The analysis of nearly 20 million information-stealing malware logs sold on the dark web and Telegram channels revealed that they had achieved significant infiltration into business environments.
Information stealers are malware that steals data stored in applications such as web browsers, email clients, instant messengers, cryptocurrency wallets, FTP clients, and gaming services. The stolen information is packaged into archives called ‘logs,’ which are then uploaded back to the threat actor for use in attacks or sold on cybercrime marketplaces.
The most prominent information-stealing families are Redline, Raccoon, Titan, Aurora, and Vidar, offered to cyber criminals on a subscription-based model, allowing them to conduct malware campaigns that steal data from infected devices.
While information stealers primarily target careless internet users who download software, such as cracks, warez, game cheats, and fake software from dubious sources, it has also been found to have a massive impact on corporate environments.
This is because employees use personal devices for work or access personal stuff from work computers, resulting in many info-stealer infections stealing business credentials and authentication cookies.
More specifically, as cybersecurity firm Flare explains in a new report shared with BleepingComputer, there are approximately 375,000 logs containing access to business applications such as Salesforce, Hubspot, Quickbooks, AWS, GCP, Okta, and DocuSign.
More specifically, Flare found the following in the examined stealer logs:
- 179,000 AWS Console credentials
- 2,300 Google Cloud credentials
- 64,500 DocuSign credentials
- 15,500 QuickBooks credentials
- 23,000 Salesforce credentials
- 66,000 CRM credentials
In addition to the above, there are about 48,000 logs that include access to “okta.com,” an enterprise-grade identity management service used by organizations for cloud and on-premise user authentication.
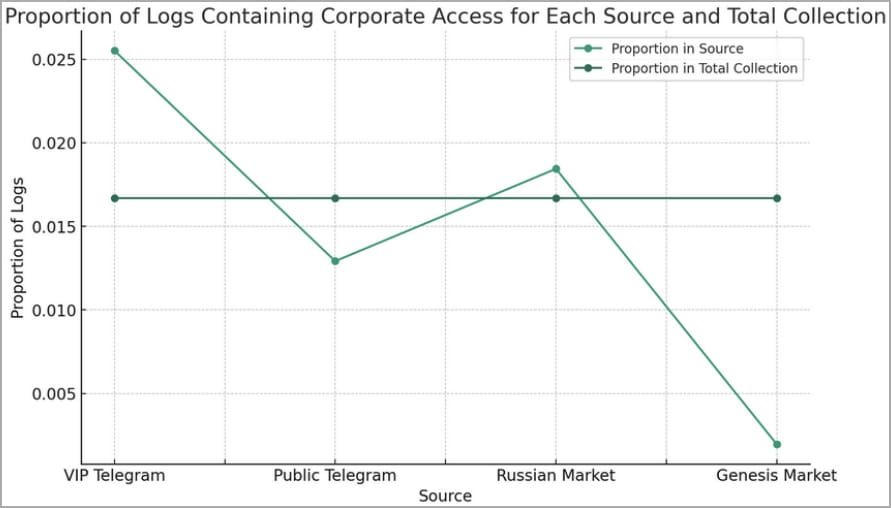
Most of these logs (74%) were posted on Telegram channels, while 25% were seen on Russian-speaking marketplaces, like the ‘Russian Market.’
“Logs containing corporate access were over-represented on Russian Market and VIP Telegram channels, indicating that the methods attackers use to harvest logs may incidentally or intentionally have more corporate targeting,” describes the Flare report.
“Additionally, public Telegram channels may deliberately post lower value logs, saving high-value logs for paying customers.”
Flare also found more than 200,000 stealer logs containing OpenAI credentials, which is double the amount that Group-IB reported recently and constitutes a risk for leaking proprietary information, internal business strategies, source code, and more.
Corporate credentials are considered “tier-1” logs, making them particularly high-valued in the cybercrime underground, where they are sold on private Telegram channels or forums like Exploit and XSS.
That value is derived from the potential profit cybercriminals can make by leveraging compromised credentials to access CRMs, RDP, VPNs, and SaaS applications and then using that access to deploy stealthy backdoors, ransomware, and other payloads.
“Based on evidence from the dark web forum Exploit in, we rate it as highly likely that initial access brokers are using stealer logs as a principal source to gain an initial foothold to corporate environments that can then be auctioned off on top-tier dark web forums,” explains Flare researcher Eric Clay.
It is recommended that businesses minimize the risk of info-stealer malware infections by imposing the use of password managers, enforcing multi-factor authentication, and setting strict controls on personal device use.
Furthermore, employees should be trained to identify and avoid common infection channels such as malicious Google Ads, YouTube videos, and Facebook posts.