North Korean state-backed hackers are running large-scale fake IT worker and “Contagious Interview” campaigns that abuse developer hiring workflows to deliver JavaScript-based malware, steal code and credentials, and covertly generate revenue for the regime.
Since at least 2022, North Korean threat actors have impersonated recruiters and hiring managers, luring software developers into executing booby-trapped code projects as part of technical interviews.
Under the Contagious Interview campaign, candidates are asked to clone a repository, test tasks, or debug a project that secretly contains loaders for custom malware families such as BeaverTail and Ottercookie.
Once executed, these projects can harvest credentials, steal source code, and establish remote control over developer endpoints across Windows, Linux, and macOS.
GitLab’s 2025 threat intelligence shows that these actors rely heavily on JavaScript-based codebases and loaders, often using obfuscation and staged payload delivery to bypass casual code review.
A common pattern involves base64-encoded URLs and headers embedded in .env files, a “trigger” function that fetches remote content, and a custom error handler that abuses Function.constructor to run attacker-controlled code if an error occurs.
In more than 80% of observed cases, the actual malware payload is hosted off-platform on services like Vercel or attacker-controlled domains, with GitLab projects only delivering a concealed loader.
Fake IT Worker Schemes
Alongside Contagious Interview, North Korean operators are systematically building fake IT worker personas to infiltrate companies as contractors or full-time remote employees.
GitLab banned 131 accounts in 2025 linked to malicious projects and IT worker activity, and observed multiple distinct teams working in parallel, based on differing infrastructure, obfuscation styles, and malware variants.
One exposed cell, managed by North Korean national Kil-Nam Kang, kept detailed GitLab-hosted financial and personnel records showing more than US$1.64 million in earnings between Q1 2022 and Q3 2025 from freelance development work under false identities, likely operating out of Beijing under an academic cover story.
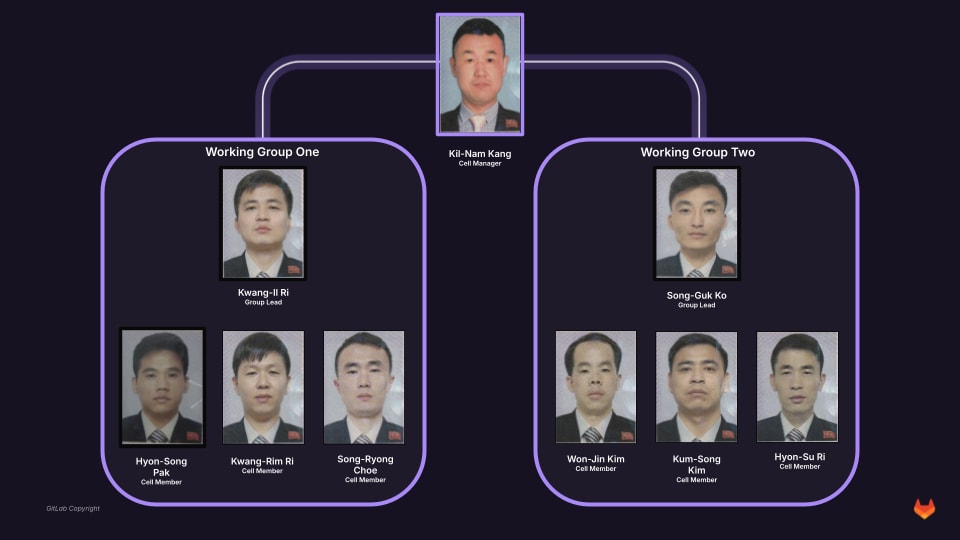
The cell tracked individual performance, stored passports, banking details, and remote-access credentials for members and facilitators across dozens of countries, illustrating an organized, quota-driven revenue operation.
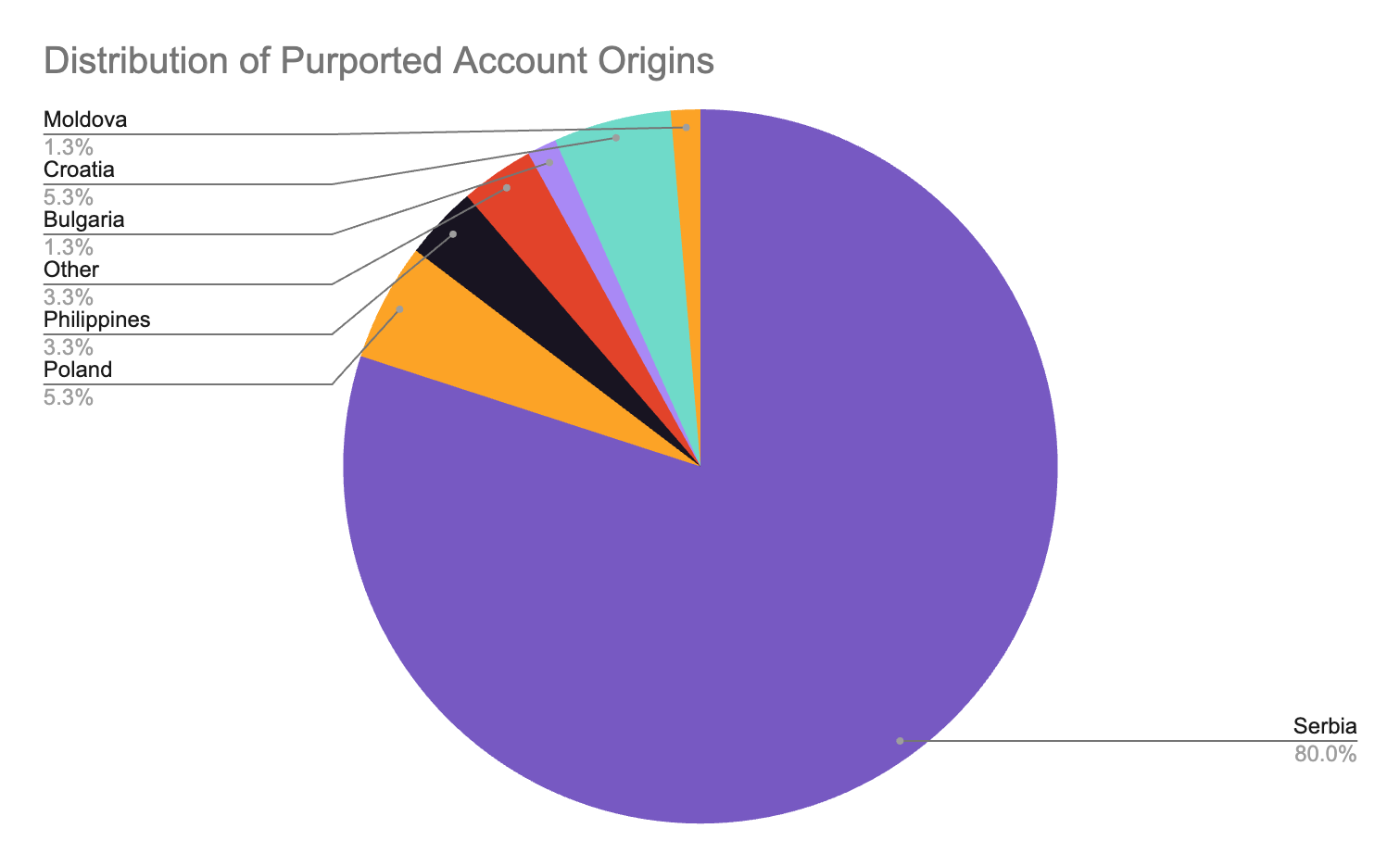
