A new Android malware called Perseus is checking user-curated notes to steal sensitive information, like passwords, recovery phrases, or financial data.
Distributed over unofficial stores disguised as IPTV, Perseus allows complete device takeover, screenshot capturing , and overlay attacks.
By posing as IPTV apps, which are often used to stream pirated content, the threat actor relies on the user’s familiarity with sideloading APKs from outside the Google Play store and ignoring security warnings.
This trend has emerged over the past eight months, as users seek free or low-cost ways to access live sports broadcasts. In a recent campaign, threat actors leveraged the IPTV app lure to distribute the Massiv Android banking malware.
According to researchers at mobile security company ThreatFabric, Perseus is primarily targeting financial institutions in Turkey and Italy, as well as crypto services.
One app loading the malware is called Roja Directa TV, a popular sports streaming service that has been the target of copyright infringement and shutdown actions.
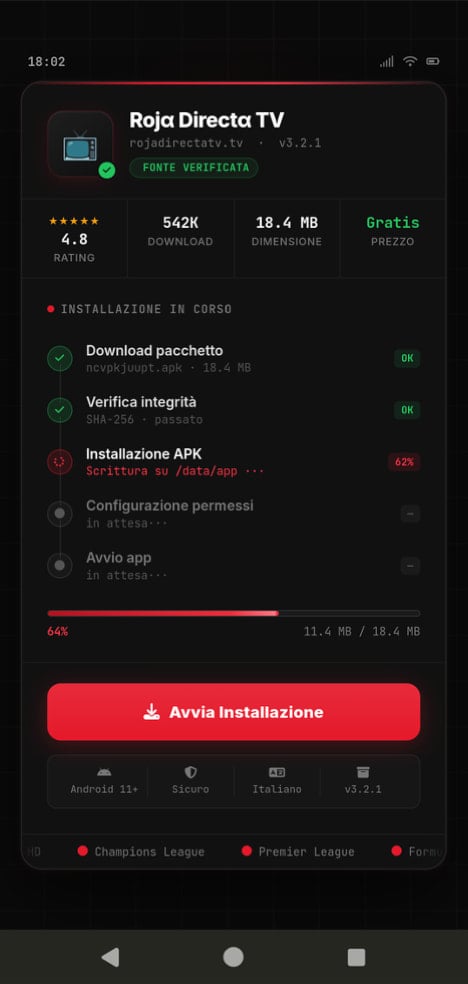
Source: ThreatFabric
The dropper for Perseus can bypass Android 13+ sideloading restrictions and is the same one for delivering the Klopatra and Medusa malware.
According to ThreatFabric researchers, “Perseus appears to build specifically on the Phoenix codebase,” which was created from the Cerberus code, leaked almost six years ago.
In a report today, the researchers say that the malware has two versions, one in Turkish and a more refined one in English, which also features better debugging and additional quality-of-life features.
The English variant includes extensive logging and emojis in the code, which is a strong indication that AI tools were used in the development process.
A focus on Turkey is also evident in the list of targeted financial institutions in the country (17), followed by Italy with 15, Poland with 5, Germany (3), and France (2). The malware also targets 9 cryptocurrency apps.
By abusing Android Accessibility Services, Perseus gives operators full remote control over the infected devices, enabling them to:
- Capture screenshots continuously and stream them to the operator (start_vnc)
- Send a structured UI hierarchy for programmatic remote interaction (start_hvnc)
- Simulate taps, swipes, text input, long presses, and other UI navigation actions
- Turn the screen on, launch apps, and block apps
- Enable a black screen overlay to hide activity from the victim
- Launch overlay attacks and perform keylogging
Perseus’ unusual feature targets Android note-taking apps, including Google Keep, Xiaomi Notes, Samsung Notes, ColorNote, Evernote, Microsoft OneNote, and Simple Notes.
ThreatFabric researchers note that this is the first time they’ve seen an Android malware checking for sensitive details in personal notes on the device.
“While many Android malware families focus primarily on harvesting credentials or intercepting communications, this feature reflects a broader interest in contextual and personally curated data,” reads the ThreatFabric report.
“Notes often contain sensitive information such as passwords, recovery phrases, financial details, or private thoughts, making them a valuable target for attackers.”
The malware’s English version uses Accessibility Services to systematically open the notes apps one by one and scan individual notes stored in them.
