A newly discovered ClickFix campaign is targeting macOS users through a technique that completely bypasses Terminal, using Script Editor to drop the Atomic Stealer infostealer onto compromised systems.
This campaign marks a clear shift in how attackers are responding to Apple’s tightening security controls — a sharp reminder that social engineering can work around almost any technical barrier.
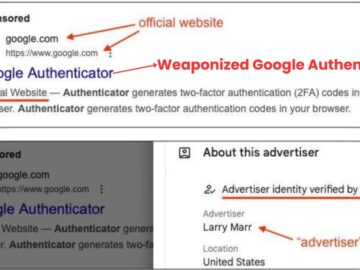
ClickFix attacks have traditionally relied on convincing users to copy and paste malicious commands into Terminal, usually under the cover of a routine troubleshooting or system maintenance step.
Apple directly addressed this in macOS 26.4 by introducing a security feature that scans commands pasted into Terminal before they execute, adding meaningful friction to that familiar attack path.
Rather than abandoning the tactic, attackers simply shifted the execution point — swapping Terminal for Script Editor, a built-in macOS application that supports AppleScript automation and carries a well-documented history of malware abuse.
Researchers at Jamf Threat Labs identified this new variant through one of their behavioral detection mechanisms, which flagged the Script Editor-based execution as suspicious activity in the wild.
The discovery reinforced just how quickly threat actors adapt when a new control gets in their way. In this case, the actors exploited the applescript URL scheme to invoke Script Editor directly from a web browser, quietly sidestepping the newer Terminal protections without tripping any obvious alerts.
The attack begins with a fake Apple-themed webpage, presenting itself as a disk space cleanup tool with step-by-step instructions that closely resemble legitimate macOS maintenance guidance.
.webp)
When the user clicks the Execute button, the page silently triggers the applescript URL scheme within the browser. The browser then shows a security permission dialog asking to open Script Editor making the whole process feel like a routine system task rather than an active threat.
.webp)
Once Script Editor opens, it displays a pre-populated script that is ready for the user to run. The script carries fake copyright headers claiming to be an Apple storage optimization utility, lending it a highly credible look.
%20and%20macOS%2026.4%20(right)%20(Source%20-%20Jamf).webp)
Depending on the macOS version, the experience differs with macOS 26.4 requiring users to approve saving the script to disk before execution proceeds.
Script Execution and Payload Delivery
Once a user runs the pre-filled script, the actual attack chain kicks off. The command embedded inside is obfuscated using a character-translation method through the tr utility, which converts a scrambled string at runtime into a working URL.
That URL calls curl with the -k flag, disabling TLS certificate validation and allowing the malware to reach untrusted infrastructure without triggering a warning. The downloaded content is piped directly into zsh and executed entirely in memory, never touching disk during this initial stage.
The first-stage payload uses base64 encoding combined with gzip compression to conceal its actual contents. Once decoded, it retrieves a Mach-O binary, saves it to /tmp/helper, strips extended attributes, assigns execution permissions, and runs it.
That binary is a recent Atomic Stealer variant — a well-known macOS infostealer that harvests browser credentials, saved passwords, cryptocurrency wallets, and other sensitive data from the infected machine.
The confirmed indicators of compromise include the domain dryvecar.com, along with storage-fixes.squarespace.com and cleanupmac.mssg.me, both tied to the fake ClickFix webpages used in this campaign.
The Mach-O binary saved as helper carries the SHA-256 hash 3d3c91ee762668c85b74859e4d09a2adfd34841694493b82659fda77fe0c2c44.
macOS users are strongly advised to avoid executing any script prompted by an external webpage, even those displaying Apple branding. Users should decline browser requests to open Script Editor or any automation tool from an unknown external source.
Keeping macOS updated to the latest available version is one of the most effective steps to ensure the newest built-in security controls are active and running against threats like this one.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.