A recent investigation as exposed how a suspected North Korean IT worker allegedly used a stolen identity, AI-generated resume content, and scripted interview answers to try to secure a senior remote role at U.S.-based threat intelligence firm Nisos.
The case highlights how DPRK IT employment schemes are evolving by combining traditional fraud with modern AI and remote access technologies.
He used stolen personally identifiable information (PII), a newly created email address, and a VoIP phone number designed to match the claimed U.S. location.
According to Nisos, the individual applied in June 2025 for a Lead AI Architect role, posing as a Florida-based senior full stack developer and AI specialist.
Network indicators tied the applicant to IP addresses believed to belong to the Astrill VPN anonymization network, a service previously linked to North Korean remote IT worker activity.
Investigators determined the resume was likely generated or heavily assisted by an AI chatbot.
AI-Generated Resume
The document mirrored the employer’s own job description, repeating long lists of skills and technologies, including programming languages, agentic AI tools, cloud platforms, databases, and OSINT tooling, directly lifted from the posting.
The summary section also reused language about researching and evaluating emerging agentic AI technologies, suggesting automated content creation rather than authentic experience.
During the virtual interview, Nisos analysts suspected the candidate was relying on an AI chatbot to answer questions in real time.
The operative frequently looked away from the camera and repeatedly began answers with the phrase “How can I say?”, appearing to wait for scripted responses.
When interviewers asked a fake question about a recent “hurricane George” in Florida a non-existent event the candidate still attempted to respond, reinforcing suspicions that he was reading generic AI-generated text rather than speaking from personal experience.
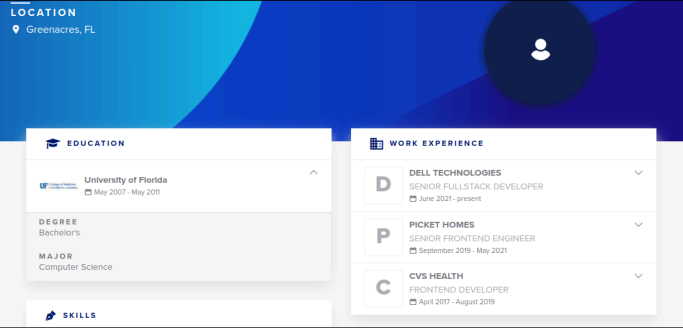
Pre-employment OSINT uncovered three different resume platform profiles tied to the same name but with inconsistent locations, universities, and employment histories.
All profiles appeared to reference the real addresses of an actual Florida resident, indicating that the operative had likely stolen that person’s identity.
Nisos’ investigation showed the network had searched for information about this real individual and later coordinated victim notification with law enforcement.
Nisos shipped a corporate laptop to the address provided by the applicant, which differed from the address on the resume a pattern common in DPRK workforce fraud.
Once activated, tracking showed the device stayed at that location, and the built-in camera revealed a “laptop farm” setup inside a closet containing numerous laptops.
Access to the device uncovered Raspberry Pi–based PiKVM hardware used for stealthy keyboard-video-mouse control, allowing remote operators to manage multiple corporate machines as if physically present, while evading typical endpoint detection mechanisms.
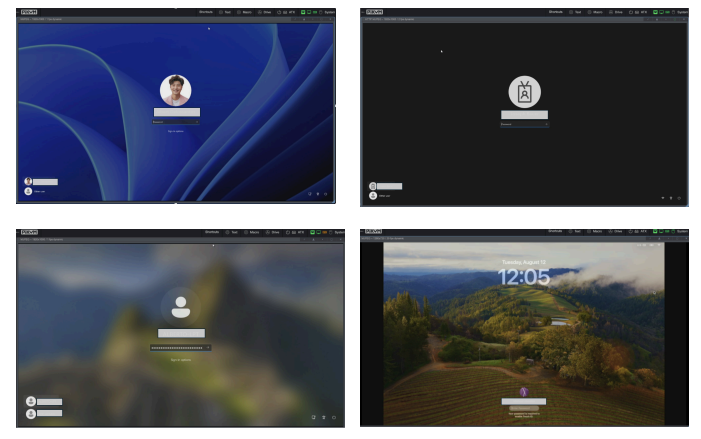
laptop farm (Source : Nisos).
The network also used Tailscale, a mesh VPN service, to build an encrypted private network among these devices, enabling remote command execution and data exfiltration over point-to-point connections.
Nisos identified around 40 devices on the network, with roughly 20 believed to be part of the laptop farm, each tied to different employee identities at different companies.
Researchers warn that this model allows DPRK IT workers to covertly earn foreign currency and gain access to sensitive corporate data worldwide.
Nisos stresses that companies should strengthen remote hiring controls with pre-employment OSINT screening, verification of identities and portfolios, and deeper technical interviews that can expose scripted or AI-assisted answers.
Without these measures, organizations risk unknowingly onboarding DPRK-linked contractors, creating openings for intellectual property theft, data breaches, and regulatory exposure.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.