Another cluster developed a synthetic identity pipeline that scraped photos, used faceswapper.ai and illicit services like VerifTools to generate fake passports, and automated email and professional networking accounts, creating at least 135 personas and gaining access to 48 private codebases.
GitLab also identified an individual operator controlling 21 personas based on real identities, including U.S. victims whose documents were doctored by inserting the operator’s photo into genuine templates, and an additional fake IT worker likely operating from central Moscow, who progressed from freelance work to full-time roles while recruiting “laptop custodians” in the U.S. and U.K. for remote access.
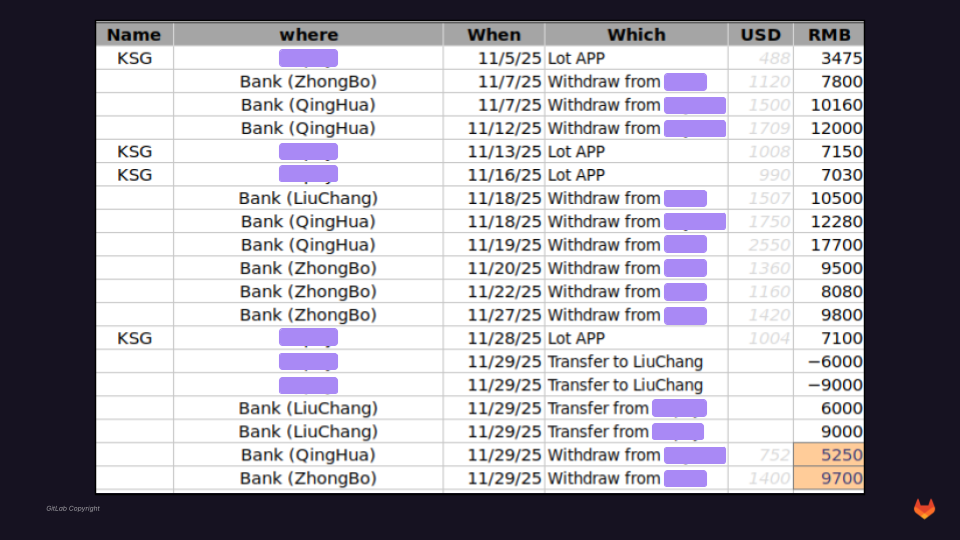
Reports compare team member earnings against predefined targets and quarter-over-quarter performance.
These activities align with FBI and DOJ warnings that North Korean IT workers use stolen or synthetic identities to secure remote jobs, exfiltrate proprietary data, extort companies, and generate funds that evade sanctions.
Evolving Tradecraft and Defensive Takeaways
North Korean malware activity on GitLab accelerated in the second half of 2025, peaking around September, with an average of 11 accounts per month banned for distributing malware or loaders.
The threat actor also had more than 73,000 leads stored in its database dump, providing insight into the scope of its outbound activities.
Operators increasingly adopted anti-analysis techniques, including sandbox checks in Ottercookie, invite-only private projects, malicious npm dependencies, and Visual Studio Code task-based execution chains to hide second-stage payload delivery.
GitLab additionally observed one developer using AI tools such as ChatGPT and Cursor to iteratively test and harden a custom obfuscator for BeaverTail, underscoring how generative AI can be repurposed to refine offensive tradecraft.
For defenders, the report highlights several priorities. Organizations should treat interview-linked coding projects, unsolicited test repositories, and portfolios with dead or thin professional profiles as high-risk, especially in crypto, finance, and real estate sectors disproportionately targeted by these campaigns.
Strengthening remote hiring due diligence, verifying identities and device ownership, and monitoring for anomalous use of code platforms, VPN-origin logins, and npm or VS Code-based execution chains are critical to detecting fake IT workers and contagious interview setups before they translate into data theft, ransomware, or long-term insider access.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.