Three popular WordPress plugins with tens of thousands of active installations are vulnerable to high-severity or critical SQL injection vulnerabilities, with proof-of-concept exploits now publicly available.
SQL injection is a website security flaw that allows attackers to input data into form fields or via URLs that modify legitimate database queries to return different data or modify a database.
Depending on the website code being vulnerable to a SQL injection flaw, an attacker could modify or delete data to a site, inject malicious scripts, or gain full access to the website.
Proof of Concept exploits released
The three vulnerable plugins were discovered by Tenable security researcher Joshua Martinelle, who reported them responsibly to WordPress on December 19, 2022, along with proofs of concept (PoCs).
The authors of the plugins released security updates to address the issues in the following days or weeks, so all problems have been fixed now, and those running the latest available version are no longer vulnerable.
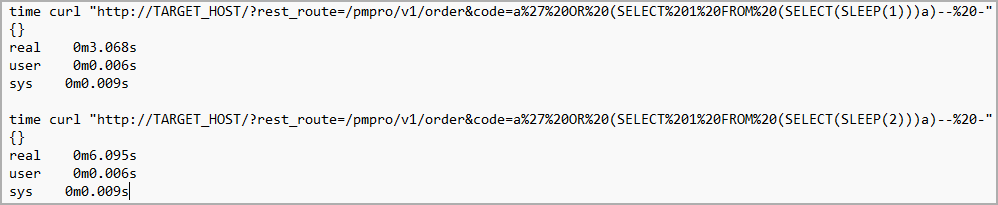
Yesterday, the researcher disclosed technical details about each vulnerability with proof of concept exploits using the SLEEP function to demonstrate how the flaws work.
The first plugin that was found to be vulnerable to SQL injection is ‘Paid Memberships Pro,’ a membership and subscriptions management tool used in over 100,000 websites.
“The plugin does not escape the ‘code’ parameter in the /pmpro/v1/order REST route before using it in a SQL statement, leading to an unauthenticated SQL injection vulnerability,” reveals Tenable’s post.
The flaw is tracked as CVE-2023-23488, receiving a CVSSv3 severity rating of 9.8 (critical), and it affects all versions of the plugin older than 2.9.8. Paid Memberships Pro fixed the vulnerability on December 27, 2022, with the release of version 2.9.8.
The second WordPress add-on vulnerable to SQL injection is ‘Easy Digital Downloads,’ an e-commerce solution for selling digital files with over 50,000 active installations.
“The plugin does not escape the ‘s’ parameter in the ‘edd_download_search’ action before using it in a SQL statement, leading to an unauthenticated SQL injection vulnerability,” explains Tenable.
“The vulnerable part of the code corresponds to the ‘edd_ajax_download_search()’ function of the ‘./includes/ajax-functions.php’ file.”
The vulnerability is tracked as CVE-2023-23489 and has received a CVSSv3 severity rating of 9.8, categorizing it as critical. The flaw impacts all versions below 3.1.0.4, released on January 5, 2023.
Finally, Tenable discovered CVE-2023-23490, a ‘high-severity’ SQL injection flaw in ‘Survey Marker,’ a WordPress plugin used by 3,000 websites for surveys and market research.
The flaw received a severity rating of 8.8, according to the CVSS v3, because the attacker has to be authenticated as at least a subscriber to exploit it.
However, this prerequisite is usually easy to fulfill, as many websites allow visitors to register as members.
Survey Marker was the quickest vendor to respond to Tenable’s SQL injection discovery, releasing a fixing update on December 21, 2022, with version 3.1.2.
While all of these plugins were vulnerable to SQL injection, and proof of concept exploits were released, Tenable did not share what impact they could lead if exploited in attacks.
However, as the bugs are categorized as critical, it is recommended that all sites using these plugins upgrade to the latest version.







