A newly exposed global malware campaign reveals how PXA Stealer has been wielded by Vietnam‑linked actors to siphon sensitive data from professionals across multiple countries using trusted platforms like LinkedIn. First documented in late 2024, this campaign has evolved into a new threat that leverages social engineering, advanced payload delivery, and stealthy execution to outmaneuver traditional defenses.
Cybersecurity researchers at Cyble have mapped the multi‑stage attack chain, attributing the PXA Stealer campaign with a high degree of confidence to cybercriminals operating from Vietnam. These Vietnam‑linked actors target job seekers and professionals in India, Bangladesh, Sweden, the Netherlands, and the United States, exploiting trust in professional outreach to propagate their malware at scale.
Fake Recruiter Messages Feed the PXA Stealer Infection Chain
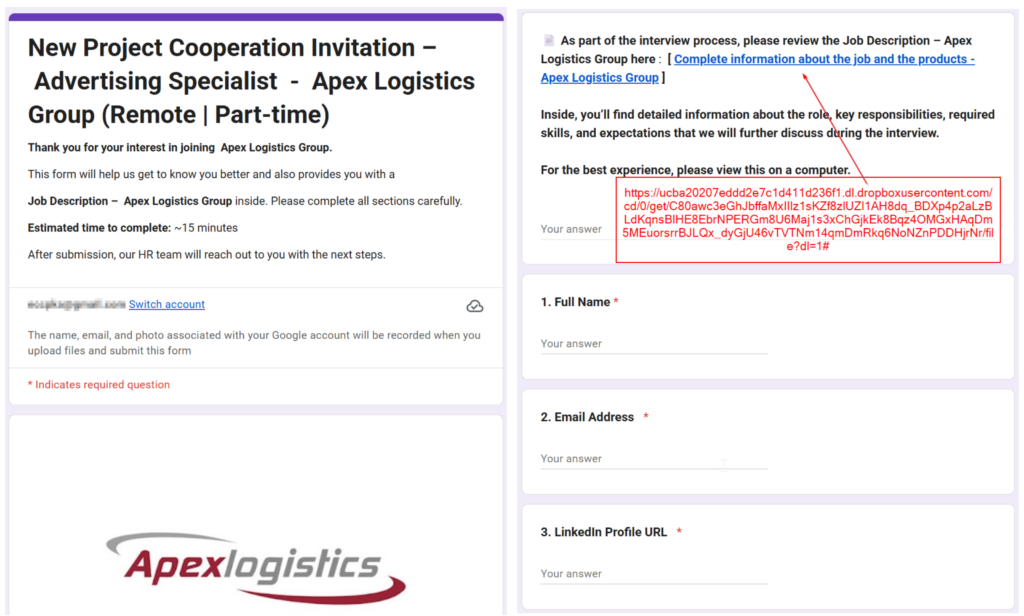
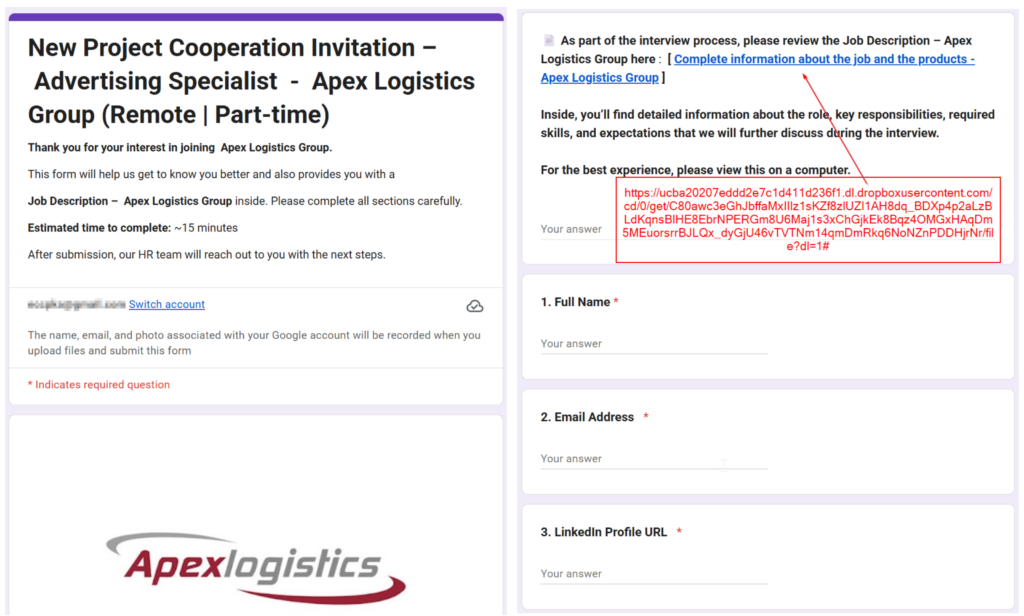
The campaign typically begins with a direct message on LinkedIn from a compromised or spoofed account posing as a recruiter from a fictitious company called Apex Logistics Group. The message promises remote work opportunities in fields like digital marketing and invites targets to engage, a tactic that lowers suspicion due to the context of career networking.
