A new Rust-based version of the Qilin (Agenda) ransomware strain, dubbed ‘Qilin.B,’ has been spotted in attacks, featuring stronger encryption, better evasion from security tools, and the ability to disrupt data recovery mechanisms.
Qilin.B was spotted by security researchers at Halcyon, who warned about the threat and shared indicators of compromise to help with early detection.
Qilin updates its encryptor
Starting with the new encryption scheme, Qilin.B users AES-256-CTR with AESNI capabilities for CPUs that support it, speeding up the encryption.
However, the new strain retains ChaCha20 for weaker or older systems that don’t have the appropriate hardware for AESNI, ensuring robust encryption in any case.
Qilin.B also incorporates RSA-4096 with OAEP padding for encryption key protection, making decryption nearly impossible without the private key or captured seed values.
Upon execution, the new Qilin malware adds an autorun key in the Windows Registry for persistence and terminates the following processes to free up critical data for encryption and disable security tools.
- Veeam (backup and recovery)
- Windows Volume Shadow Copy Service (system backup and recovery)
- SQL database services (enterprise data management)
- Sophos (security and antivirus software)
- Acronis Agent (backup and recovery service)
- SAP (enterprise resource planning)
Existing volume shadow copies are wiped to prevent easy system restoration, and Windows Event Logs are cleared to hinder forensic analysis. The ransomware binary is also deleted after the encryption process has been completed.
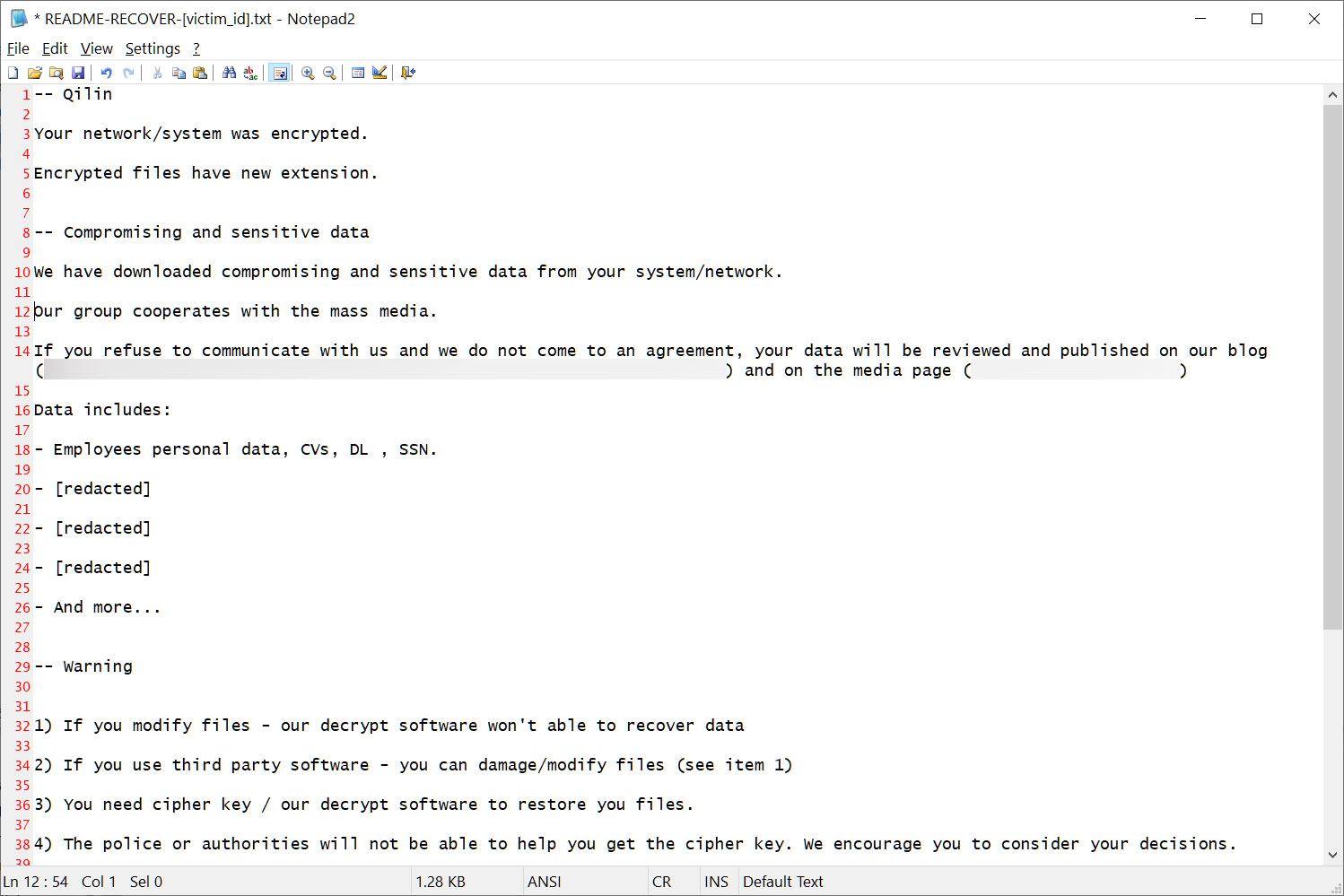
Qilin.B targets both local directories and network folders and generates ransom notes for each directory processed, including the victim ID in the title.
Source: BleepingComputer
For maximum reach, it modified the Registry with a separate entry to enable sharing of network drives between elevated and non-elevated processes.
Although the above are not ground-breaking features in the ransomware space, they can have a severe and far-reaching impact when they’re added to a family used by notorious threat groups in highly effective attacks.
Last August, Sophos revealed that Qilin deploys a custom info-stealer in attacks to collect credentials stored in the Google Chrome browser and extend their attacks to entire networks or re-introduce itself on breached networks even after cleanups.
Previously, Qilin was used in highly damaging attacks against major London hospitals, Court Services Victoria in Australia, and automotive giant Yanfeng.
The group also uses a Linux variant focused on VMware ESXi attacks, but the variant Halcyon spotted concerns Windows systems.







