ClearFake Infects 9,300 Sites, Uses Fake reCAPTCHA and Turnstile to Spread Info-Stealers
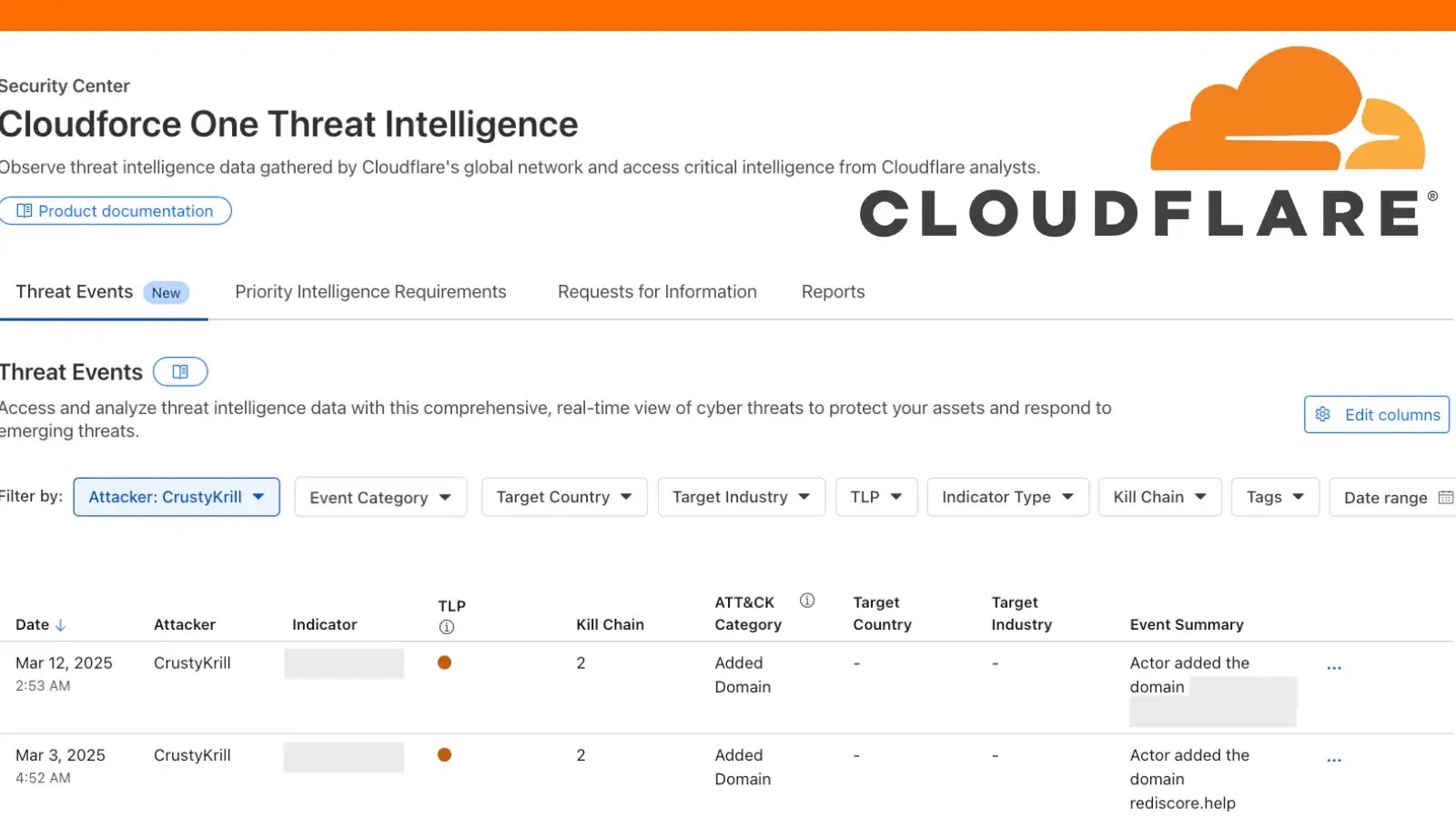
Mar 19, 2025Ravie LakshmananCloud Security / Web Security The threat actors behind the ClearFake campaign are using fake reCAPTCHA or Cloudflare Turnstile verifications as lures…