Cofense researchers have found a new phishing scam where threat actors use LiveChat software to impersonate brands like Amazon and PayPal. By chatting with victims in real-time, these cybercriminals are able to bypass security codes and steal credit card information.
Online threat actors have found a new way to trick people by using live chat tools that we usually see on official business websites. According to the latest research from the Cofense Phishing Defense Center (PDC), a new wave of scams is using a software-as-a-service (SaaS) tool called LiveChat to talk to victims in real-time, making their theft attempts feel much more believable.
How the Trap is Set
The scam begins with an email. While most junk mail is easy to ignore, these messages stand out for their clever tricks to get you to click. One version mimics a PayPal notification claiming you have a $200.00 USD refund waiting. This email includes a button to view transaction details to act as a hook. Another version is much more generic, simply stating that an order is pending and needs your confirmation.
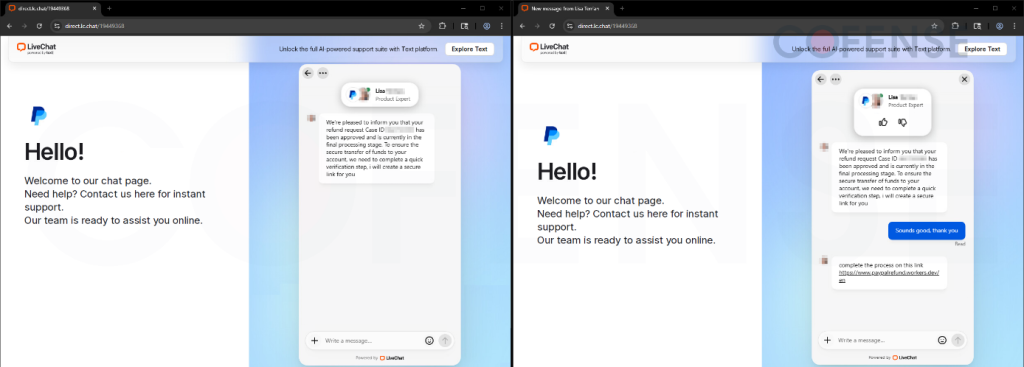
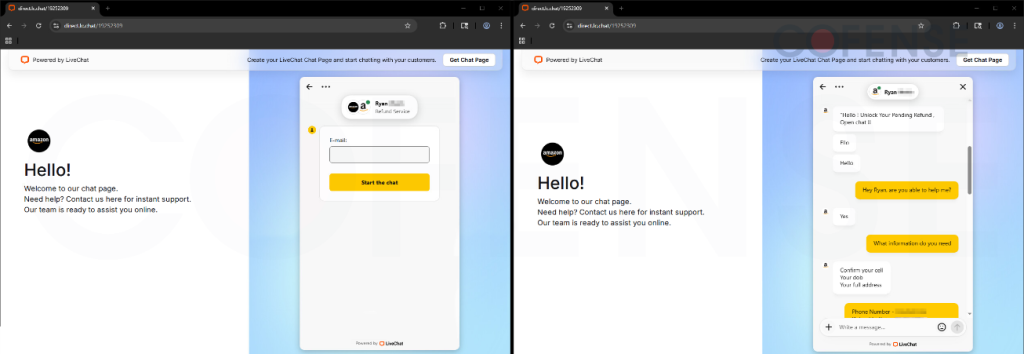
Further probing revealed that these emails contain links, specifically using the domain lc.chat, that lead to a live messaging box. This is where the LiveChat software comes in. Instead of just landing on a fake webpage, you are greeted by what looks like a helpful customer service agent or an automated bot.
Real-Time Deception
According to Cofense, cybercriminals customise these chat boxes to look like famous brands like Amazon and PayPal. In the Amazon version, a fake agent engaged in a back-and-forth conversation with the user. Researchers noted that the agent’s language was often messy and unprofessional, with strange greetings like “Ello” and odd punctuation like “Hello !” or “Open chat !!”. This suggested a real person was typing on the other end rather than a polished computer program.
During these chats, the threat actors ask for sensitive data, including personally identifiable information (PII), which includes private details like names, addresses, phone numbers, and dates of birth. They also go after banking details such as full credit card numbers, expiration dates, and CVC codes, and even try to snatch multi-factor authentication (MFA) codes, which are those one-time security passwords sent to your phone to verify your identity.
Why It Works
Using a live chat makes the scam feel authentic. We are used to resolving issues through these boxes on real shopping sites, so our guard is naturally lower, and that’s actually the catch here. Once the scammers get a victim’s login and phone code, they can bypass security and “drain the user’s financials” by taking control of the account, the report explains.
It is worth noting that the attackers often promise that your data will be “handled with the utmost confidentiality” just to make you feel safe while they steal your money. By the time the chat ends with a polite thank you, the damage is already done. So, staying cautious of unexpected refund offers remains the best way to stay safe.
“We highlighted two threats that combine brand impersonation, social engineering, credential theft, identity theft, and other techniques that demonstrate the rapid evolution and integration of threats. These cases highlight why human-driven analysis remains essential,” Cofense’s report concludes.






