A newly observed Linux backdoor technique, dubbed Pam, is exploiting the flexibility of Pluggable Authentication Modules (PAM) to capture SSH credentials and maintain persistence on compromised systems stealthily.
Since its introduction in 1991 by Linus Torvalds, Linux has been designed for simplicity, modularity, and flexibility.
This modular architecture allows administrators to customize nearly every component, from networking and authentication to system management and security controls.
While this design has made Linux one of the most secure and widely adopted operating systems, it also introduces unique attack surfaces when misused.
Security researchers from the Group-IB DFIR team have uncovered a novel persistence technique that leverages PAM’s modular nature, particularly the pam_exec module, to execute malicious code during authentication workflows.
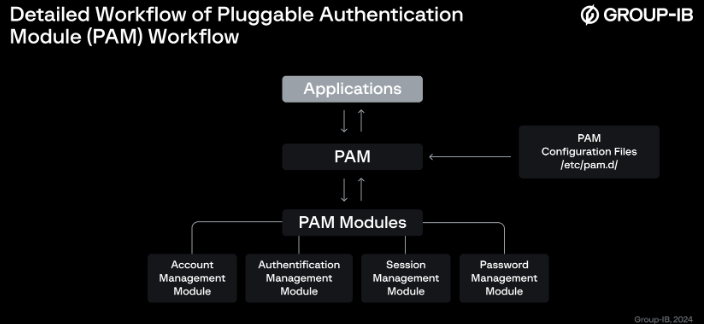
PAM acts as an intermediary authentication layer used by applications such as sshd, login, passwd, and su. It separates authentication logic from applications, enabling flexible and centralized control over access policies.
The framework consists of four module types: authentication, account management, password handling, and session control.
Each module operates based on control flags such as required, requisite, sufficient, and optional, which determine how authentication results are processed.
Despite its advantages, PAM introduces risk because it does not store passwords but processes authentication data, sometimes in plaintext.
Applications such as su, passwd, login, gdm, sshd, and ftpd can all utilize PAM. PAM provides each of these applications with a specialized library to verify user identities and determine whether they have the necessary permissions to access resources.
If attackers gain the ability to modify PAM configurations, they can insert malicious modules or scripts to intercept credentials or establish backdoors.
Pam Backdoor Targets Linux Systems
The pam_exec module is intended to execute external commands during authentication events. Administrators often use it for legitimate purposes such as triggering alerts or scripts after password changes.
However, attackers can weaponize this functionality. By inserting a malicious entry into PAM configuration files like /etc/pam.d/sshd, threat actors can force the system to execute a hidden script during SSH authentication attempts.
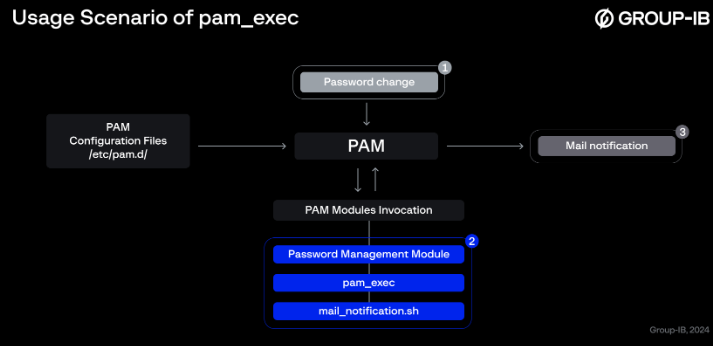
In the PamDOORa attack scenario, a malicious script is silently triggered using pam_exec whenever an SSH login attempt occurs.
The script collects sensitive data such as usernames, timestamps, and environment variables including PAM_USER, PAM_RHOST, and PAM_SERVICE.
This data is then exfiltrated to a remote command-and-control server using tools like netcat (nc) over a predefined port.
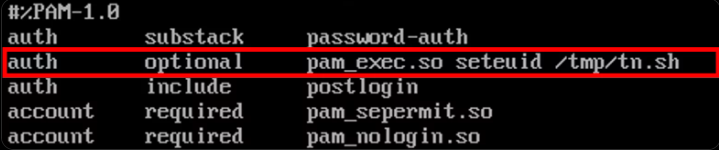
Notably, the PAM configuration is set with the optional control flag, ensuring the malicious execution does not disrupt the authentication flow or raise suspicion.
One of the most concerning aspects of this technique is its stealth. Even when SSH authentication fails, the malicious script still executes and transmits data externally.
Because PAM handles authentication internally, these actions leave minimal traces in system logs. Logs typically only record failed login attempts, masking the underlying data exfiltration activity. This significantly complicates forensic investigations and detection efforts.
For example, a compromised system may show repeated failed SSH logins in logs, while in reality, each attempt triggers silent credential harvesting in the background.
The Pam technique highlights how legitimate Linux features can be abused for persistent and covert attacks. Its reliance on native tools and standard configurations makes detection particularly challenging for traditional security monitoring solutions.
Organizations running Linux servers, especially those exposed to external networks, should take proactive steps to mitigate this risk.
This includes regularly auditing PAM configuration files, monitoring unauthorized changes in /etc/pam.d/, restricting script execution permissions, and implementing file integrity monitoring solutions.
Additionally, enabling stricter logging, deploying endpoint detection tools, and leveraging SELinux or AppArmor policies can help limit unauthorized modifications and execution paths.
As Linux continues to dominate enterprise and cloud environments, attacks like PamDOORa serve as a reminder that even trusted and secure frameworks can become attack vectors when misconfigured or compromised.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.