The bug involves a legacy Flask-based API server component “src/praisonai/api_server.py” in PraisonAI that shipped with authentication disabled by default. The issue affects versions 2.5.6 to 4.6.33, and has been fixed in version 4.6.34.
“Authentication disabled by default in a development-grade API server is a known anti-pattern, and its blast radius is bounded by whatever permissions the operator gave the agent workflow,” said Trey Ford, chief strategy and trust officer at Bugcrowd. “Any organization that accelerated AI agent adoption without auditing network binding, authentication defaults, and credential exposure in agent configuration files now faces risk it likely hasn’t quantified.”
Sysdig said a GitHub advisory was published around 13:56 UTC on May 11, and probing started at 17:40 UTC.
Authentication was disabled by default
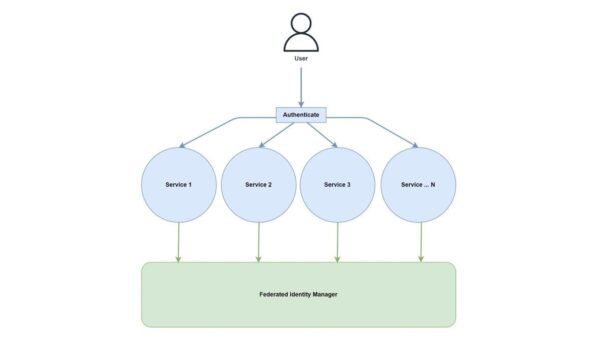
Sysdig said the vulnerable component was a PraisonAI legacy API server, where authentication protections were effectively disabled by design. The researchers noted that any reachable caller could interact with agent workflows without valid tokens.