into a service and verify multi-factor authentications, allowing them to bypass multi-factor authentication (MFA) in future logins.
Unfortunately, attackers use malware to steal these cookies, thus circumventing MFA prompts to hijack the linked accounts.
To solve this problem, Google is working on a new feature called Device Bound Session Credentials (DBSC) that makes it impossible for attackers to steal your cookies by cryptographically binding your authentication cookies to your device.
After enabling DBSC, the authentication process is linked to a specific new public/private key pair generated using your device’s Trusted Platform Module (TPM) chip that can’t be exfiltrated and is securely stored on your device, so even if an attacker steals your cookies, they won’t be able to access your accounts.
“By binding authentication sessions to the device, DBSC aims to disrupt the cookie theft industry since exfiltrating these cookies will no longer have any value,” said Kristian Monsen, a software engineer on Google’s Chrome Counter Abuse team.
“We think this will substantially reduce the success rate of cookie theft malware. Attackers would be forced to act locally on the device, which makes on-device detection and cleanup more effective, both for anti-virus software as well as for enterprise managed devices.”
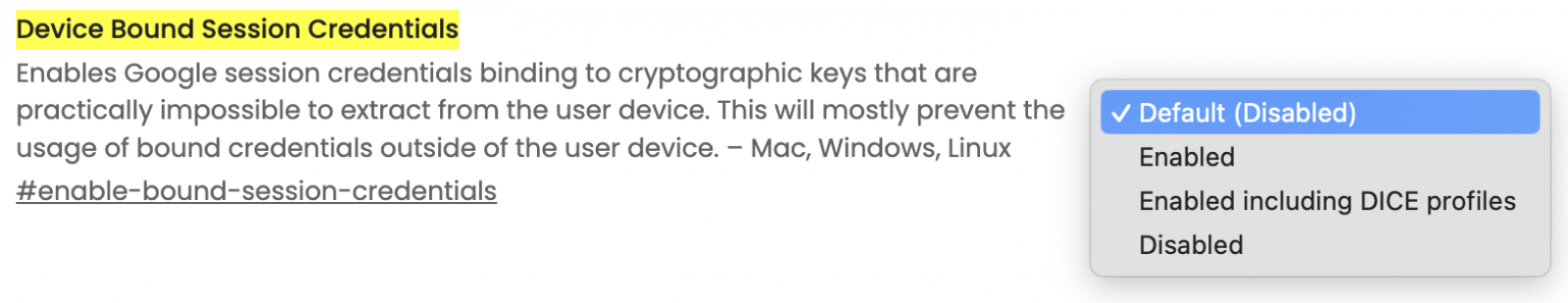
While still in the prototype phase, according to this estimated timeline shared by Google, you can test DBSC by going to chrome://flags/ and enabling the “enable-bound-session-credentials” dedicated flag on Windows, Linux, and macOS Chromium-based web browsers.
DBSC works by allowing a server to start a new session with your browser and associate it with a public key stored on your device using a dedicated API (Application Programming Interface).
Each session is backed by a unique key to protect your privacy, with the server only receiving the public key used to verify possession later. DBSC doesn’t enable sites to track you across different sessions on the same device, and you can delete the keys it creates at any time.
This new security capability is expected to be initially supported by about half of all Chrome desktop devices, and it will be fully aligned with the phase-out of third-party cookies in Chrome.
“When it’s deployed fully, consumers and enterprise users will get upgraded security for their Google accounts under the hood automatically,” Monsen added.
“We are also working to enable this technology for our Google Workspace and Google Cloud customers to provide another layer of account security.”
In recent months, threat actors have been abusing the undocumented Google OAuth “MultiLogin” API endpoint to generate new authentication cookies after previously stolen ones have expired.
Previously, BleepingComputer reported that the Lumma and Rhadamanthys information-stealing malware operations claimed they could restore expired Google authentication cookies stolen in attacks.
At the time, Google advised users to remove any malware from their devices and recommended enabling Enhanced Safe Browsing in Chrome to defend against phishing and malware attacks.
However, this new feature will effectively block the threat actors from abusing these stolen cookies, as they will not have access to the cryptographic keys required to use them.






