A Pakistani threat actor group, Cosmic Leopard, has been conducting a multi-year cyber espionage campaign named Operation Celestial Force, targeting Indian entities.
Since 2018, they have used GravityRAT malware, initially for Windows and later for Android, which has been deployed through malicious documents and social engineering.
In 2019, they expanded their toolkit with HeavyLift, a malware loader distributed via fake installers, where each campaign within the operation is managed by custom “GravityAdmin” panels, highlighting the need for user education on cyber hygiene and implementing defense-in-depth security models.
Operation Celestial Force, a cyberespionage campaign targeting Indian entities, uses two main infection vectors: spearphishing emails with malicious documents and social engineering on social media to trick targets into downloading malware.
Free Webinar on API vulnerability scanning for OWASP API Top 10 vulnerabilities -> Book Your Spot
The malware suite includes GravityRAT, a remote-access Trojan for Windows and Android, and HeavyLift, a Windows malware loader.
The operators manage these tools with a multi-paneled administrative interface called GravityAdmin.
.webp)
GravityAdmin is a malware framework used to manage various malicious campaigns. The panel binary authenticates users with a server and retrieves a token to communicate with campaign-specific C2 servers.
Different campaigns target different platforms (Windows and Android) and deploy different malware families (GravityRAT and HeavyLift).
There are infrastructure overlaps between campaigns, such as sharing malicious domains to host payloads or maintaining infected machine lists.
.webp)
GravityRAT, a multi-platform remote access trojan, first targeted Windows machines but has since expanded to Android devices, which are likely used by Pakistani actors against Indian targets and spread through fake app websites and social media.
New variants steal user data (SMS, call logs, files), device information (IMEI, location), and even associated email addresses.
The malware communicates with hidden command-and-control servers and can wipe data on infected devices.
.webp)
HeavyLift, an Electron-based malware loader, is disguised as an installer and deployed through social engineering, which communicates with C2 servers to steal system information (including username, MAC address, and OS version) and download malicious payloads.
These payloads are executed persistently on the compromised system using crontab for macOS and scheduled tasks for Windows. The malware also implements anti-analysis techniques to evade detection in virtual environments.
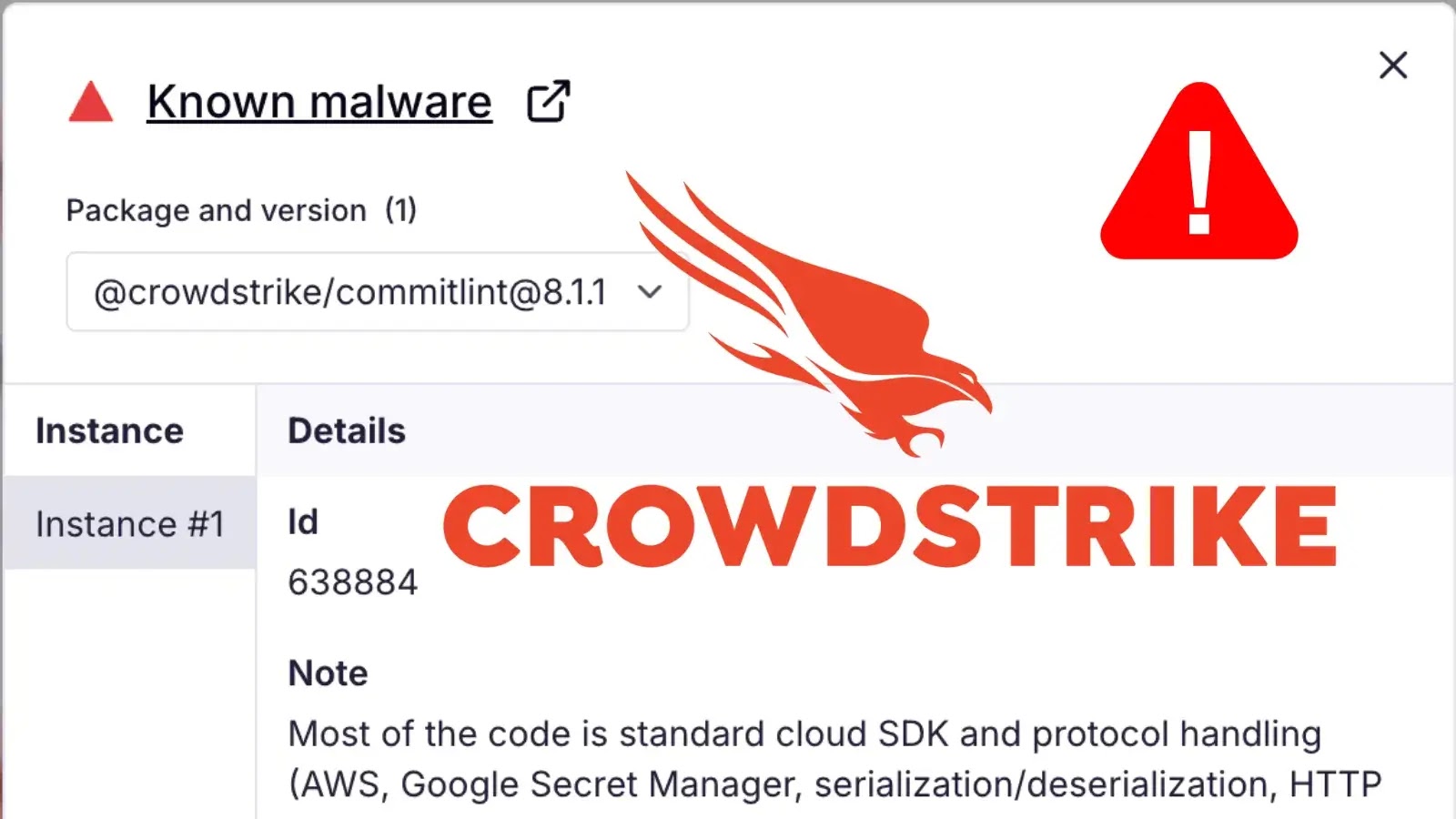
The provided Indicators of Compromise (IOCs) by Cisco Talos are hashes of malicious files, domains, and URLs that are associated with Android malware, including HeavyLift, GravityRAT Android, and GravityAdmin.
The URLs contain suspicious parameters and may be used to exploit vulnerabilities on Android devices, and by checking these IOCs against files, network traffic, and URLs, security researchers can identify potential infections.
Free Webinar! 3 Security Trends to Maximize MSP Growth -> Register For Free