A new PlugX USB worm variant is driving fresh infection waves across several continents, using DLL sideloading and stealthy USB-based propagation to evade detection.
First observed in Papua New Guinea in August 2022, the same strain resurfaced months later not only in the Pacific Rim but also in Ghana, Mongolia, Zimbabwe, and Nigeria, underscoring a fragmented but global spread pattern.
PlugX is a long‑running remote access Trojan (RAT) of Chinese origin, frequently deployed by espionage‑aligned intrusion sets and often delivered via DLL sideloading of legitimate executables.
In this campaign, infections in geographically distant but localized clusters suggest operators are leveraging targeted distribution, likely via physical media or controlled USB seeding, rather than broad phishing.
Researchers note that this variant introduces a new payload and uses callbacks to a command‑and‑control (C2) server previously considered only loosely associated with PlugX activity.
The new variant’s callbacks to C2 infrastructure at 45.142.166[.]112 aligns with earlier research that tentatively linked this endpoint to “other PlugX” activity, and recent analysis strengthens the link to the PKPLUG/Mustang Panda threat actor.
How DLL sideloading and USB spread work
The worm abuses a legitimate Avast executable (AvastSvc.exe) that is vulnerable to DLL sideloading, pairing it with a malicious DLL (wsc.dll) and an encrypted PlugX payload.
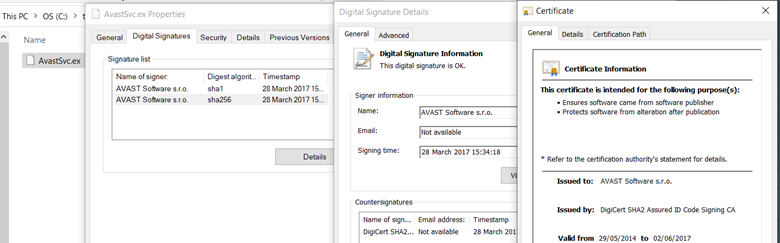
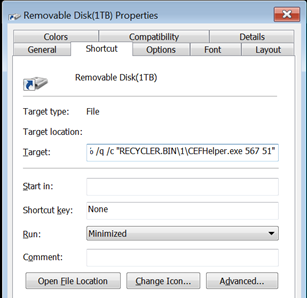
On infected systems and removable drives, the malware deploys components into a RECYCLER.BIN directory and renames the trusted loader (for example, to CEFHelper.exe) to disguise it as a benign helper process.
When users double‑click what appears to be a removable drive shortcut, Windows actually executes the renamed AvastSvc executable, which then sideloads the rogue DLL and decrypts the PlugX backdoor.
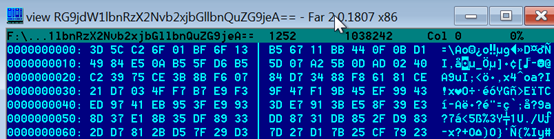
To support data theft and lateral movement, the worm drops a batch script (tmp.bat) that runs a series of discovery commands including ipconfig, systeminfo, tasklist, and netstat, collecting results into an obfuscated file whose name is base64‑encoded (for example, “c3lzLmluZm8” for sys.info).
PlugX then searches for documents with extensions such as .doc, .docx, .xls, .xlsx, .ppt, .pptx, and .pdf, up to a per‑file size limit, encrypting and storing copies in RECYCLER.BIN with base64‑encoded file names for later exfiltration.
On removable media, the worm uses Windows shortcut tricks and filesystem attributes to appear invisible to casual users.
Old USB worm tactics, renewed at scale
The drive looks empty except for a single “removable disk” entry, which is actually a shortcut that launches the sideloaded loader rather than opening storage content.
All malicious files and stolen data are marked as hidden and system, and a crafted desktop.ini associates RECYCLER.BIN with the Windows Recycle Bin shell extension so it even displays normal recycle‑bin content from the host system, further masking the backdoor’s presence.
While USB worms fell out of favor as cloud storage and email became dominant vectors, PlugX’s USB‑aware variants show advanced persistent threat (APT) actors are reviving removable‑media propagation for persistence and for reaching air‑gapped or tightly segmented networks.
Recent sinkholing efforts and telemetry demonstrate that self‑spreading PlugX USB malware families remain active years after initial deployment, with tens of thousands of infected public IPs still beaconing daily.
The latest DLL‑sideloading PlugX USB worm underlines how mature toolsets can be repackaged with minimal changes in loader and infrastructure to create fresh, geographically dispersed campaigns.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.