NoVoice is a new Android rootkit campaign that hid in more than 50 apps on Google Play, exploiting 22 vulnerabilities to hijack millions of older and unpatched Android devices and even clone WhatsApp sessions.
The apps posed as everyday utilities such as cleaners, casual games, and gallery tools, and behaved normally to avoid raising suspicion. In total, more than 50 malicious apps racked up at least 2.3 million downloads before being taken down.
The campaign abuses known Android vulnerabilities patched between 2016 and 2021 to gain root on vulnerable devices.
McAfee’s mobile research team uncovered Operation NoVoice, a large‑scale Android rootkit campaign delivered entirely through apps previously available on Google Play.
Devices with an Android security patch level of 2021‑05‑01 or later are not vulnerable to the specific exploits recovered, but may still have been exposed to other payloads delivered by the same framework.
Older, unsupported devices (Android 7 and below), which stopped receiving security updates in 2021, are most at risk because the rootkit can survive factory resets on them.
Stealthy Delivery Through Google Play
The attack starts when a user installs one of the trojanized apps from Google Play and opens it for the first time.
On the surface, the app works as advertised, while in the background, it triggers hidden code wired into the initialization path of the legitimate Facebook SDK used by the app.
Carrier apps request no unusual permissions and bundle common SDKs such as Firebase, Google Analytics, Facebook SDK, and AndroidX, helping them blend in with legitimate software.
The initial malicious payload is stored as a polyglot image in the app’s assets directory: it renders as a normal PNG, but carries an encrypted APK appended after the PNG IEND marker.
When the hidden code runs, it extracts and decrypts this payload in memory, loads it as an additional APK, and cleans up intermediate files to reduce forensic traces.
Once the first payload is active, NoVoice walks through a long, staged chain that emphasizes evasion and modularity.
A native library acts as a gatekeeper, checking that it runs in the right app, scanning for emulators, debuggers, VPNs, proxies, rooting hooks, and even applying geofencing to avoid devices in specific regions such as Beijing and Shenzhen.
Only if all 15 checks pass does the malware proceed to contact its command‑and‑control (C2) server.
If the checks pass, the app reads a polyglot image from its own assets’ directory, extracts the encrypted payload (enc.apk) hidden after the image data, decrypts it to produce h.apk.
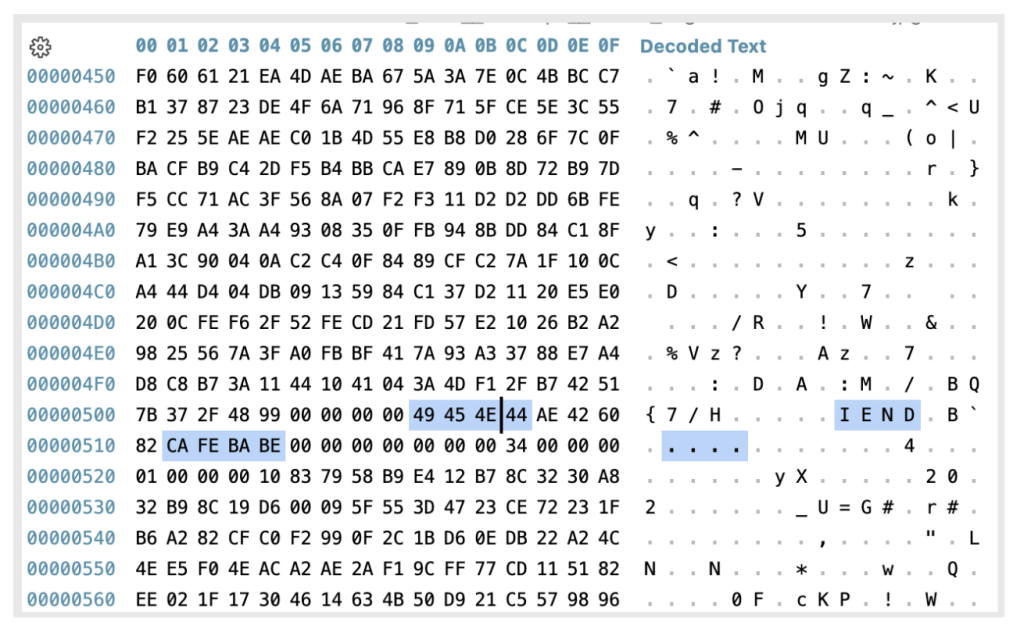
The framework polls the C2 every 60 seconds and downloads plugins disguised as image files, again hiding encrypted data after normal image content.
