A financially motivated hacking group is targeting Canadian employees with a sophisticated campaign designed to covertly redirect their salary payments into attacker-controlled bank accounts, Microsoft researchers discovered.
SEO poisoning and malvertising + phishing + AiTM
The group, which Microsoft tracks as Storm-2755, begins by poisoning search engine results and running malicious ads against generic queries like “Office 365”, or even common misspellings like “Office 265.”
Victims who click through land on a convincing but fake Microsoft 365 login page that both steals their login credentials and proxies the entire authentication session in real time, capturing the session token issued after login.
“Storm-2755 leveraged version 1.7.9 of the Axios HTTP client to relay authentication tokens to the customer infrastructure which effectively bypassed non-phishing resistant MFA and preserved access without requiring repeated sign ins. This replay flow allowed Storm-2755 to maintain these active sessions and proxy legitimate user actions, effectively executing an AiTM attack,” Microsoft’s incident responders explained.
For most victims, the attacker just maintained this quiet background access. But for a smaller number of accounts, they also changed the victim’s password and MFA settings. That way, even after the original stolen token expired or was revoked, they still “owned” the account.
The real goal of the campaign
Once inside the victim’s email account, the attackers search the compromised mailbox for references to payroll, HR, and finance, then send an email from the victim’s account to the organization’s HR staff requesting a “direct deposit” change.
Because the email comes from the employee’s real address, HR has no reason for suspicion and if they comply and file the change, the employee’s next paycheck will go to the attacker’s bank account instead the victim’s-
Before sending the email to HR or the finance department, the attackers create an inbox rule that silently buries any HR replies containing words like “bank” or “direct deposit” in a hidden folder, so the victim won’t see them and raise the alarm.
“Where Storm-2755 was unable to successfully achieve changes to payroll information through user impersonation and social engineering of HR personnel, we observed a pivot to direct interaction and manual manipulation of HR software-as-a-service (SaaS) programs such as Workday,” Microsoft added.
In one successful attack, Storm-2755 manually signed in to Workday as the victim to update banking information and that employee suffered direct financial loss.
How to stymie “payroll pirate” attacks
This particular campaign was focused on compromising employees in Canada, but similar campaigns are constantly mounted to target employees in other countries and/or working in companies operating in specific economic sectors.
Microsoft recommends using FIDO2/WebAuthn passkeys as the second authentication factor, as they bind authentication to the legitimate origin site and cannot be intercepted by an AiTM proxy the way traditional push or OTP-based MFA can.
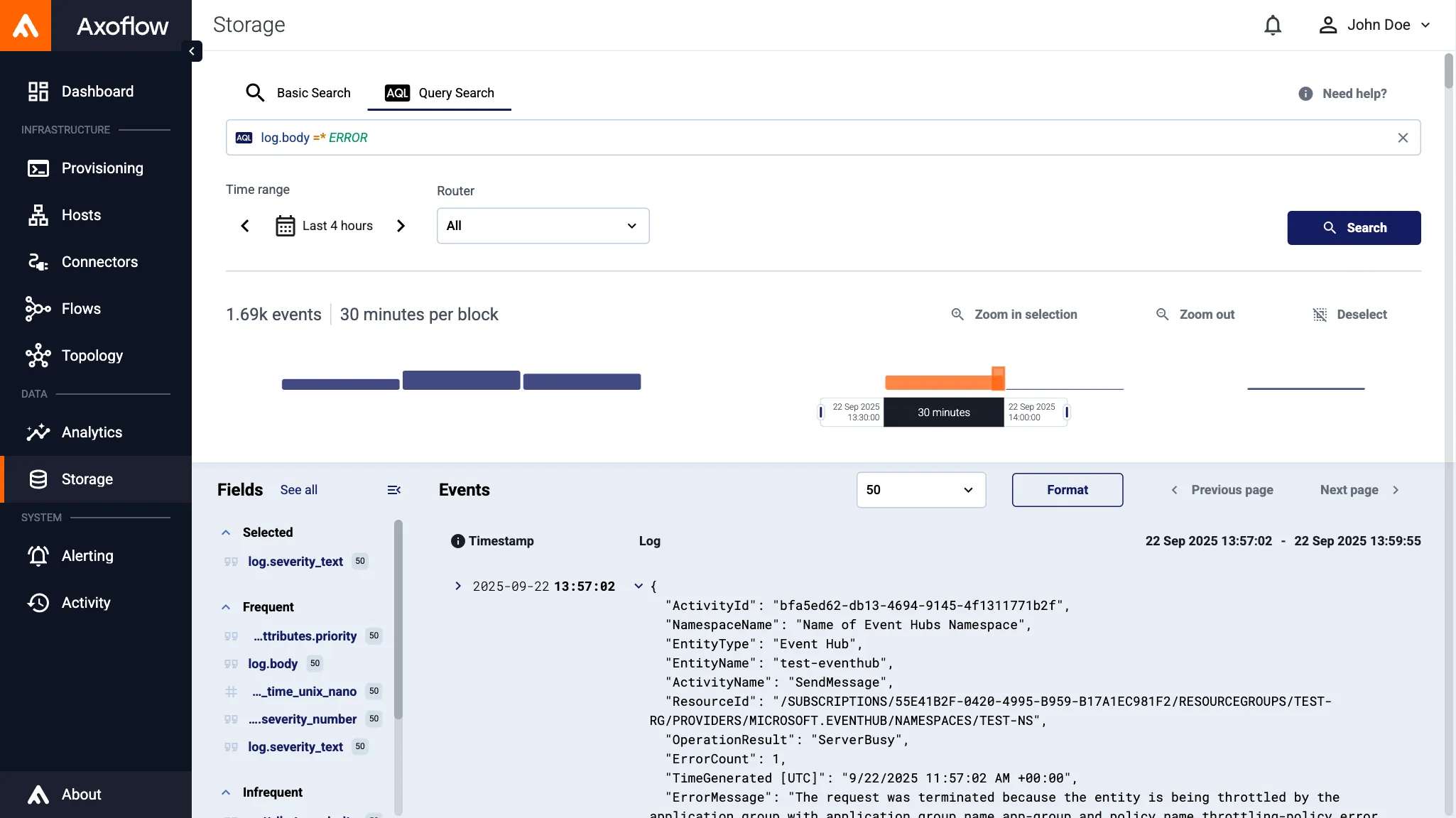
Beyond that, organizations should monitor for the Axios user-agent appearing in sign-in logs, watch for non-interactive sign-ins to OfficeHome repeating on roughly 30-minute intervals, and alert on newly created inbox rules that filter on financial keywords.
HR and payroll teams should also adopt out-of-band verification (e.g., a phone call or in-person confirmation) for any direct deposit change requests.
Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!
![]()