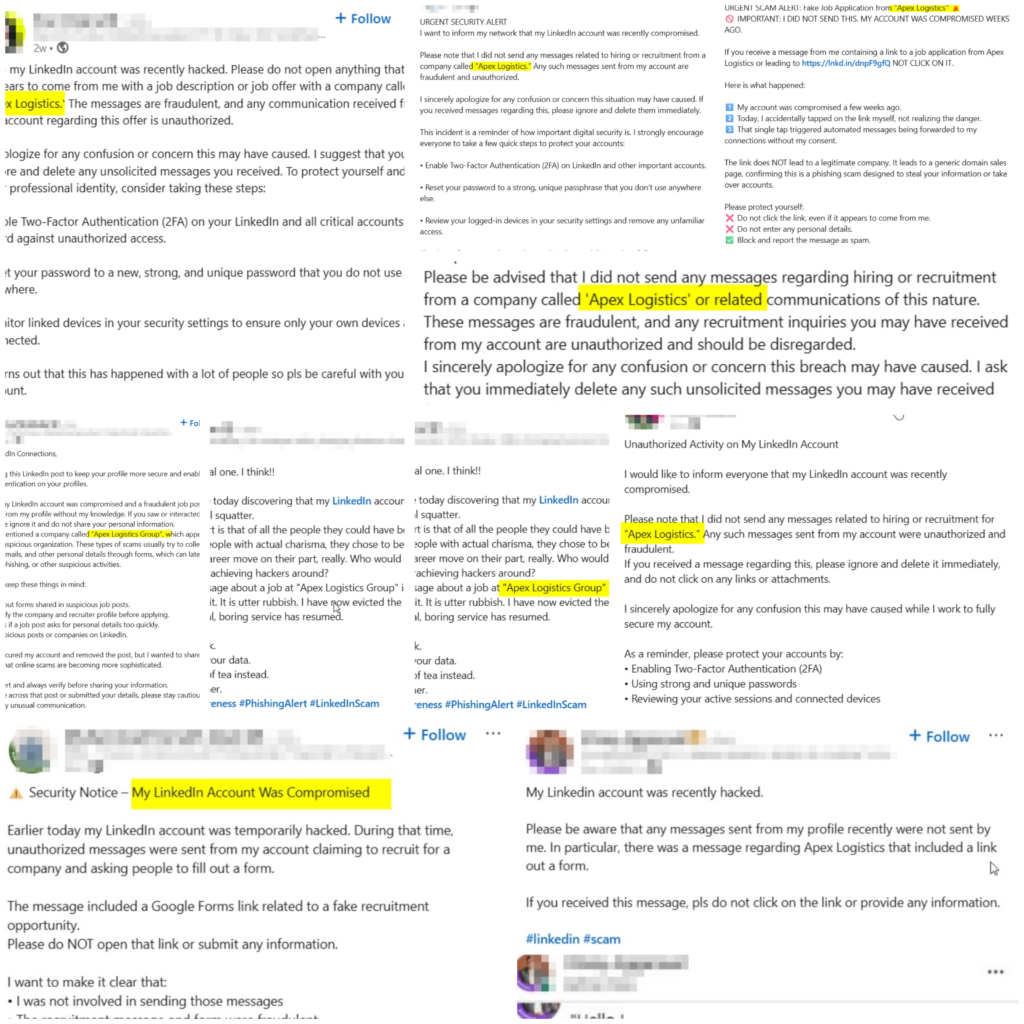
Once interest is established, victims are asked to complete a Google Form and then redirected through a URL shortener to a Zip archive hosted on cloud storage. That file, labeled with a job‑related name, contains a seemingly legitimate Microsoft Word executable that initiates a DLL sideloading sequence once launched. This technique allows the malicious DLL payload to load under the guise of a trusted binary.
To bypass detection, threat actors inflate the size of the malicious DLL to roughly 100 MB, far larger than its legitimate counterpart. A form of binary padding designed to slip past scanners that skip oversized files. The final payload, PXA Stealer, then executes solely in memory, leaving minimal traces on disk and greatly impeding forensic analysis.
Data Exfiltration and Persistence
Once active on a victim machine, PXA Stealer focuses on harvesting a wide range of sensitive materials. This includes:


- Stored browser login credentials, cookies, and session tokens
- Cryptocurrency wallet identifiers and associated applications
- Two‑factor authentication secrets from authenticator apps
- Desktop and email client credentials
Persistence is established through scheduled tasks disguised as standard system updates, such as a bogus Microsoft Edge update, blending malicious activity into normal operations. Exfiltration of stolen data is facilitated through encrypted Telegram channels and hidden command‑and‑control infrastructure that can masquerade as legitimate services to avoid detection.