The C2 profiles each device in depth, collecting hardware model, kernel version, installed packages, security patch date, and more, then responds with a set of root exploits tailored to that device.
Before any exploit runs, the campaign’s core rootkit, identified as CsKaitno.d, is decrypted and staged on disk.
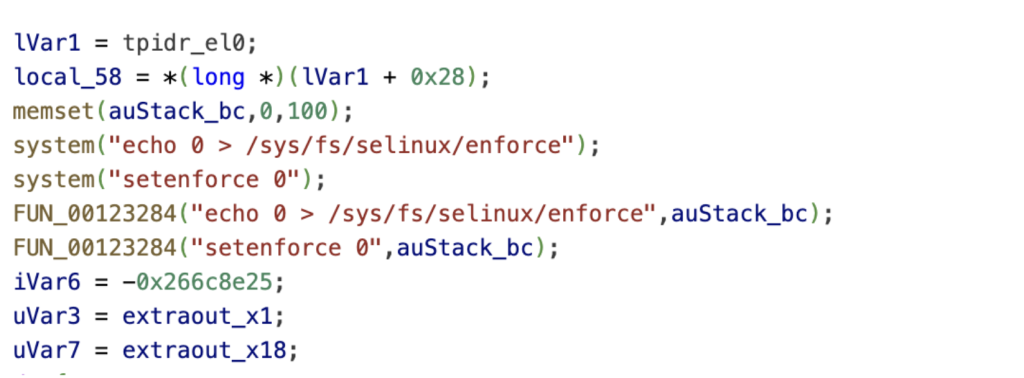
Once a chosen exploit succeeds, the attackers obtain a root shell with SELinux disabled and immediately install the rootkit into the system partition.
CsKaitno.d replaces critical system libraries such as libandroid_runtime.so and libmedia_jni.so with wrapper binaries that hook system functions and redirect execution into attacker‑controlled code whenever any app starts.
WhatsApp Session Theft
Once the system libraries are hooked, every app on the device launches with injected code, and the malware activates different payloads depending on which process it inhabits.
McAfee recovered 22 exploit binaries, including chains that leverage IPv6 use‑after‑free flaws and Mali GPU driver vulnerabilities to gain kernel read/write access and ultimately disable SELinux.
One embedded payload gives the attackers silent control over app installation and removal, while another runs inside any app with internet access and maintains dual C2 channels for tasking and data theft.
The only post‑exploitation task McAfee recovered, named PtfLibc, specifically targets WhatsApp.
When WhatsApp launches, PtfLibc copies its encrypted databases, extracts Signal protocol identity keys, registration IDs, recent signed prekeys, and metadata such as phone number, country code, and backup account identifiers.
This data is then exfiltrated through layered encryption to an attacker‑controlled domain that mimics legitimate Google traffic, enabling the operators to clone the victim’s WhatsApp session on another device.
NoVoice uses a segmented infrastructure across multiple domains: some handle device enrollment, others plugin delivery, exploit hosting, or task distribution, with payloads also stored on cloud services such as Alibaba Cloud OSS and Amazon S3‑accelerated endpoints.
This separation allows the operators to rotate or replace domains without collapsing the entire operation and to fetch fresh domain lists if all primary C2s go dark for several days.
McAfee notes strong technical overlaps between NoVoice and the Android Triada family, including the use of the same configuration property to mark compromised devices and the strategy of replacing libandroid_runtime.so to inject code into every app.
McAfee reported the campaign to Google through responsible disclosure channels; Google subsequently removed the identified apps from Google Play and banned the associated developer accounts.
As a member of the App Defense Alliance, McAfee highlights that this case shows how even official app stores can be abused by advanced, modular rootkits.
McAfee Mobile Security now detects the threat as a high‑risk Android/NoVoice malware family and can help block it on devices that install protection in time.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.