Over 400,000 sites at risk as hackers exploit Breeze Cache plugin flaw (CVE-2026-3844)

Attackers exploit a Breeze Cache flaw (CVE-2026-3844) to upload files without login. Wordfence researchers detected over 170 attacks.
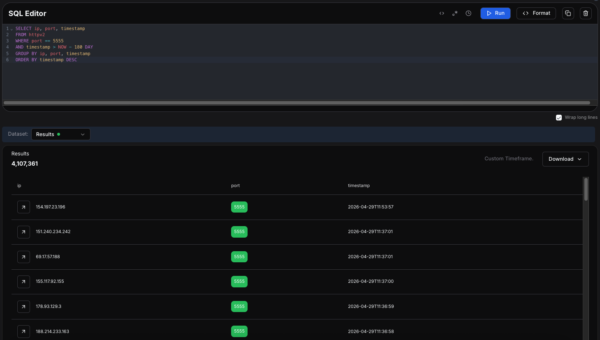
Threat actors are exploiting a critical flaw, tracked as CVE-2026-3844 (CVSS score of 9.8), in the Breeze Cache WordPress plugin, allowing them to upload files to a server without authentication. The vulnerability has already been used in over 170 attack attempts detected by Wordfence.
Breeze Cache is a free WordPress plugin developed by Cloudways that improves website speed and performance. It offers page and browser caching, file minification, Gzip compression, and CDN integration, helping reduce load times and optimize overall site delivery. The plugin is currently installed on over 400,000 websites.
The security researcher Hung Nguyen (bashu) discovered the vulnerability.
“The Breeze Cache plugin for WordPress is vulnerable to arbitrary file uploads due to missing file type validation in the ‘fetch_gravatar_from_remote’ function in all versions up to, and including, 2.4.4. This makes it possible for unauthenticated attackers to upload arbitrary files on the affected site’s server which may make remote code execution possible.” reads the report published by Wordfence. “The vulnerability can only be exploited if “Host Files Locally – Gravatars” is enabled, which is disabled by default.”
Wordfence researchers say the flaw stems from missing file-type validation in the ‘fetch_gravatar_from_remote’ function, allowing unauthenticated attackers to upload arbitrary files. This can lead to remote code execution and full site takeover. According to the advisory, the exploitation is only possible if the “Host Files Locally – Gravatars” option is enabled. The issue affects Breeze Cache up to version 2.4.4 and is fixed in version 2.4.5.
Since the vulnerability is actively exploited, Breeze Cache users should update to the latest version immediately or disable the plugin temporarily.
At the time of this writing, Wordfence reported that it had blocked 3,936 attacks targeting this vulnerability in the past 24 hours.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Breeze Cache plugin)