North Korea’s cyber program is shifting from monolithic “families” to a modular, portfolio-style malware ecosystem designed to survive exposure, frustrate attribution, and keep operations running under constant pressure.
Years of sanctions, coordinated law-enforcement pressure, and rapid public disclosure of campaigns have forced Pyongyang to treat every tool as disposable.
Once-static implants are now built with short lifespans in mind, assuming that exposed loaders, C2 clusters, or payloads will be fingerprinted and neutralized quickly.
This has pushed the program toward resilience rather than longevity: malware is engineered to be burned and replaced, while the underlying operational structure continues largely unaffected.
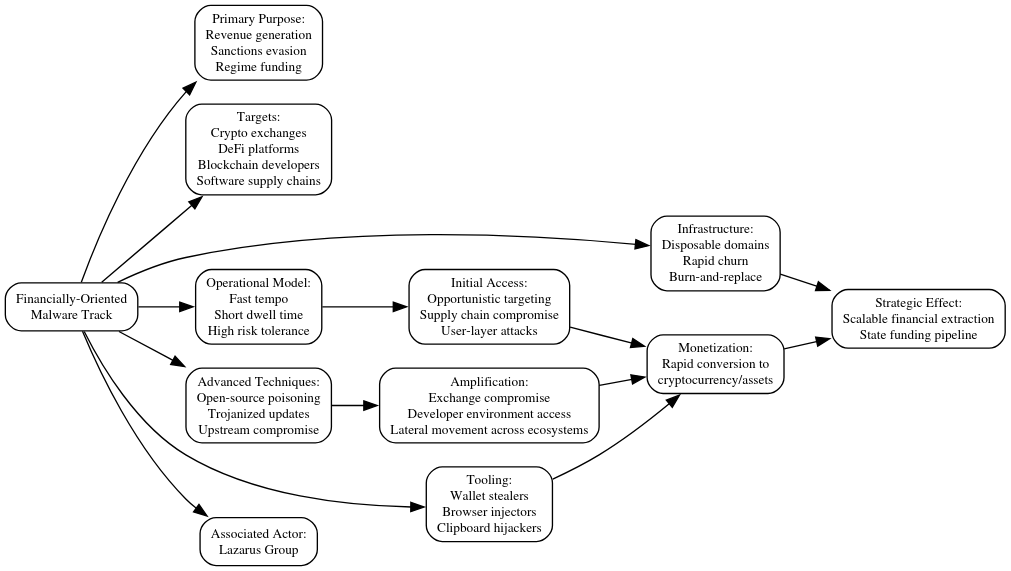
According to the report, the DPRK now runs parallel malware tracks aligned with espionage, financial theft, and disruption, each with its own tooling, infrastructure, and risk profile.
That structure is explicitly mission-aligned. Reporting on Lazarus, Kimsuky, and Andariel shows distinct development and deployment pipelines mapped to revenue generation, espionage, and disruptive operations, respectively.
When one track is compromised, the others can continue, limiting cascading impact and allowing planners to assume compromise as routine rather than exceptional.
Espionage Track: Low Noise, Long Dwell
Kimsuky-led espionage campaigns prioritize stealthy access to governments, defense, academia, and policy-adjacent organizations where information value is high but economic payoff is indirect.
These operations lean heavily on social engineering and tailored lures such as faux VPN invoices or government-themed documents to land script-heavy loaders instead of large binaries.
PowerShell and VBS-based chains, like recent three-stage loaders culminating in the HttpTroy backdoor, emphasize memory-resident access, credential theft, and mailbox surveillance over noisy lateral movement.
Once inside, operators increasingly abuse trusted cloud and collaboration platforms as C2 and staging layers, blending command traffic into normal enterprise workflows.
The result is a quiet collection posture that can persist for months, even as more aggressive DPRK operations execute elsewhere against unrelated targets.
The Lazarus-led financial track is optimized for speed and yield, converting intrusion into hard currency to offset sanctions and help fund weapons programs.
