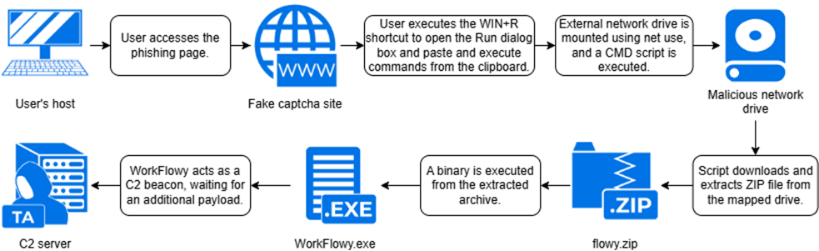
A new ClickFix scam tricks Windows users into running hidden commands that map hacker-controlled drives and load malware through trusted apps.
Cybersecurity researchers have discovered a cunning new twist on a well-known scam that targets everyday Windows users. This latest ClickFix attack, identified by the firm Atos, is particularly dangerous because it doesn’t rely on commonly know malware, and tricks victims into using your own device tools to open the door for hackers.
According to Atos, the scam starts on a dodgy website like ‘happyglamper.ro’ that greets visitors with a fake Captcha (the usual “prove you aren’t a robot” test). However, rather than clicking images of buses, the site tells you to press Windows + R, then Ctrl + V, and finally Enter. By following these steps, you are actually running a hidden command that the website has already silently copied to your clipboard.
The Brain-Swap Inside Trusted Apps
Researchers assessed that this version is stealthier than previous ones because it uses a standard Windows command called net use to connect your PC to a remote server. To your computer, this looks like a harmless connection to an office network drive. Once the connection is made, your PC automatically downloads a legitimate note-taking app called WorkFlowy (version 1.4.1050), originally signed by FunRoutine Inc.
However, the attackers have performed a brain swap on the app. They replaced a hidden file inside the software, known as an asar archive, with their own malicious code. Because the app itself is genuine, most security software simply looks the other way.
A Spy in the Background
Because the malware is hidden inside a trusted app, it gains high-level access to your system. Researchers noted that, “The malicious code runs in the Node.js main process with the full privileges of the logged-in user, allowing for the malicious code to executes any actions user is allowed to do on the system. No files are actually written to disk.”
This means, the virus bypasses the security sandboxes that usually stop apps from prying into your files. Once active, it generates a unique Victim ID and saves it in a file called id.txt, then begins messaging a hacker-controlled server at cloudflare.report every two seconds.
The threat has caught the attention of the wider security community. On X, Steven Lim, a cloud security expert and Microsoft MVP, raised the alarm about this “Cloudflare Win + R” variant. Using intelligence tools, Lim identified several other domains linked to this campaign, including modacontractors.uk, itexe.pl, and a spoofed static.cloudflareinsights.com, urging defenders to block them immediately.
Atos researchers caught the scam by hunting through the RunMRU registry key, a digital ledger that records every command typed into the Windows Run box. Because the malware leaves almost no other trace on the hard drive, this registry footprint was the only proof the attack had occurred.
It shows that since these scams now hide behind native Windows tools, we must be more careful than ever about which keys we are told to press.