The Qilin ransomware group has developed a highly sophisticated infection chain that targets and disables over 300 endpoint detection and response (EDR) solutions.
As defenders improve behavioral detection capabilities, attackers are increasingly targeting the defense layer itself during the early stages of a breach.
By deploying a malicious “msimg32.dll” file, attackers can bypass traditional antivirus defenses and execute their payloads entirely in memory.
The Initial Infection
The attack begins when a legitimate application inadvertently side-loads the malicious “msimg32.dll” file instead of the genuine Windows system library.
To avoid raising immediate suspicion, this rogue DLL forwards all normal application requests back to the real library located in the Windows directory.
Once successfully loaded, the malware triggers its hidden payload directly from its initialization function to launch a complex evasion process.
The malware uses a custom loader designed to suppress security event logging and neutralize standard user-mode hooks.
It relies heavily on structured exception handling (SEH) and vectored exception handling (VEH) to obscure its execution flow and conceal its activity from basic scans.
Furthermore, the loader uses a specialized scanning technique to find clean system calls, entirely bypassing any behavioral monitoring established by local EDR software.
Before executing its final payload, the malware checks the compromised system’s language settings to perform basic geo-fencing.
If it detects languages commonly used in post-Soviet countries, the process intentionally crashes to avoid infecting those specific systems.
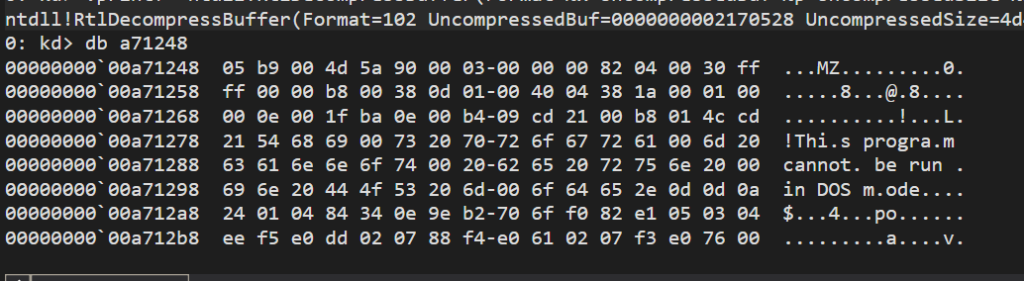
The payload is then decrypted and mapped directly into the system’s memory using shared views, ensuring that the EDR killer never touches the hard drive in an unencrypted state.
Malicious Kernel Drivers
Once the final stage is active, the malware elevates its privileges to administrative levels. It then loads two distinct kernel-level helper drivers to dismantle the underlying security tools from the inside out.
Abusing legitimately signed drivers allows the malware to bypass strict Windows driver signature enforcements.
| Driver Name | Original Source | Primary Malicious Function |
|---|---|---|
rwdrv.sys | Renamed “ThrottleStop.sys” | Grants direct read and write access to physical system memory . |
hlpdrv.sys | Custom malicious driver | Terminates protected EDR processes and disables antivirus software . |
Using the direct physical memory access provided by the first driver, the malware iterates through a hardcoded list of targeted EDR drivers.
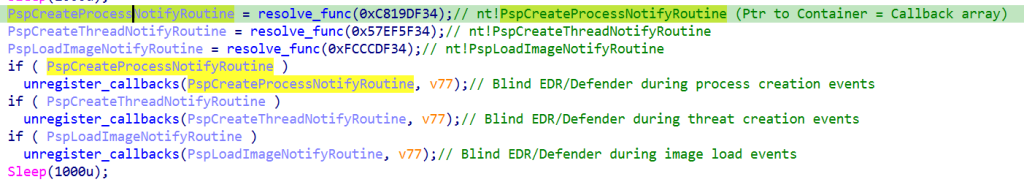
It systematically unregisters their monitoring callbacks for critical system events like process creation, thread creation, and image loading.
This effectively blinds the EDR tools at the kernel level before the second driver forcefully terminates their active background processes.
To cover its tracks, the malware temporarily disables Windows Code Integrity enforcement by overwriting specific kernel validation functions, as reported by Talos Intelligence.
During this vulnerability window, it freely modifies system structures without triggering fatal crashes or security alerts.
Once the EDR software is successfully neutralized, the malware restores these original integrity checks, reducing forensic traces and allowing the Qilin ransomware to proceed undetected.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.