A New Kind of Threat
Technical analysis of the PXA Stealer campaign shows a steady increase in technical activities since cybersecurity researchers first documented the strain in November 2024. Originally a Python‑based infostealer, the malware has since developed multi‑layer obfuscation, memory‑only execution, and dynamic command infrastructure retrieval via Telegram, traits which complicate detection and mitigation.
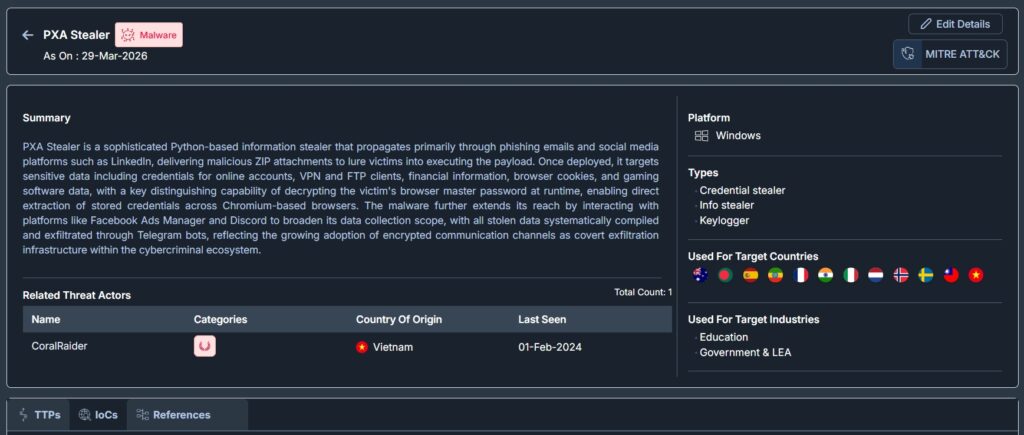
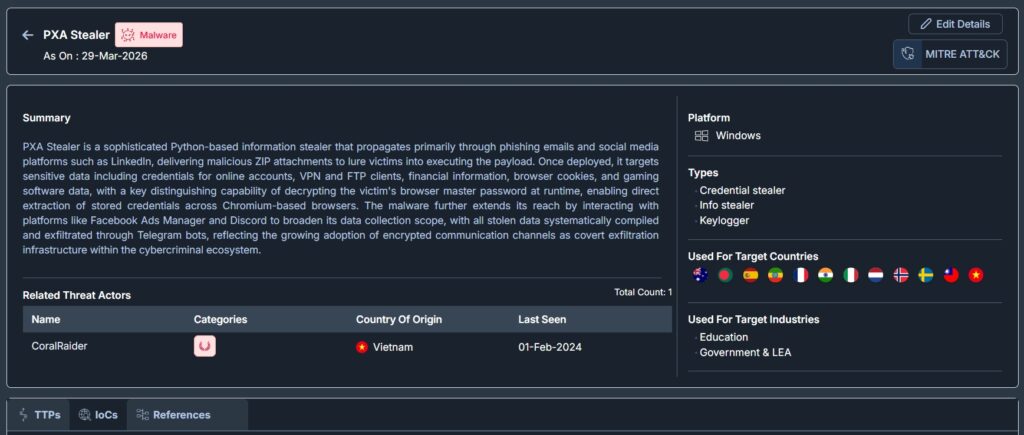
Through 2025, researchers observed expanded sideloading vehicles, enhanced obfuscation layers, and broader geographic targeting. By late 2025 and into early 2026, the attackers diversified the social engineering lures beyond job offers to include invitations to view tax forms, legal documents, and software installers. These hooks are designed to increase the likelihood of user interaction, particularly among the professionals most likely to be active on LinkedIn.
Global Scale and Consequences
Investigations by multiple cybersecurity groups indicate that PXA Stealer has already impacted tens of thousands of devices worldwide, with estimates of over 94,000 infected systems spanning Europe, Asia, and the Americas. The theft of credentials, including hundreds of thousands of unique passwords and millions of browser cookies, has enabled criminal actors to bypass multi‑factor authentication and escalate unauthorized access quickly.
Victims range from individual job seekers to organizations in heavily regulated sectors. Companies face not only immediate compromise of systems and accounts but also longer‑term risks, including Business Email Compromise, regulatory breaches under frameworks like GDPR, and reputational harm if employee or customer data is misused.
The PXA Stealer campaign shows how Vietnam‑linked actors exploit LinkedIn and fake recruiters like Apex Logistics Group to steal credentials, crypto wallets, and sensitive data. Organizations need vigilant defenses, including employee training, endpoint protection, MFA, and monitoring for unusual activity. Cyble offers AI-powered threat intelligence that predicts, detects, and neutralizes such attacks in real time. Schedule a demo to see how Cyble protects against threats like PXA Stealer.