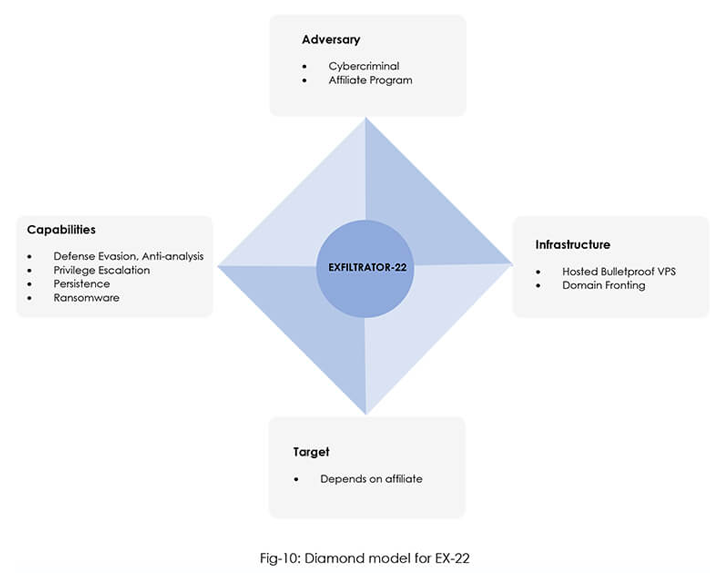
A new post-exploitation framework called EXFILTRATOR-22 (aka EX-22) has emerged in the wild with the goal of deploying ransomware within enterprise networks while flying under the radar.
“It comes with a wide range of capabilities, making post-exploitation a cakewalk for anyone purchasing the tool,” CYFIRMA said in a new report.
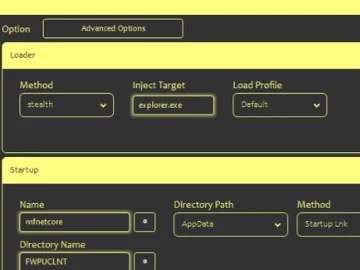
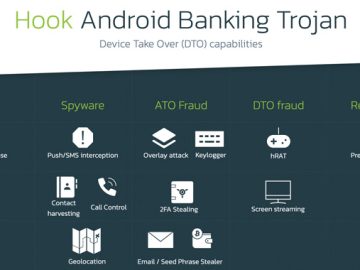
Some of the notable features include establishing a reverse shell with elevated privileges, uploading and downloading files, logging keystrokes, launching ransomware to encrypt files, and starting a live VNC (Virtual Network Computing) session for real-time access.
It’s also equipped to persist after system reboots, perform lateral movement via a worm, view running processes, generate cryptographic hashes of files, and extract authentication tokens.
The cybersecurity firm assessed with moderate confidence that threat actors responsible for creating the malware are operating from North, East, or Southeast Asia and are likely former affiliates of the LockBit ransomware.
Advertised as a fully undetectable malware on Telegram and YouTube, EX-22 is offered for $1,000 a month or $5,000 for lifetime access. Criminal actors purchasing the toolkit are provided a login panel to access the EX-22 server and remotely control the malware.
Since its first appearance on November 27, 2022, the malware authors have continuously iterated the toolkit with new features, indicating active development work.
The connections to LockBit 3.0 arise from technical and infrastructure overlaps, with both malware families utilizing the same domain fronting mechanism for hiding command-and-control (C2) traffic.
Is Your Business Prepared for the Top SaaS 🛡️ Security Challenges of 2023? Learn How to Tackle Them – Join Our Webinar Now!
The post-exploitation-framework-as-a-service (PEFaaS) model is the latest tool available for adversaries looking to maintain covert access to compromised devices over an extended period of time.
It also joins other frameworks like Manjusaka and Alchimist as well as legitimate and open source alternatives such as Cobalt Strike, Metasploit, Sliver, Empire, Brute Ratel, and Havoc that have been co-opted for malicious ends.