Paranoid about getting hacked? #shorts

Source link
Related Articles
All Mix →Burp Scanner can now crawl static sites between 6x – 9x faster | Blog
Table of Contents Crawler? What's that? The problem with overthinking Benchmarking the new strategy – how much faster is it? In short: using the improved…
Cybernoz
4 min read
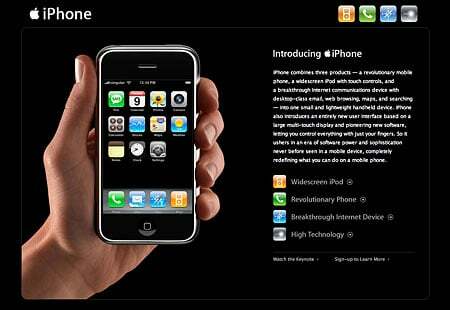
The Aesthetics vs. Features iPhone Debate
Ok, there are two basic arguments here. I’ll summarize them below: Features Rule Everything (Anti-iPhone)Look, it doesn’t matter how cool people think the graphics or…
Cybernoz
2 min read
Does “Erase All Content and Settings” actually wipe user data on macOS?
Does “Erase All Content and Settings” actually wipe user data on macOS? Source link
Cybernoz
1 min read
how to find more vulnerabilities using Google search
Table of Contents Filtering in-page keywords: Filtering by page title Filtering by URL Filtering by file extension Filtering by file type Filtering by date (finding…
Cybernoz
5 min read