North Korea-linked APT Sapphire Sleet targets IT job seekers with bogus skills assessment portals

North Korea-linked APT group Sapphire Sleet set up bogus skills assessment portals in attacks aimed at IT job seekers.
The North Korea-linked APT group Sapphire Sleet (aka APT38, BlueNoroff, CageyChameleon, and CryptoCore) is considered a sub-group of the popular Lazarus APT group. The APT group’s campaigns focus on cryptocurrency exchanges, venture capital firms, and banks.
Microsoft researchers warn of a new social engineering campaign aimed at IT job seekers that relied on a new cluster of bogus skills assessment portals.
“The threat actor that Microsoft tracks as Sapphire Sleet, known for cryptocurrency theft via social engineering, has in the past few weeks created new websites masquerading as skills assessment portals, marking a shift in the persistent actor’s tactics.” warns Microsoft through a series of posts on X.
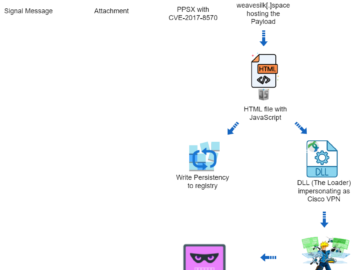
In the past, Sapphire Sleet was observed using platforms like LinkedIn and employed lures related to skills assessment. Once established communication with the victims, the threat actors move it to other platforms, like instant messaging apps or email.
Sapphire Sleet sent weaponized attachments directly or used links to pages hosted on legitimate websites like GitHub. Microsoft experts believe that after it uncovered Sapphire Sleet’s tactics, the APT group switched to new attack techniques by creating its own websites.
The group created multiple domains to trick recruiters into registering for an account.
Researchers from Jamf Threat Labs recently discovered a new macOS malware strain dubbed ObjCShellz and attributed it to North Korea-linked APT BlueNoroff. The experts noticed that the ObjCShellz malware shares similarities with the RustBucket malware campaign associated with the BlueNoroff APT group.
The researchers have yet to determine which were the victims of the ObjCShellz attacks, however, the choice of using a domain similar to the one of a legitimate exchange suggests that threat actors targeted an entity or an individual with an interest in the crypto currency sector.
Recently Elastic Security Labs reported that North Korea-linked Lazarus APT group was spotted using new KandyKorn macOS malware in attacks against blockchain engineers.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, North Korea)