Here, infrastructure is explicitly disposable: domains, VPS nodes, and web shells churn rapidly, with operators expecting that successful cryptocurrency heists or upstream compromises will quickly attract attention.
Tooling is purpose-built for theft. Recent investigations highlight wallet stealers, browser injectors, and clipboard hijackers tuned for crypto workflows, alongside supply-chain compromises of developer tools and software updates.
By compromising exchanges, blockchain projects, or developer environments, Lazarus can move laterally across entire ecosystems, amplifying impact far beyond a single compromised host. Tool loss is acceptable as long as the financial return lands before the window closes.
Andariel-linked operations form a separate disruptive and coercive track, focused on delivering visible impact during periods of geopolitical tension rather than on profit or persistent access.
These campaigns favor ransomware-like tooling and wipers, rapid lateral movement, and domain-wide execution designed to maximize operational and psychological effect before controls can respond.
Despite visible fragmentation, technical and infrastructure “invariants” tie these tracks together. Analysts continue to observe recurring cryptographic routines, packing styles, and lightweight loader designs echoed across otherwise distinct DPRK families.
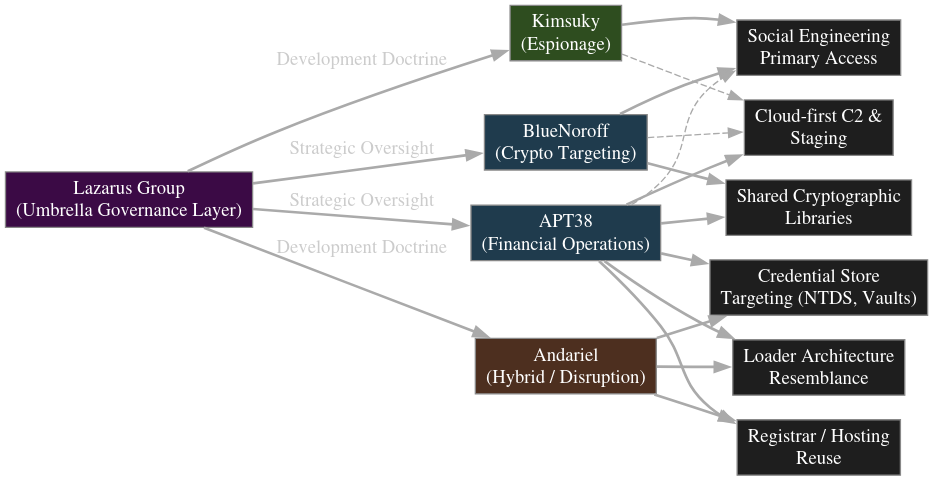
Infrastructure overlap is also evident at the registrar, hosting, and certificate level, even as front-end domains rotate aggressively.
Across all tracks, DPRK operators still rely primarily on social engineering, spear-phishing, and abuse of trusted cloud, developer, and collaboration ecosystems rather than exotic exploits.
This mirrors patterns seen in other APT ecosystems such as Russia’s APT29 and APT28, China’s APT41, and Iran’s Charming Kitten but DPRK stands out in how completely burn-and-replace logic is institutionalized across missions rather than confined to a single campaign type.
For defenders, a signature-first, family-centric model is no longer enough. DPRK toolchains are designed for rapid churn, making static indicators and single-family tracking increasingly brittle.
Effective detection now depends on behavioral analytics, identity and access monitoring, and deep telemetry from cloud and developer ecosystems that can surface credential abuse, anomalous movement, and abuse of trusted services regardless of the specific malware variant in play.
Viewing DPRK activity solely as espionage, or only as financial crime, risks missing entire mission tracks operating in parallel with different tooling and risk profiles.
The emerging picture is of a mature, centrally coordinated cyber portfolio in which modular malware is a consumable resource, not a crown jewel engineered to be sacrificed so that the broader system can endure.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.