Cybersecurity Researchers from Zimperium zLabs have shared details on four new Android malware families currently being used in four different campaigns targeting Android banking and crypto apps. These are capable of stealing private data from more than 800 apps, according to Zimperium’s report shared with Hackread.com.
Meet the Four Families
The zLabs team has been busy tracking these threats, which they’ve named RecruitRat, SaferRat, Astrinox, and Massiv. Each one uses a different trick to lure users into downloading the malware, with the most common methods being phishing and smishing.
Phishing involves fake websites that look exactly like real login pages for banks or popular services. For example, the SaferRat campaign uses websites that promise free access to premium video streaming services to lure victims in.
In Smishing, urgent text messages are used claiming there is a problem with your account, with a link that downloads the malicious payload after clicking. RecruitRat campaign uses fake job-seeking sites and targets employment seekers, making them download an APK file that looks like a job application.
Then there is Astrinox, which mimics a business tool called HireX on the site xhirecc. While researchers found a fake Apple App Store page for this one, they noted that the actual malicious payloads are currently only targeting Android users. The final group, Massiv, is a mystery; though, it is so well-hidden that researchers couldn’t find any clear sign of how it spreads.
The Blindfold Trick
Once these apps infect a phone, they quickly launch an Overlay attack. This involves a fake screen that pops up right when you open a real app, like your bank or a crypto wallet. If you type your password, you aren’t giving it to the bank but to the hackers.
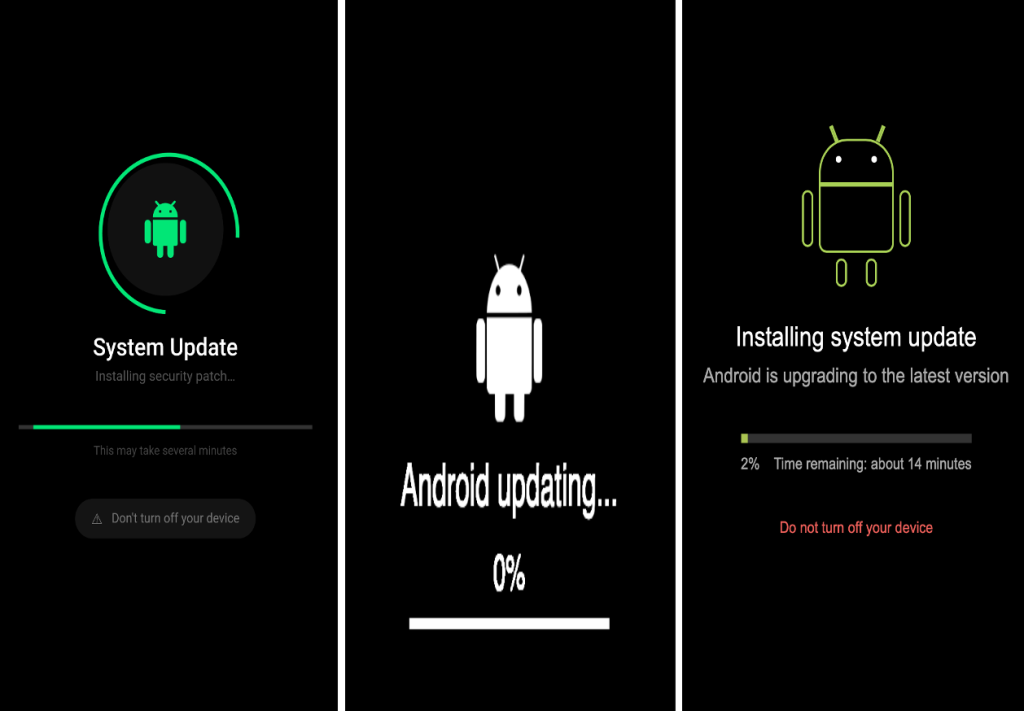
To prevent raising suspicion, Zimperium’s report found that the malware uses a blindfold. By abusing Accessibility Service permissions, it can put a non-moving image over your screen. So, you get to see a frozen page or a fake Android Update screen, while the hackers work in the background, seeing your contacts, reading your SMS messages, and even recording your screen using the MediaProjection framework.
Bypassing Your Security
One of the most dangerous parts of these attacks is how they handle security codes. We always feel safe because of one-time passwords (OTPs) sent via text, but these programs can intercept those texts in real-time.
Researchers noted that RecruitRat even has a library of over 700 fake login pages stored inside it, activating the moment you open a targeted app. These threat actors are also using Keylogging to track every single tap you make. By using a constant link through WebSockets, they stay connected to your device, waiting for the perfect moment to strike. Experts suggest avoiding clicking links in urgent texts and downloading apps only from the official platforms.