A new, sophisticated malware campaign dubbed “LTX Stealer.” This malware represents a shift in attacker techniques, utilizing legitimate software frameworks and cloud services to hide its activities and steal sensitive user data.
By mimicking standard Windows processes, LTX Stealer is designed to operate quietly, making it difficult for traditional antivirus systems to detect.
The malware is distributed through a heavily disguised installer built with “Inno Setup,” a common tool used by legitimate developers to create Windows software installers.
The malicious file, identified in this campaign as “Negro.exe,” appears to be a standard application. However, distinct metadata tags explicitly reference the LTX Stealer, signaling its true nature.
To evade detection, the installer contains a massive, encrypted archive. Approximately 99.9% of the file contents are encrypted, preventing security tools from scanning the malicious code inside.
At CYFIRMA, we observed attacker techniques that rely on legitimate installers and user trust to enable low noise system compromise.
Several components were notable, including updater.exe, a bundled python.exe with associated runtime libraries, multiple SQLite database file.
Once a victim runs the installer, it requests administrator privileges. If granted, it drops a payload named updater.exe into a hidden system folder designed to look like a Microsoft update component.
Under the Hood: Node.js and Obfuscation
What makes LTX Stealer unique is its internal architecture. The updater.exe file is not a standard virus but a bundled Node.js runtime environment.
The attackers use a tool called pkg to package the malicious JavaScript code with the runtime.
By duplicating the LSASS access token and applying it to the current execution thread, the code temporarily executes under SYSTEM context.
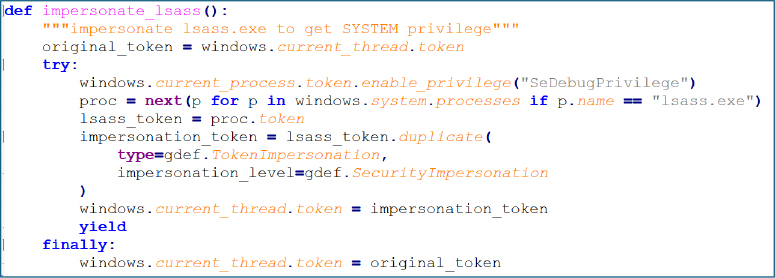
Furthermore, the attackers employ “Bytenode” compilation. Instead of leaving the malicious code as readable JavaScript, they compile it into bytecode.
This technique deliberately hinders security researchers’ attempts to reverse-engineer or analyze the malware’s logic.
Once active, LTX Stealer aggressively targets sensitive information. It primarily focuses on Chromium-based web browsers like Google Chrome and Microsoft Edge.
The malware includes a Python script (decrypt.py) that mimics the browser’s own decryption processes. This allows the attackers to bypass encryption protections and extract:
- Saved login credentials (usernames and passwords).
- Browser cookies.
- Active session tokens.
In addition to browser data, LTX Stealer specifically hunts for cryptocurrency assets. It scans the infected computer for wallet files and data from browser-based crypto extensions, packaging everything into an archive for exfiltration.
Infrastructure and Business Model
The malware’s backend infrastructure relies on legitimate cloud services to blend in with normal network traffic.
The malware resolved the domain api.eqp.lol, which returned the following IP addresses:
- 172.67.153.236
- 104.21.12.237
![Further investigation identified an additional panel server hosted on a separate IP address: 69[.]164.242.27 (Source : CYFIRMA).](https://www.cyfirma.com/media/2026/02/stealer08-17.jpg)
It uses Supabase for authentication and database management, and Cloudflare to hide the location of its command-and-control servers.
CYFIRMA analysis suggests that LTX Stealer is being operated as a “Stealer-as-a-Service” (SaaS).
The malware is advertised on public channels for as little as $10 per week or $25 per month. Evidence points to the developers likely being based in Brazil, as early samples and pricing structures align with activity in that region.
This low-cost, scalable model indicates that LTX Stealer is designed for widespread, indiscriminate attacks rather than targeted espionage.
INDICATORS OF COMPROMISES
| Indicator | Type | Remarks |
| eqp[.]lol | Domain | Panel |
| 69[.]164.242.27 | Domain | Panel |
| ca9798f6bb9ad81dc20f8dee10c19368a44f3e48d71fa823b9c6f3b6473ca518 | SHA256 | Updater.exe (Dropped Node.js–based packaged stealer) |
112d731bbfd7379cdf3263cbba39a170c235d616c26b803f3afe6b014f4748a1 | SHA256 | Negro.exe (Setup file) |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.