Security researchers have released a new Proof of Concept (PoC) for a vulnerability in the Windows Common Log File System (CLFS) driver.
The flaw, identified as CVE-2026-2636, allows low-privileged users to force a system into a Blue Screen of Death (BSoD), effectively causing a Denial of Service.
Vulnerability Mechanism
The discovery occurred while a researcher was analyzing the CLFS driver for Remote Code Execution (RCE) flaws.
Instead, they found that modifying specific values in the exploit chain triggered a system crash.
According to coresecurity, the vulnerability stems from improper handling of invalid elements (CWE-159) within CLFS.sys.
When a user executes a ReadFile command using a handle from an opened .blf log file, the driver fails to handle the input correctly.
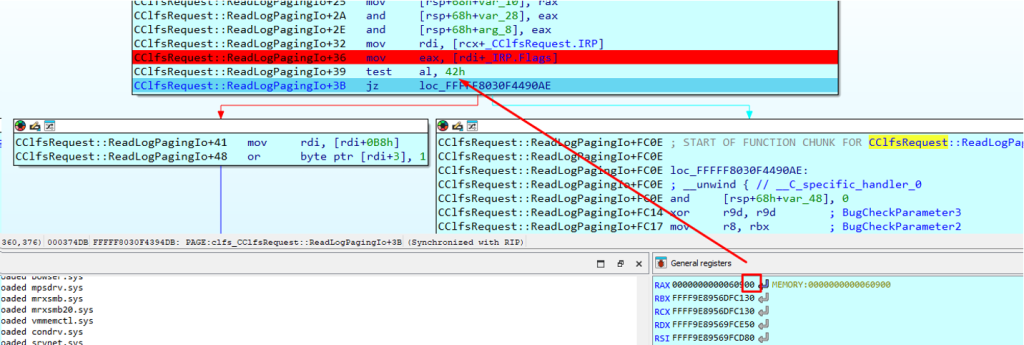
Specifically, the crash happens because internal routines expect specific flags such as IRP_PAGING_IO or IRP_INPUT_OPERATION to be enabled within the I/O request structure.
In the PoC scenario, these flags are disabled, leading the driver to an unrecoverable state. To protect the integrity of the OS, Windows invokes KeBugCheckEx, causing the immediate BSoD.
While the CVSS score is a moderate 5.5, the impact on availability is high. Any user logged into a vulnerable machine can crash it without needing administrator permissions.
Microsoft silently patched this issue in the September 2025 cumulative update. Windows 11 2024 LTSC and Windows Server 2025 are already protected, but older versions like Windows 11 23H2 remain vulnerable if not updated.
| Metric | Details |
|---|---|
| CVE ID | CVE-2026-2636 |
| CVSS Score | 5.5 (Medium) |
| Vulnerability Type | Denial of Service (BSoD) |
| Affected Component | CLFS.sys Driver |
| Root Cause | CWE-159 (Improper Handling of Special Elements) |
| Trigger Method | ReadFile call on .blf log handle |
| Fixed Version | September 2025 Cumulative Update |
Organizations running older builds of Windows 10 or 11 should ensure the September 2025 security updates are applied.
While this flaw does not allow for data exfiltration, the ability for a standard user to repeatedly crash servers or workstations poses a significant operational risk.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.