Cybersecurity frameworks such as NIST CSF, ISO/IEC 27001, and the CIS Critical Security Controls have significantly contributed to standardizing security practices across industries. They provide a common language, define control domains, and help organizations reason about risk in a structured way.
However, in real-world environments—particularly small and mid-sized organizations—the challenge is rarely a lack of frameworks. The challenge is execution.
Security leaders often operate under constraints that are not adequately reflected in theoretical models: limited budgets, small teams, heterogeneous infrastructures, legacy systems, and competing business priorities. In these contexts, cybersecurity maturity is not determined by how many controls are documented, but by how effectively a small set of controls can be deployed, maintained, and recovered from when failures inevitably occur.
Cyber resilience, therefore, must be understood not as a checklist, but as an operational capability.
Why Traditional Security Models Fail in Constrained Environments
Many security initiatives fail not because the controls are wrong, but because they are introduced in ways that exceed the organization’s operational capacity.
Common failure patterns include:
- Vendor-driven complexity: Tool sprawl increases attack surface and operational burden.
- Control overload: Attempting to implement dozens of controls simultaneously dilutes effectiveness.
- Compliance-first mindset: Meeting audit requirements without improving real-world recovery capability.
- Fragile architectures: Systems designed to prevent failure rather than to recover from it.
In constrained environments, every control must justify not only its security value, but also its operational cost. A control that cannot be maintained, monitored, or recovered from under stress conditions actively reduces resilience.
Core Principles of an Operational Cyber Resilience Model
Based on years of hands-on experience designing and operating security programs in resource-constrained environments, several principles consistently emerge as prerequisites for operational cyber resilience.
- Minimum Viable Security
Not every control needs to be implemented at once. Organizations should identify the smallest set of controls that meaningfully reduce risk and expand from there.
- Failure-Expected Design
Assume that breaches, misconfigurations, and outages will occur. The goal is not perfect prevention, but rapid detection and recovery.
- Automation Over Optimization
Automated, “good enough” controls outperform manually optimized controls that depend on scarce human resources.
- Recoverability as a Primary Control
Backups, system rebuild procedures, and configuration reproducibility are not secondary controls—they are central to resilience.
- Repeatability and Simplicity
Controls must be easy to redeploy, audit, and replicate across environments.
These principles shift the focus from theoretical completeness to operational survivability.
Translating Principles Into Practice: A Practitioner Framework
Translating these principles into actionable security controls requires a framework that prioritizes execution over abstraction.
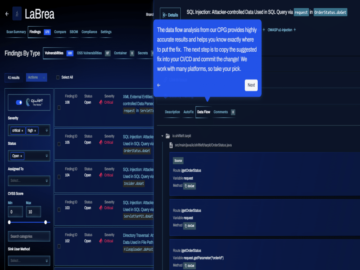
One example of such an approach is the S4T framework, an open-source initiative designed to operationalize core cybersecurity and resilience principles in environments with real-world constraints. Rather than competing with established standards, the framework aligns with them while focusing explicitly on implementation feasibility.
At a high level, the framework organizes security efforts around a small number of technical pillars:
- System Hardening: Secure baseline configurations for operating systems, hypervisors, and network devices.
- Network Segmentation: Logical separation of assets to contain lateral movement.
- Backup and Recovery: Automated, tested, and immutable backup strategies.
- Monitoring and Logging: Centralized visibility using lightweight and open tooling.
- Incident Response Readiness: Predefined procedures focused on containment and recovery rather than attribution.
The framework’s open-source nature allows organizations to adapt it to their infrastructure while maintaining transparency and avoiding vendor lock-in. More importantly, each pillar is designed to be deployable independently, enabling incremental maturity improvements without requiring large upfront investments.
Lessons Learned From Real-World Implementations
Across multiple environments, several recurring lessons emerge when applying an operational resilience mindset.
Fewer Controls, Better Outcomes
Organizations that implemented a small number of well-integrated controls consistently achieved better security outcomes than those attempting broad control coverage.
Backup Strategy Defines Survival
The difference between a security incident and a business-ending event is often the ability to restore systems quickly and reliably. Backup maturity is one of the strongest predictors of resilience.
Segmentation Beats Detection Alone
Preventing unrestricted lateral movement limits blast radius even when detection fails or is delayed.
Documentation Enables Recovery
Clear, concise documentation—focused on rebuild and recovery—proves more valuable during incidents than complex policies.
Tooling Is Secondary to Process
Tools support resilience, but process determines whether controls work under pressure.
Strategic Takeaways for CISOs and Security Leaders
Cyber resilience is not achieved by acquiring more tools or adopting more frameworks. It is achieved by aligning security controls with the organization’s operational reality.
For security leaders operating under constraints, several strategic takeaways stand out:
- Prioritize time-to-recover over theoretical prevention.
- Design controls that can be re-deployed under stress.
- Treat recoverability and segmentation as first-class security objectives.
- Favor open, transparent, and repeatable approaches over opaque complexity.
Operational cyber resilience is ultimately a cultural and architectural choice. Organizations that embrace simplicity, automation, and recovery-oriented design are better positioned to withstand the inevitability of cyber incidents.
Conclusion
The future of cybersecurity effectiveness lies not in ever-expanding control catalogs, but in the ability to operationalize a small set of resilient, repeatable, and recoverable security practices.
Frameworks provide guidance, but practitioners must translate that guidance into architectures that survive real-world conditions. Approaches such as the S4T framework demonstrate that it is possible to bridge the gap between theory and execution—particularly when security is treated as an operational discipline rather than a compliance exercise.
Cyber resilience is not about avoiding failure. It is about ensuring that when failure occurs, the organization continues to operate.
About the Author
Diego Neuber is a Chief Information Security Officer (CISO) and founder of Disatech, a Brazilian company specializing in IT security, training, audits, and secure infrastructure solutions. With over 14 years of experience in cybersecurity, he currently serves as CISO for multiple organizations across diverse industries.
He is a Senior Member of IEEE, an active article contributor and reviewer for international cybersecurity publications, and a frequent speaker at professional and academic events. Diego also serves as a judge for the Globee® Awards for Cybersecurity and the German Stevie® Awards, recognizing excellence and innovation in the cybersecurity field.
Diego can be reached at [email protected], on LinkedIn at linkedin.com/in/diegoneuber, and through his company website: www.disatech.com.br.