Open Source Security Foundation (OpenSSF), a group of open source software security specialists, is warning about a new phishing scam where hackers are targeting software developers using the Slack chat app.
These scammers pretend to be well-known leaders from the Linux Foundation, with the aim of getting developers to download malware that could give them total control over a computer. Their modus operandi is based on mimicking a legitimate Google Workspace flow, which redirects unsuspecting developers to a malicious page.
How the scam works
Researchers noted in the security advisory that the attack specifically targeted the TODO Group Slack workspace, which is a community for open source professionals. It starts with a simple private message supposedly from a community leader, but actually, it is the scammer.
The message is about a new, secret AI tool that can guess which bits of code will be accepted by a project before anyone even looks at them. To make it seem real, they say they are “only sharing this with a few people for now,” and even provide a fake email ([email protected]) and an access key (CDRX-NM71E8T) to look official.
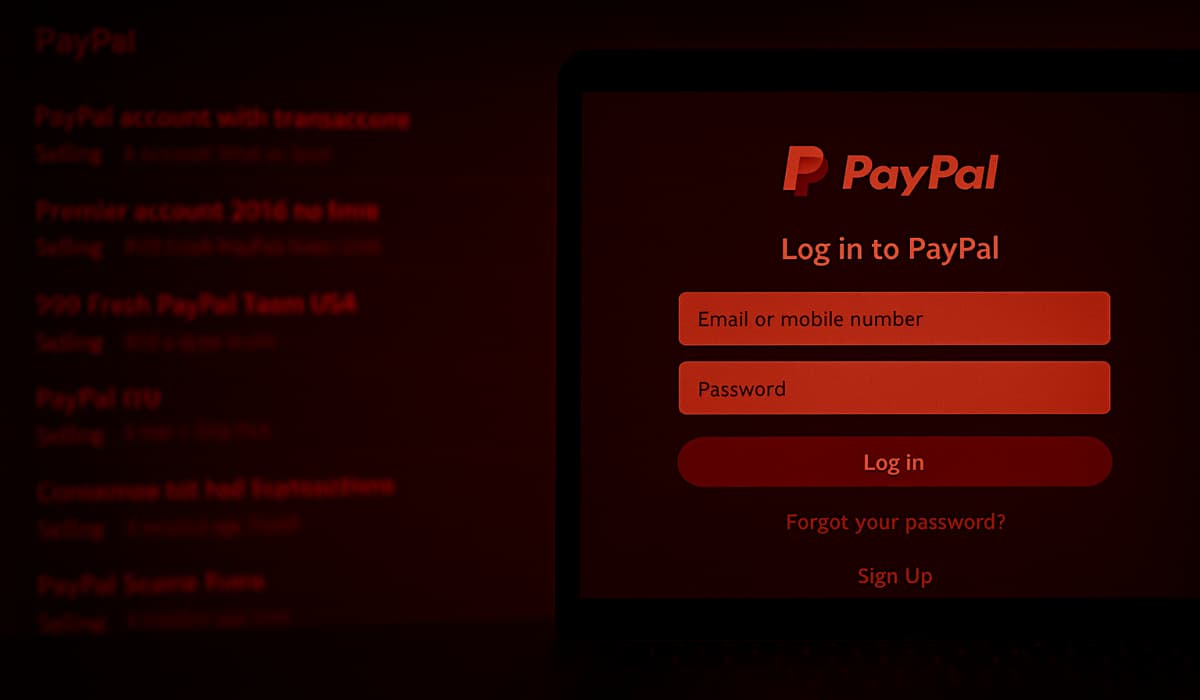
If a person believes the story, they are sent to a website that looks like a normal Google page. This site asks for an email and a special code. When the person enters these details, the site asks them to install a Google certificate, which is a malicious root certificate that lets hackers bypass security to spy on your private, encrypted web traffic and steal your data. Simply put, it lets the hackers monitor everything the person does online.
The now-deleted link used in the campaign: https://sites.google.com/view/workspace-business/join.
Different Risks for Mac and Windows
Further investigation revealed that the attack changes depending on the computer you use. On Apple Mac computers, the site tries to run a file called gapi, which can lead to a full system takeover. On Windows, the site tries to get the user to click a button to trust the fake certificate.
It must be noted that these tactics are similar to those used in a recent campaign against developers of other popular software like Node.js, and security researchers at Mandiant have linked these attacks to North Korean state-sponsored hackers.
Christopher Robinson, a top security expert at OpenSSF, says that people should never trust a message just because of the name or photo on the profile. He also gave some clear advice for anyone using these chat groups: “Do not install certificates from links,” as most real companies will never ask you to do that.
If you suspect that you clicked a suspicious link, immediately change all your passwords and always use extra login steps, like using MFA (multi-factor authentication) to keep your accounts safe.
Photo by Jon Tyson on Unsplash