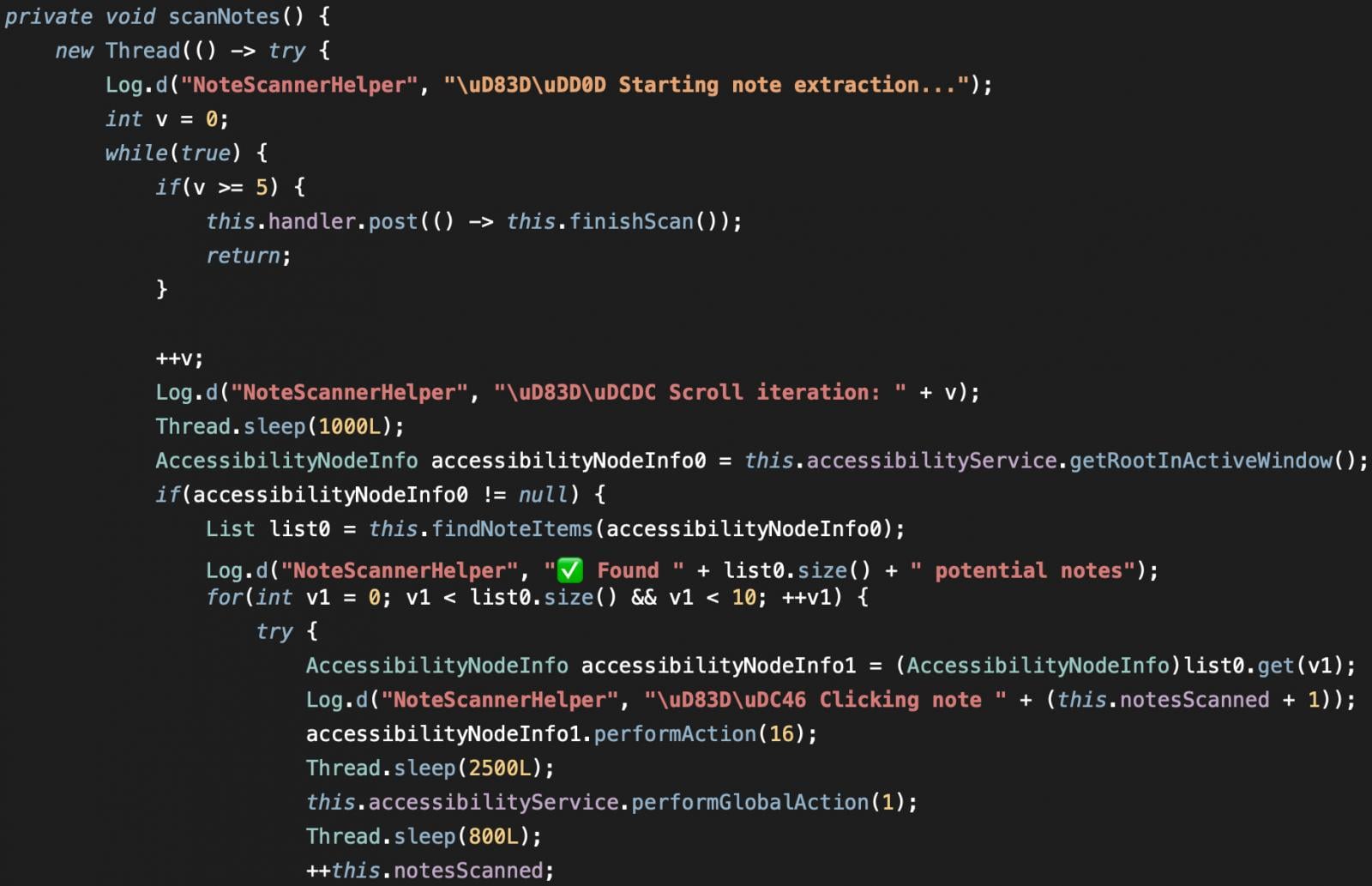
Source: Threat Fabric
Perseus performs extensive anti-analysis and evasion checks before executing on a device, including root, emulator fingerprints, SIM details, hardware profile, battery data, Bluetooth presence, app count, and Google Play Services availability, and formulates a “suspicion score” that it sends to the command-and-control (C2) panel.
Based on that score, the operator decides whether to proceed with data theft.
To minimize risk, Android users are recommended to avoid sideloading APKs from questionable sources and to only download legal streaming apps from the official Android app store, Google Play. Also, ensure that Play Protect is active and use it to regularly scan the device for known threats.

Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.







