Cybersecurity researchers at Moonlock Lab have identified a new macOS malware strain, notnullOSX, engineered to drain cryptocurrency wallets. In particular, it uses a submission form to assess a victim’s financial holdings, targeting only those with balances exceeding 10,000 USD. The malware was first detected on 30 March 2026, with confirmed activity in Vietnam, Taiwan, and Spain.
The Return of a Notorious Developer
The story behind the malware began with a developer known as 0xFFF, who left a hacking forum in 2023 after a public argument. By August 2024, he returned using the name alh1mik and promised to build a powerful new tool for the macOS platform. By early 2026, he delivered this modular program, which is far more advanced than his earlier work.
Deceptive Tactics and Fake Applications
Moonlock Lab’s investigation reveals that the hackers rely on social engineering to trick people into infecting their own computers. One common method they use is a fake protected Google Document that shows an encryption error, such as claiming a Google API Connector is out of date.
Additionally, users are told to copy a specific command into their Mac’s Terminal, which is the ClickFix trap, to fix it. As we know it, many developers and crypto users use the Terminal daily, making them more likely to paste the code without realizing it installs malware.
Once the command runs, the program asks for Full Disk Access. Researchers noted that granting this permission basically bypasses Apple’s security framework, allowing the malware to silently read iMessages, Apple Notes, and Safari credentials.
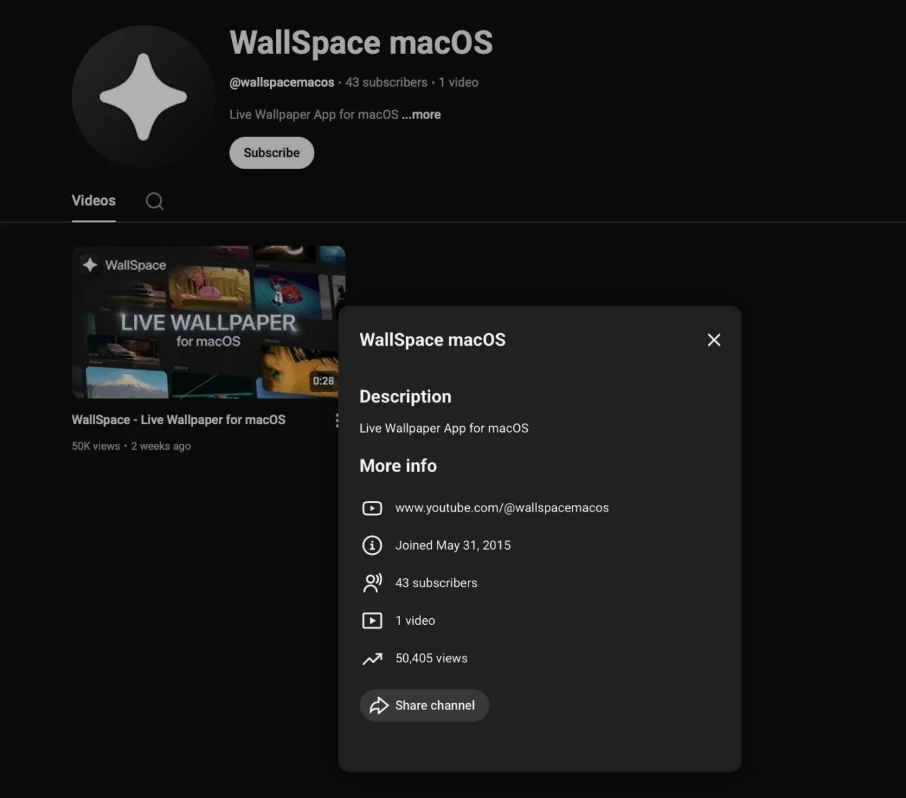
The hackers also created a malicious version of a real app called WallSpace. They promoted it through a hijacked YouTube channel that had been active for ten years, gaining 50,000 views in just two weeks. Once installed, the malware keeps a backdoor open so hackers can send new instructions at any time.
Targeting High-Value Crypto Assets
The most concerning part is how notnullOSX handles hardware wallets. Further probing revealed a feature called ReplaceApp, which swaps legitimate apps like Ledger Live or Trezor with fake versions. This allows hackers to steal secret seed phrases as the user types them. The malware also targets desktop wallets like Bitcoin Core, Exodus, and MetaMask.
In their final analysis, the team at Moonlock Lab stated that this new version is “the product of someone who spent 2 years paying attention to what the macOS threat landscape required.” This shows that even hardware wallets are not safe if the software managing them is fake. While this threat currently focuses on high-value targets, researchers believe this platform will likely expand in the future.