Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as Remcos RAT using a malware loader called IDAT Loader.
The attack has been attributed to a threat actor tracked by the Computer Emergency Response Team of Ukraine (CERT-UA) under the moniker UAC-0184.
“The attack, as part of the IDAT Loader, used steganography as a technique,” Morphisec researcher Michael Dereviashkin said in a report shared with The Hacker News. “While steganographic, or ‘Stego’ techniques are well-known, it is important to understand their roles in defense evasion, to better understand how to defend against such tactics.”

IDAT Loader, which overlaps with another loader family called Hijack Loader, has been used to serve additional payloads like DanaBot, SystemBC, and RedLine Stealer in recent months. It has also been used by a threat actor tracked as TA544 to distribute Remcos RAT and SystemBC via phishing attacks.
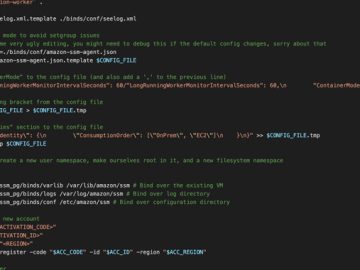
The phishing campaign – first disclosed by CERT-UA in early January 2024 – entail using war-themed lures as a starting point to kick-start an infection chain that leads to the deployment of IDAT Loader, which, in turn, uses an embedded steganographic PNG to locate and extract Remcos RAT.
The development comes as CERT-UA revealed that defense forces in the country have been targeted via the Signal instant messaging app to distribute a booby-trapped Microsoft Excel document that executes COOKBOX, a PowerShell-based malware that’s capable of loading and executing cmdlets. CERT-UA has attributed the activity to a cluster dubbed UAC-0149.

It also follows the resurgence of malware campaigns propagating PikaBot malware since February 8, 2024, using an updated variant that appears to be currently under active development.
“This version of the PikaBot loader uses a new unpacking method and heavy obfuscation,” Elastic Security Labs said. “The core module has added a new string decryption implementation, changes to obfuscation functionality, and various other modifications.”