CyberProof researchers have detected a 10% surge in PXA Stealer attacks targeting financial institutions in Q1 2026. Learn how this malware uses phishing and Telegram to steal passwords and crypto.
Financial firms across the globe are facing a fresh wave of digital break-ins this year. According to cyber threat detection firm CyberProof, a relatively new malware known as the PXA Stealer has seen a sudden spike in activity.
During the first quarter of 2026, experts tracked an 8% to 10% increase in attacks using this specific tool. However, this spike isn’t a coincidence because it follows the high-profile police takedowns of older infostealers like RedLine and Lumma in 2025.
This indicates that PXA has stepped in to take their place. In a report shared with Hackread.com, CyberProof threat intelligence experts noted that these new campaigns are becoming increasingly adaptable, switching between different disguises to trick employees.
How the Infection Spreads
The scam usually starts with a simple phishing email that isn’t always obvious junk mail and often looks like legitimate messages about tax forms, legal documents, or even Adobe Photoshop installers. One common version involves a file named Pumaproject.zip. When a curious user opens it, the trap is set.
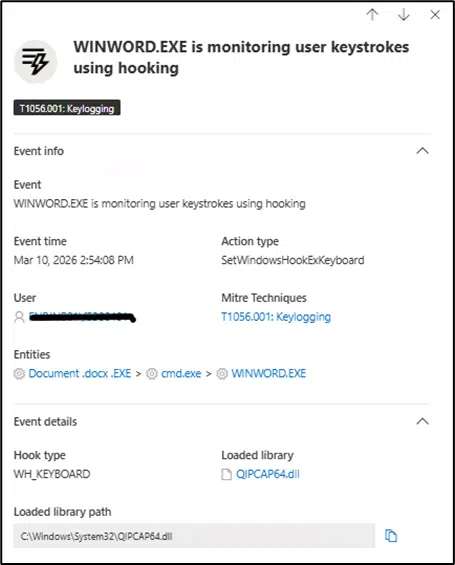
Further research reveals that the hackers use a multi-layered approach to stay hidden. The malware creates a secret folder on the computer named Dots and uses a specific password, shodan2201, to unpack its most dangerous components. To a casual observer, the computer might look fine because the virus renames its main files to svchost.exe, a name used by standard Windows processes, to blend into the background.
What Data is at Risk
The attackers are mainly targeting user credentials and crypto wallets. Once inside, the PXA Stealer quietly starts harvesting saved login passwords from web browsers, private keys from cryptocurrency wallets, and sensitive data from specific financial websites.
It is worth noting that the hackers even use a digital tracking tag, or BOT_ID, known as Verymuchxbot, to organise their stolen goods. According to researchers, the stolen data is eventually sent back to the criminals via Telegram channels. To make matters worse, the malware achieves persistence by adding a value registry entry. This means it is programmed to restart itself every time the computer is turned on.
Staying Safe
The best defence is a healthy dose of scepticism. Experts suggest being extremely wary of emails with attachments ending in .zip or .rar, particularly if they claim to be urgent invoices. Monitoring for unusual background connections to web addresses ending in .xyz or .shop can also help catch an infection before the data leaves the building. It is also a good idea to watch out for files with names like .vbs or .js that pop up unexpectedly.